Tenable Makes Verizon DBIR Findings Actionable with SecurityCenter Continuous View™

Note: Tenable SecurityCenter is now Tenable.sc. To learn more about this application and its latest capabilities, visit the Tenable.sc web page.
The Verizon Data Breach Investigations Report (DBIR) is one the most widely read publications pertaining to data breaches and security trends. I outlined my top takeaways from the 2015 report in an earlier blog, Insights from the 2015 Verizon DBIR.
While the Verizon report provides great analysis on the top vulnerabilities and successful techniques used to compromise networks, many organizations fall short in identifying if they are already victims of a breach or are vulnerable to the attacks identified in the report. Why? Because organizations don’t have the time to manually extract data from different parts of the business and iteratively filter and convert the information into security monitoring policies and an actionable program. On the other hand, most security deployments are fragmented and lack easy-to-use dashboards to provide centralized visibility – until now.
Tenable’s SecurityCenter Continuous View now includes several DBIR dashboards to help you quickly discover if the top vulnerabilities identified in the Verizon DBIR are in your deployments
New SecurityCenter CV™ dashboards
Tenable’s SecurityCenter Continuous View™ (SecurityCenter CV) now includes several DBIR dashboards to help you quickly discover if the top vulnerabilities identified in the Verizon DBIR are in your deployments and if your organization is a victim of malware or advanced threats. The dashboards also help prioritize what’s relevant, whether your security investments are updated with the latest protection, and if remediation of vulnerabilities is occurring in a timely manner.
