Tenable vs. other OT security vendors
Fortify your OT security posture
Don’t let fragmented security solutions from multiple vendors weaken your cyber defenses. Tenable’s integrated approach to exposure management combines comprehensive visibility with industry-leading vulnerability management capabilities to help break down silos and simplify security across IT, OT and IoT for a complete picture of risk.
Why Tenable
See Tenable in action
Want to see how Tenable can help your team find and fix critical cyber weaknesses that put your business at risk? Complete this form to get a custom quote or demo.
Thank you
You should receive a confirmation email shortly and one of our representatives will be in touch.
Form ID: 13427
Form Name: why-compare-form
Form Class: c-form c-form--request-demo c-form--mkto js-mkto-no-css js-form-hanging-label
Form Wrapper ID: why-compare-form-form-wrapper
Confirmation Class: why-compare-form-confirmform-modal
Simulate Success
Why customers choose Tenable over other OT security vendors
Coverage
Coverage and accuracy
Tenable leads in CVE coverage, zero-day research and vulnerability management. Our solutions are powered by extensive vulnerability coverage and intelligence, with regular updates and rapid response to high-profile issues.
Explore Tenable vulnerability coverage and zero-day research at tenable.com/plugins.
#1 in CVE coverage
#1 in zero-day research 1
#1 in vulnerability management
122K K
Vulnerabilities assessed with 332,000+ plugins
799
Vulnerabilities disclosed by Tenable Research
< 24 hrs
Median time for coverage of high profile issues
Visibility
Unmatched OT/IT/IoT visibility
Tenable’s patented hybrid discovery combines active and passive scanning to deliver full visibility of your attack surface and proactively close risk exposure.
-
Active querying: Get in-depth vulnerability insights and reduce false positives by safely querying OT systems using native protocols to check for misconfigurations, outdated firmware and more.
-
Passive monitoring: Continuously analyze network traffic with passive monitoring capabilities for real-time updates on new devices, applications and vulnerabilities.
This unique combination helps uncover hidden assets and vulnerabilities that passive monitoring often misses, including IoT devices using application-based scanning capabilities to discover asset details and communication paths.
Other OT vendors rely on SNMP-based crawlers and supported query protocols (one-size-fits-all approach) and lack extensive interlocks and overrides to safely query OT devices.
“Tenable’s track record in high-risk environments was a big factor, especially active query. Everyone else can do passive, but we weren’t looking at passive, because otherwise, we could continue with the solution we had in place.”
North American railroad company
Exposure
Exposure management from identity to on-prem to OT
The Tenable One Exposure Management Platform provides unified visibility across cloud, identities, on-prem and OT/IoT systems in a single solution. It offers granular vulnerability intelligence, tracks vulnerability history and enables risk remediation tracking with a risk-based approach.
An extensive library of dashboards and reports help facilitate communication with stakeholders such as senior leaders, IT and security teams, auditors, insurance providers and board members.
“When it comes to operational technology …that's where Tenable wins.”
Vulnerability management architect, German manufacturing company
Many vendors focus on OT security alone and lack an integrated exposure management platform for comprehensive visibility into risk across your attack surface, leaving your organization with disparate tools and without a single source of truth.
Siloed OT point solutions do not consider enterprise-wide context, such as asset criticality on your network, internal and peer benchmarking, assessment or remediation maturity.
Many OT vendors lack integrated support for Active Directory and Entra ID, which limits identity and access control.
Vulnerability
Vulnerability analytics
Tenable solutions consider 150+ factors to provide accurate risk assessments and actionable insights into cyber risk for converged OT/IT environments. Tenable Research, combined with more than 50 trillion data points, fuels our Vulnerability Intelligence. This powerful combination gives you the context you need around business urgency and risk, helping teams clearly identify risks and prioritize remediation efforts.
Many vendors lack advanced, time-tested vulnerability priority ratings (VPR), resulting in inaccurate and missing results. They can’t match the extensive research capabilities Tenable has developed over decades.
Lack of configurable dashboards and less advanced reporting capabilities.
$ 153 M
invested in research and development.
150 +
factors to determine a vulnerability’s risk level and identify those with the highest chance of exploitation.
VPR
extended prioritization capabilities from cloud to traditional on-premises assets.
Scalable
Scalable licensing and deployment model
With Tenable's asset-based licensing model, only pay for what you need—no surprises, just clarity and control. Our licensing model scales with your operations, making it easy to manage your security investments as your business grows. Whether you’re adding new plant sites, expanding production lines or opening new data centers, Tenable One OT Exposure ensures your cybersecurity investments align with your evolving needs.
And, because no two organizations are the same, Tenable offers flexible deployment options — on-prem or virtual — ensuring your OT security fits seamlessly into your existing infrastructure.
Complex procurement processes make budgeting and scaling difficult.
“The way Tenable licenses [its solutions] is better compared to Nozomi. . . Nozomi was also more confusing and Tenable was clear, so that was a differentiator.”
North American energy company
Compare Tenable to other OT security vendors
Recognized as a leader in exposure management by industry analysts
More awards and recognitions
Tenable is a Leader in the 2025 Gartner® Magic Quadrant™ for Exposure Assessment Platforms
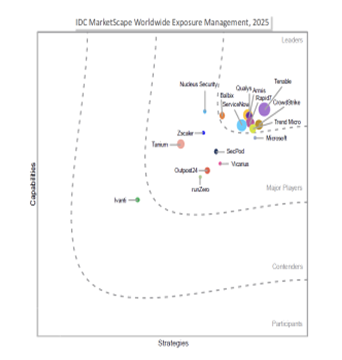
Tenable named a leader in the IDC MarketScape Worldwide Exposure Management 2025 Vendor Assessment

Tenable named a leader in The Forrester Wave™: Unified Vulnerability Management Solutions, Q3 2025
Related resources
See
Tenable
in action
See how Tenable can give your team the clarity to fix what matters, at the speed of AI.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success