New Nessus Configuration Checks Available for Citrix XenServer
A new compliance plugin is now available for Nessus customers to audit the configuration settings of Citrix XenServer. XenServer is an open-source virtualization platform used to manage cloud, server, and desktop virtual infrastructures. This new Nessus functionality allows customers to harden the virtualization layer of their infrastructure, an important component in an organization's security as so many systems are able to run on the virtual platform.
Given the similarities between XenServer and UNIX operating systems, the new XenServer compliance plugin is an extension of the UNIX compliance checks.
Scan Requirements
To begin auditing the security of your Citrix XenServer instances, you will need the following:
rootlevel credentials for XenServer host(s)- SSH access to the targets
- A Nessus policy with plugin ID #69512 (Citrix XenServer Compliance Checks) enabled
- The .audit file - Customers may obtain the required audit file for XenServer systems on the Tenable Support Portal (filename is TNS_BestPractice_XenServer.audit)
What Is Nessus Auditing?
A hardening guide for XenServer is not available from Citrix. Tenable created our own best practice audit, based on available industry standard best practices guides. The XenServer audit covers items such as firewall policy, undesired services, and other best-practice recommendations (such as passwords stored in clear-text). The XenServer .audit file also includes the ability to audit the installed patches on the target(s), offering the addition of making certain all patches are installed. The highlight of the .audit file is the ability to obtain a list of running virtual machines, patches, storage repositories, and more.
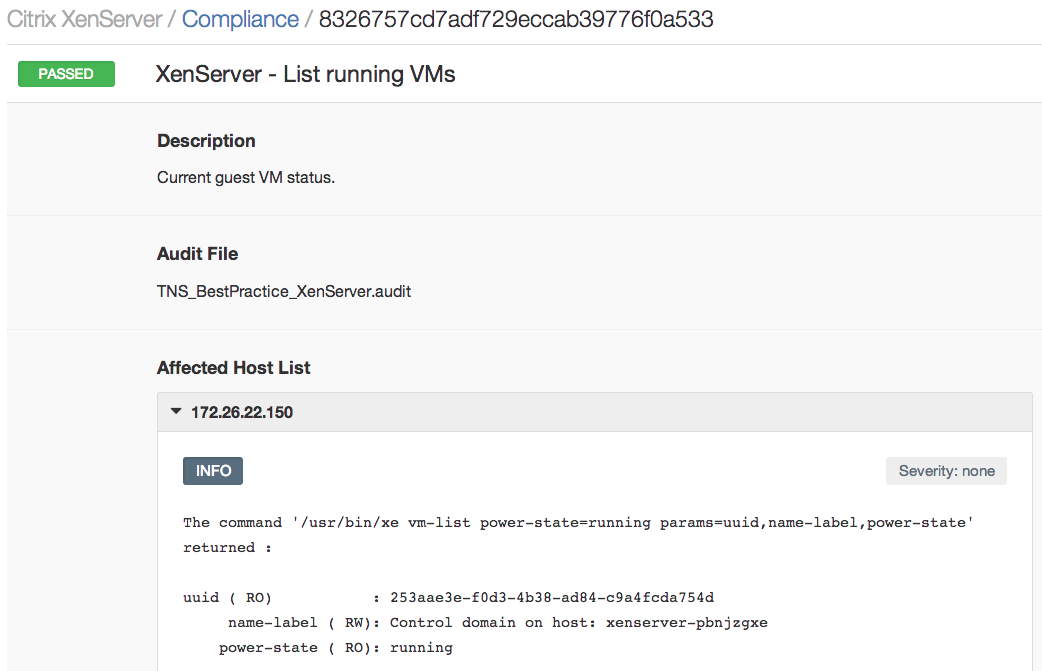
In the following screenshot, you can see a list of running virtual machines, useful for taking an inventory of all virtual systems.