Presented as tables, indicators, graphs and charts, Tenable dashboards provide analysts and executives the visibility needed to detect, prioritize, and respond to key findings and recommendations from the Verizon DBIR.
Tenable offers five dashboards based on Verizon’s findings in the 2015 DBIR:
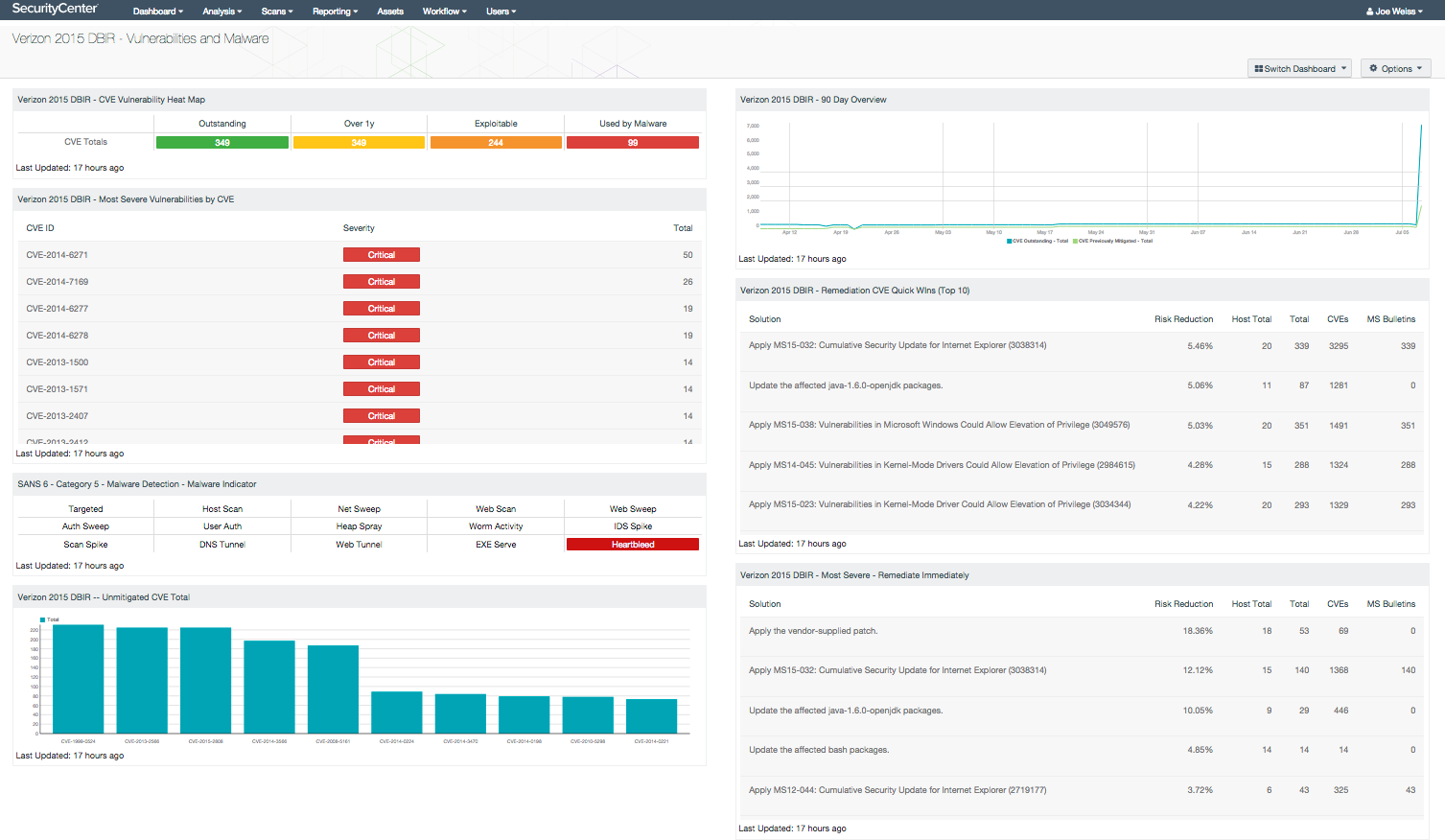
Vulnerabilities and Malware Collection
Identifies missing patches based on CVE identifiers and common malware indicators. Key components include: most severe vulnerabilities by CVE, most severe vulnerabilities to remediate immediately, heat map with hierarchy of CVE described in the DBIR, unmitigated CVEs, quick win remediations for the Top 10 CVEs, SANS 6 - Category 5 - malware detection - malware indicator, and 90-day trend of patching for the CVEs.
