Tenable versus CrowdStrike Falcon Exposure Management
Proactively secure your attack surface — not just your endpoints
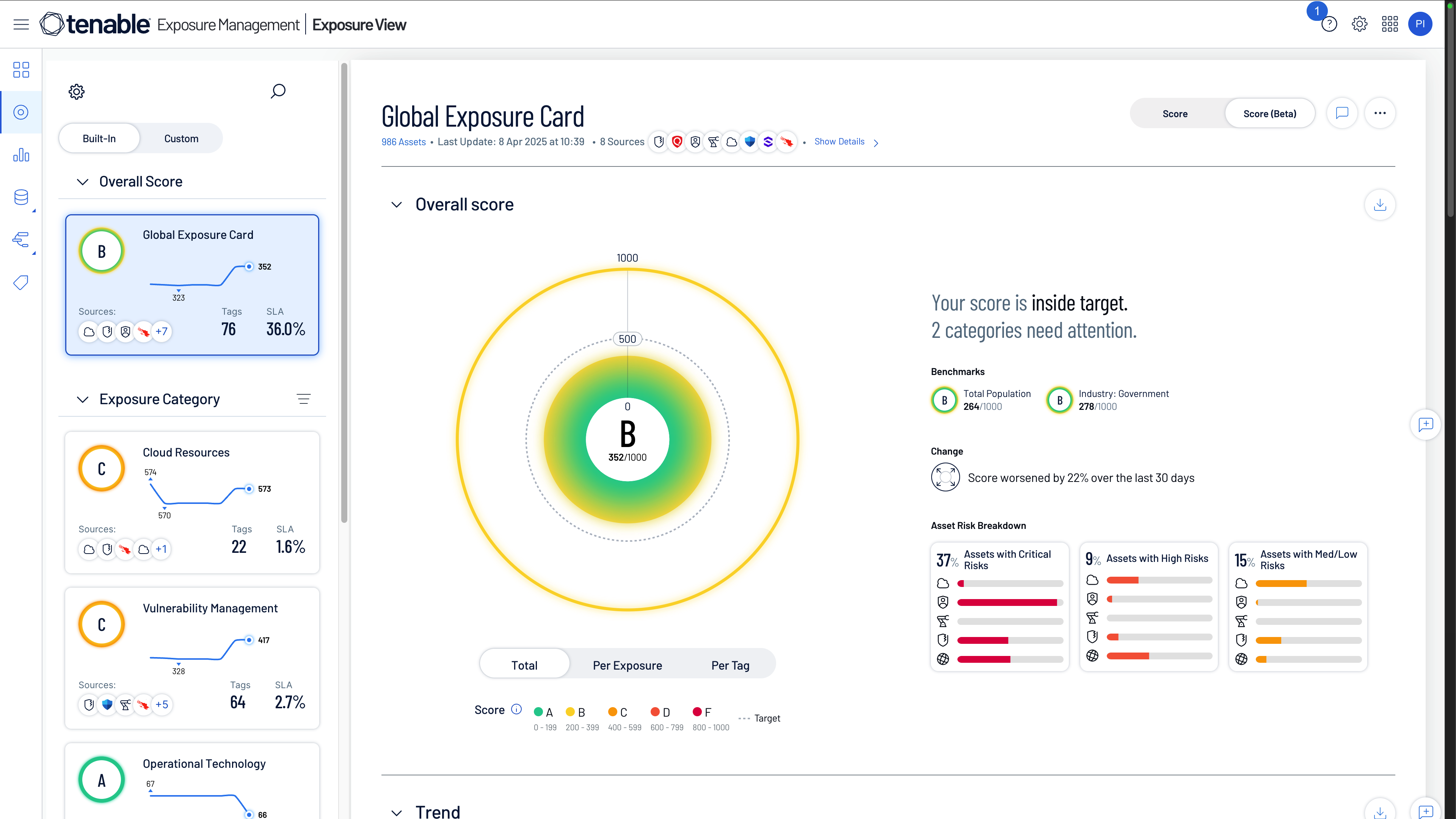
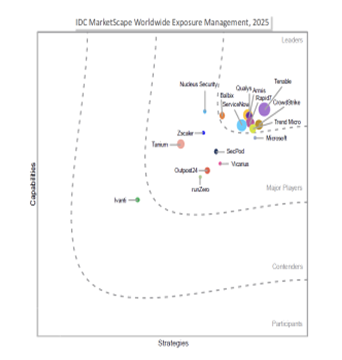
Tenable has defined proactive security with best-in-class vulnerability management for more than two decades. And now, we are leading the way to exposure management. While CrowdStrike specializes in reactive incident response with endpoint detection and response (EDR), we enable security leaders to identify, prioritize and mitigate cyber risks effectively before attackers can exploit them.
Why Tenable
See Tenable in action
Want to see how Tenable can help your team find and fix critical cyber weaknesses that put your business at risk? Complete this form to get a custom quote or demo.
Form ID: 13427
Form Name: why-compare-form
Form Class: c-form c-form--request-demo c-form--mkto js-mkto-no-css js-form-hanging-label
Form Wrapper ID: why-compare-form-form-wrapper
Confirmation Class: why-compare-form-confirmform-modal
Simulate Success
Why customers choose Tenable over CrowdStrike
Compare Tenable Exposure Management to CrowdStrike Falcon Exposure Management
Lacks comprehensive network scanning, web app security (WAS), identity data and holistic context beyond endpoints



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success