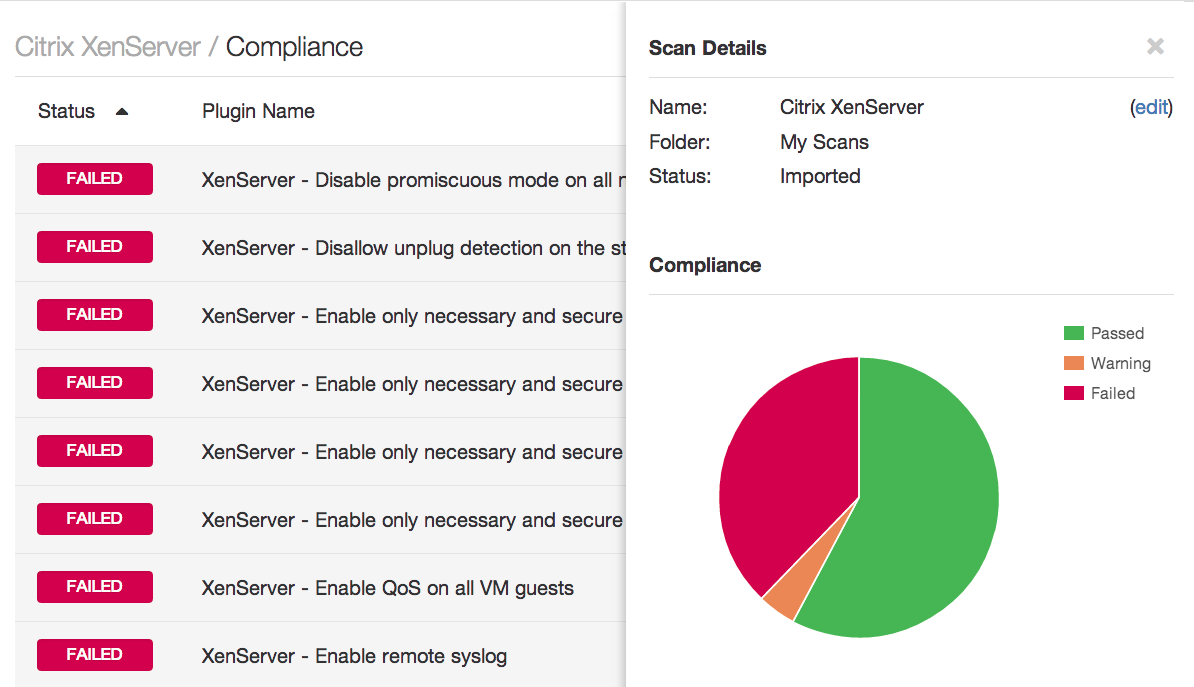
More sample results can be found below. Below, you can see the listing of compliance audit checks for all XenServers being audited. On the right, you see a pie chart depicting passed, failed, and warning-level alerts which can be viewed by clicking the "Scan details" link in the compliance results.
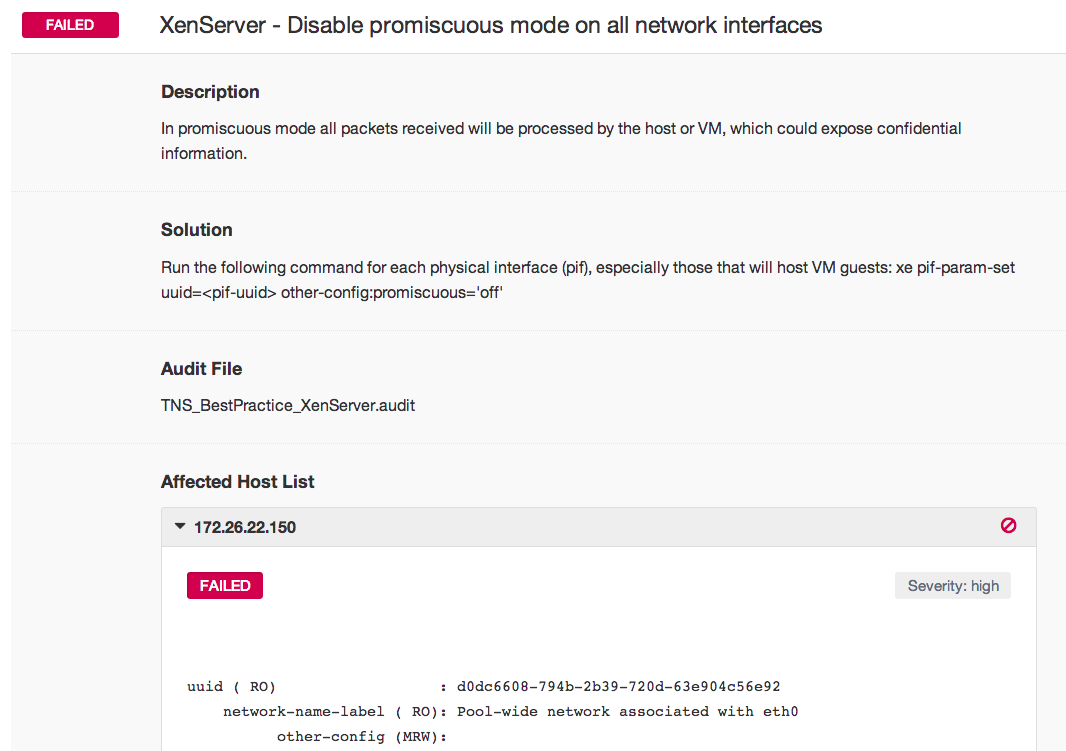
In the following screenshot, XenServer audit checks review the configuration of all interfaces and indicate a failed check for those in promiscuous mode.