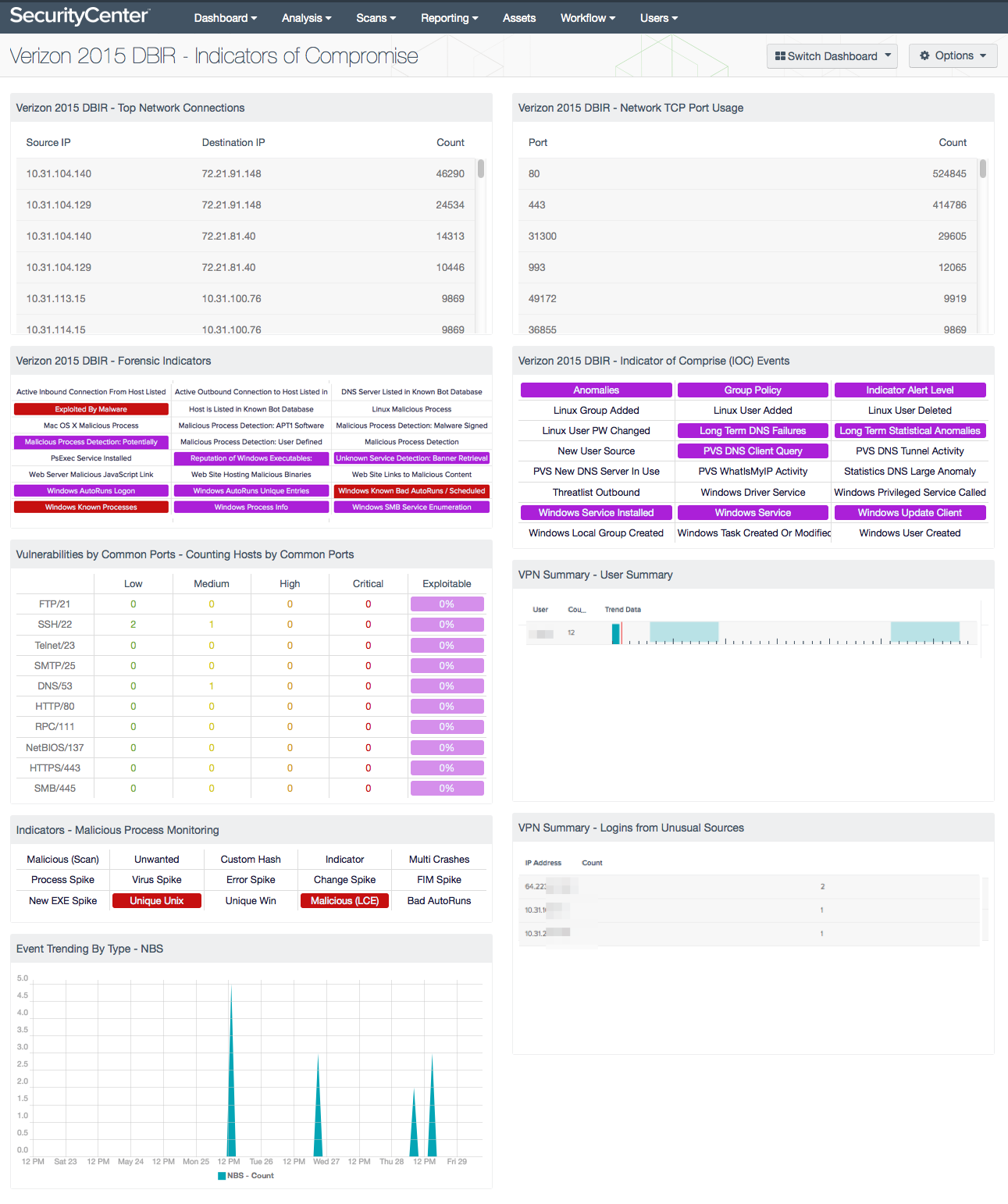
Indicators of Compromise
Consists of virus signatures, specific traffic patterns, specific IP addresses, malware, specific URLs or domains of known illicit activity. The dashboard components display threat indicators such as autorun monitoring, suspicious process detection, botnet tracking, malicious URL tracking, and event based threatlist monitoring.
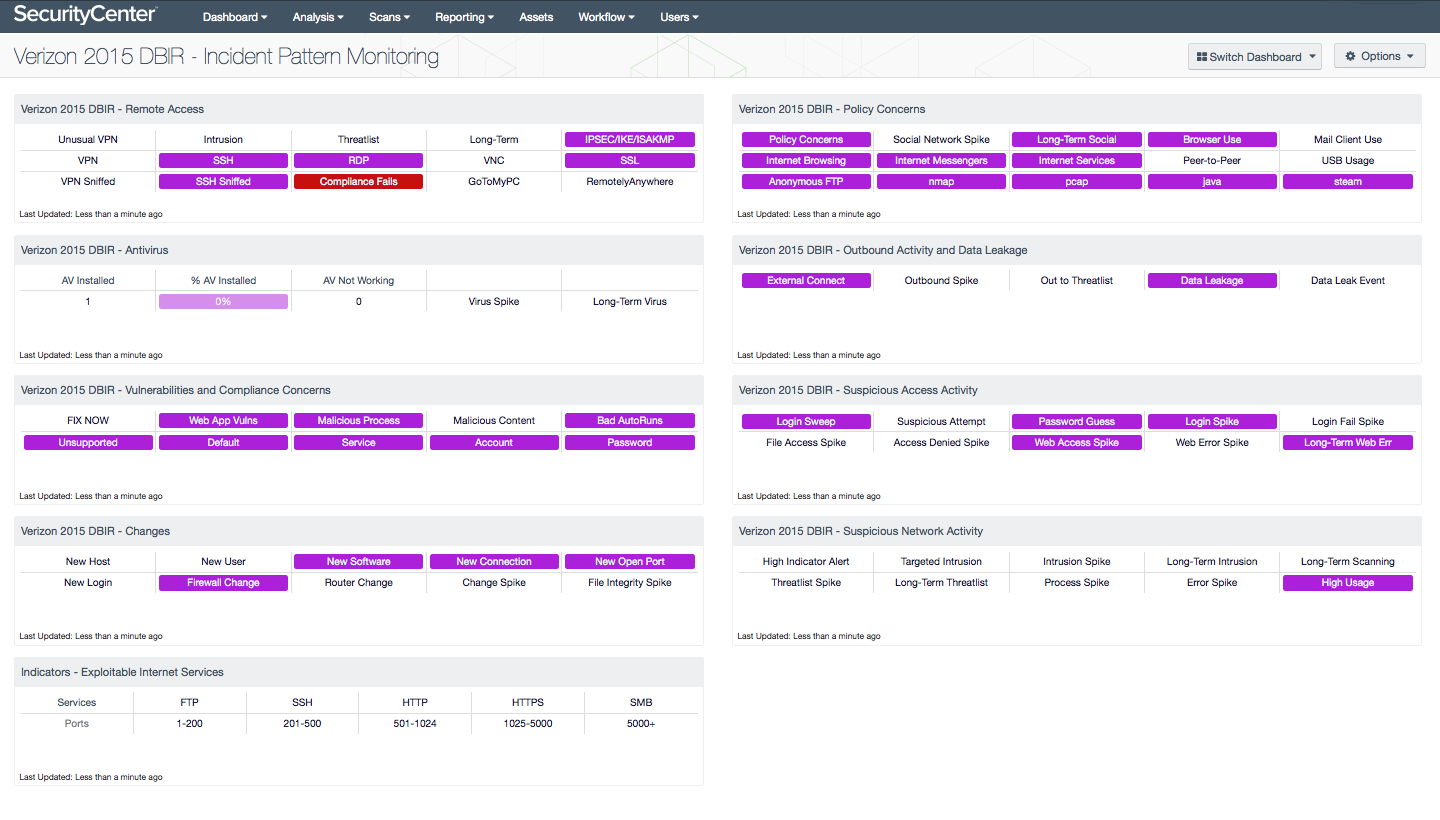
Incident Pattern Monitoring
This dashboard includes monitoring of remote access, preventing web browsing, e-mail, social network activity and more on point-of-sale (POS) systems, deploying an anti-virus (AV) solution, monitoring outbound connections, watching for data exfiltration, monitoring changes, and looking for suspicious user and network activity.
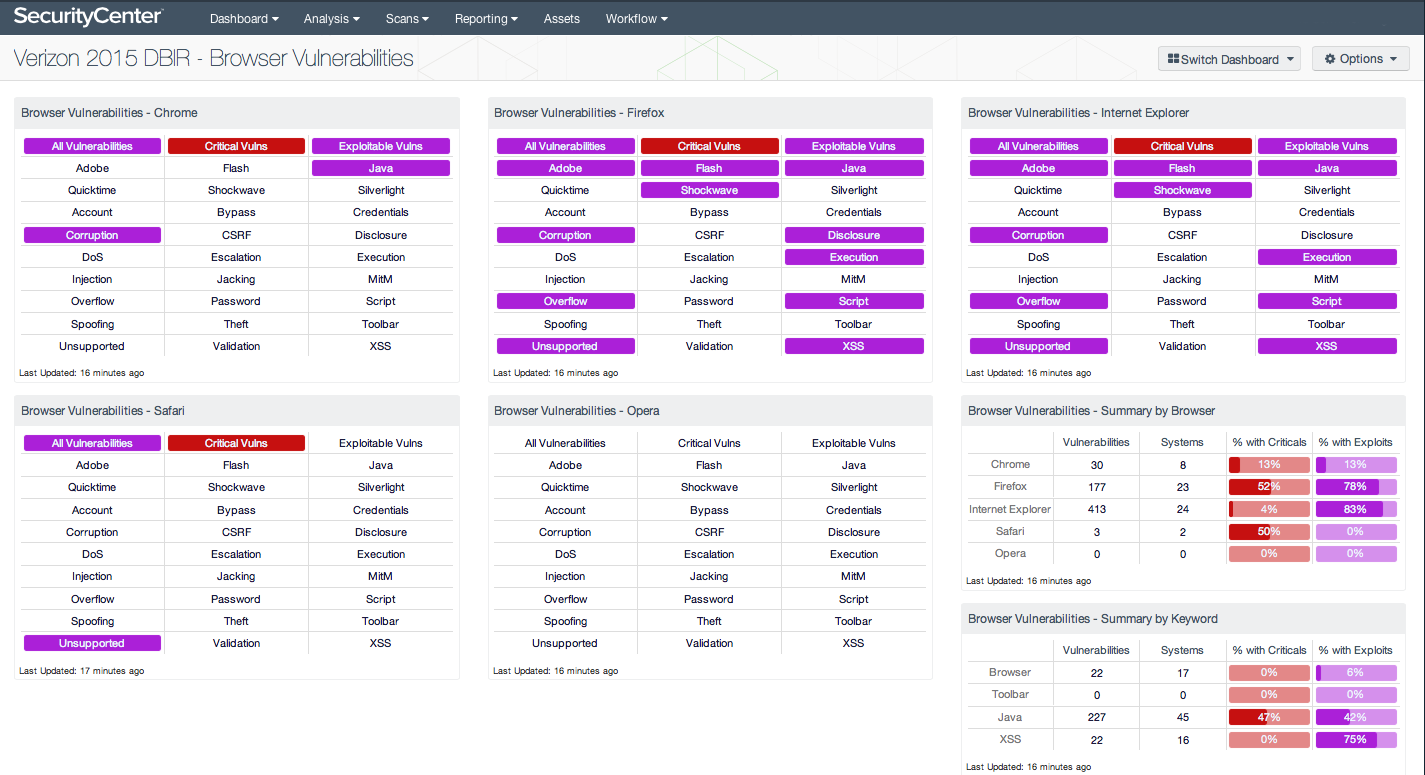
Browser Vulnerabilities
Identifies unauthorized and vulnerable web browsers that could allow compromise. This dashboard identifies vulnerability information for the major web browsers: Chrome, Firefox, Internet Explorer, Safari, and Opera. The information can assist in reducing your chances of a data breach by eliminating unauthorized web browsers (e.g., from critical servers and point-of-sale systems), patching browser vulnerabilities, and disabling vulnerable plugins (e.g., Java).