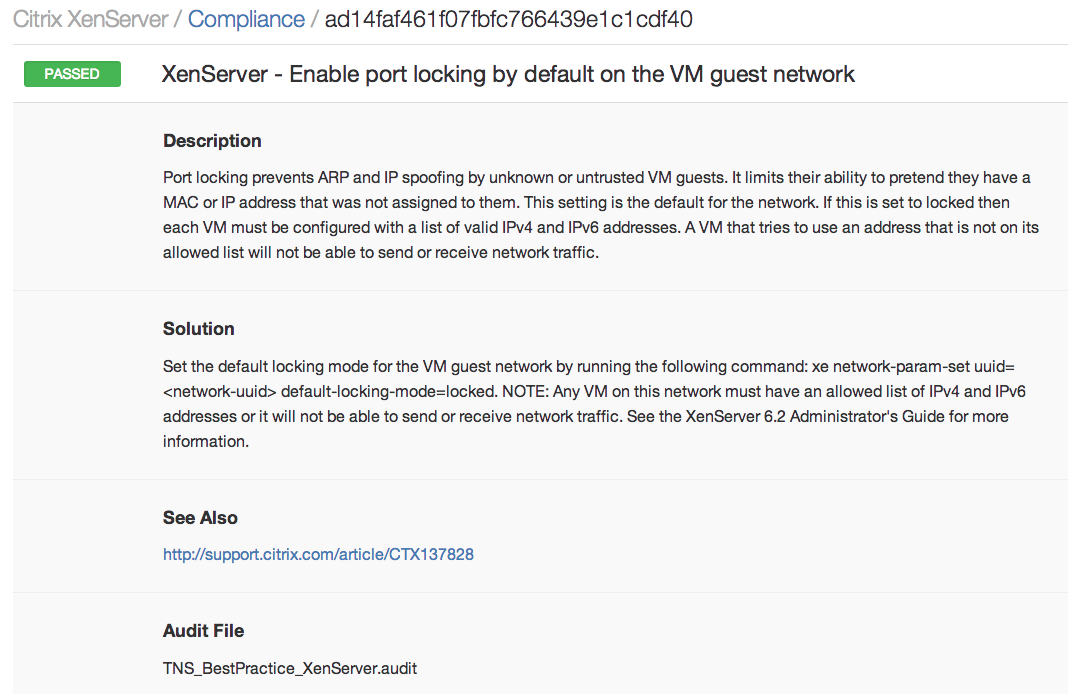
Further security measures available in XenServer's configuration include measures to prevent virtual machines from obtaining unauthorized IP addresses.
Conclusion
Nessus customers can download all the latest compliance checks from the Tenable Support Portal.
Auditing the configuration of XenServer instances further extends Nessus’ capabilities to help secure your company’s infrastructure. For further information about using Nessus to audit your network, security, or virtual infrastructure, view the following posts:
- Nessus Helps Harden FireEye Appliances
- Nessus Audits HP ProCurve Routers
- Nessus Secures NetApp Data ONTAP
- Nessus VMware vSphere/vCenter Audits Available
- Nessus Audits Palo Alto Networks PAN-OS Configurations
- Configuration Auditing Cisco Nexus Operating System (NX-OS) with Nessus
- Nessus Compliance Checks Available for Check Point GAiA
- Nessus Audits Juniper Junos Configuration
- Nessus Cisco Compliance Checks
If you like this feature and plan to use it, please leave us a comment!
Learn more
- Nessus
- Plugins
- Standards
- Virtualization
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success