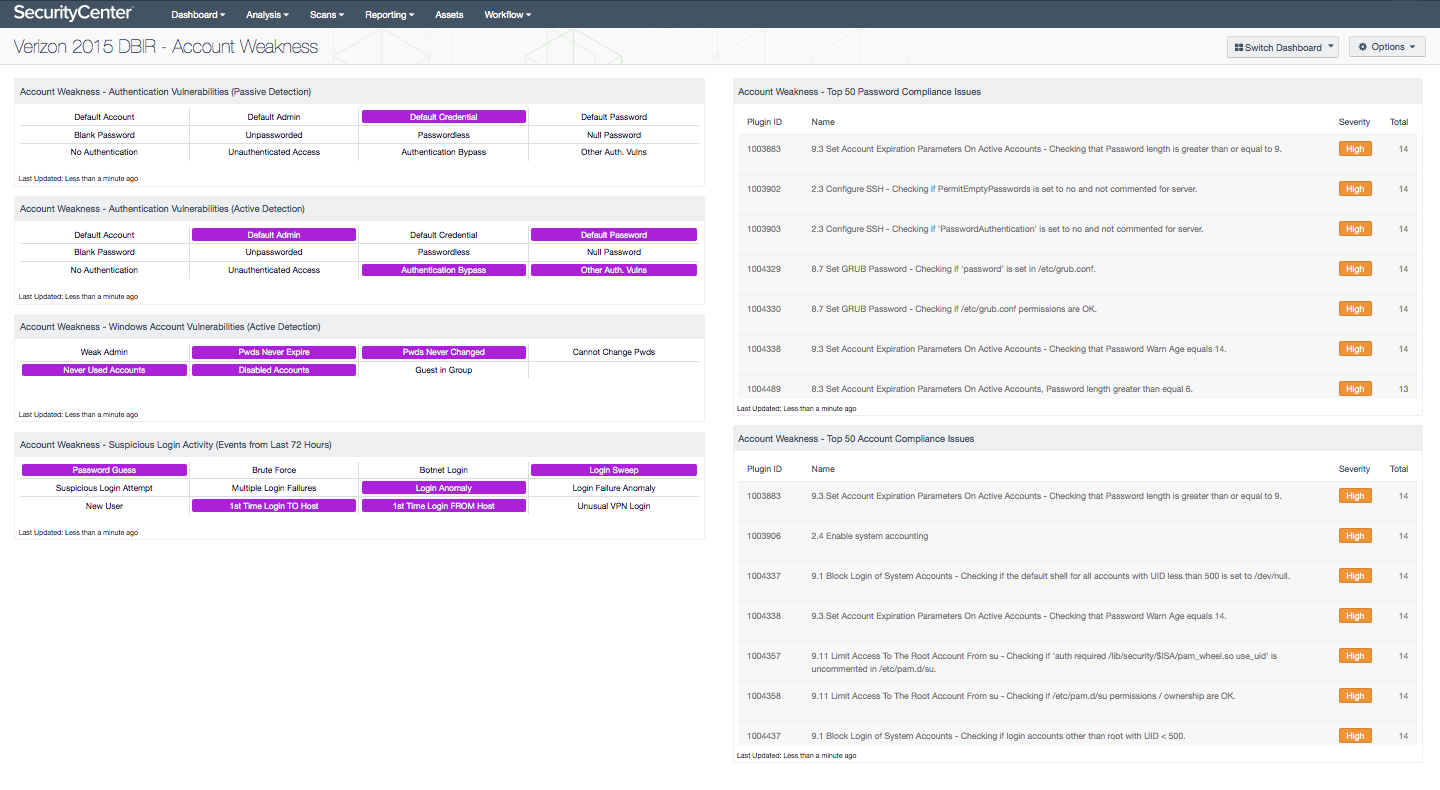
Account Weakness
This dashboard presents vulnerabilities related to accounts and credentials. These vulnerabilities include default accounts, blank passwords, vulnerabilities that allow bypassing authentication, insecure and non-compliant account and password settings, and more. Potentially suspicious login activity is also noted to bring attention to accounts that are more threatened and require greater protection. This information can help reduce your chance of a data breach by eliminating weak passwords, default accounts, and lax policies.
More resources
For more information:
- For an overview of the DBIR dashboards, review the Verizon DBIR Solution Brief.
- Download the whitepaper, Tenable’s Continuous Network Monitoring and the Verizon DBIR, to learn more about using SecurityCenter CV and applying the Verizon DBIR findings to improve your security programs.
- For a demo of SecurityCenter CV and the Verizon DBIR dashboards, please contact us
Learn more
- Announcements
- Dashboards
- Research Reports
- SecurityCenter



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success