Nessus Now Audits Palo Alto Networks PAN-OS Configurations
Introduction
In recent years, Palo Alto firewalls have gained popularity within enterprise networks. Tenable Nessus ProfessionalFeed® customers can now audit the configuration of PAN-OS™-based Palo Alto Networks firewalls. Nessus can audit the firewall operational configurations and allow Palo Alto firewall reports to be embedded into Nessus reports.
Nessus communicates with the Palo Alto XML API to access the configuration and report data. The web interface must be enabled (either HTTP or HTTPS) on the firewall. Nessus requires credentials to the devices being audited; Superuser or Superuser (readonly) accounts for PAN-OS less than or equal to version 4.1.0 and Superuser admins on PAN-OS versions less than 4.1.0. The new Nessus plugins, Palo Alto Networks PAN-OS Compliance Checks (ID 64095) and Palo Alto Networks PAN-OS Settings (ID 64286), must also be enabled.
Verify Firewall Security Settings
Scanning firewalls across your network, while providing valuable data, doesn’t give you the full picture of vulnerabilities and exposures. Configuration auditing provides you with information that can only be obtained by logging into the system directly. For example, Nessus can check for operational settings on the firewall, such as whether or not the HTTP management service has been disabled, as shown below.
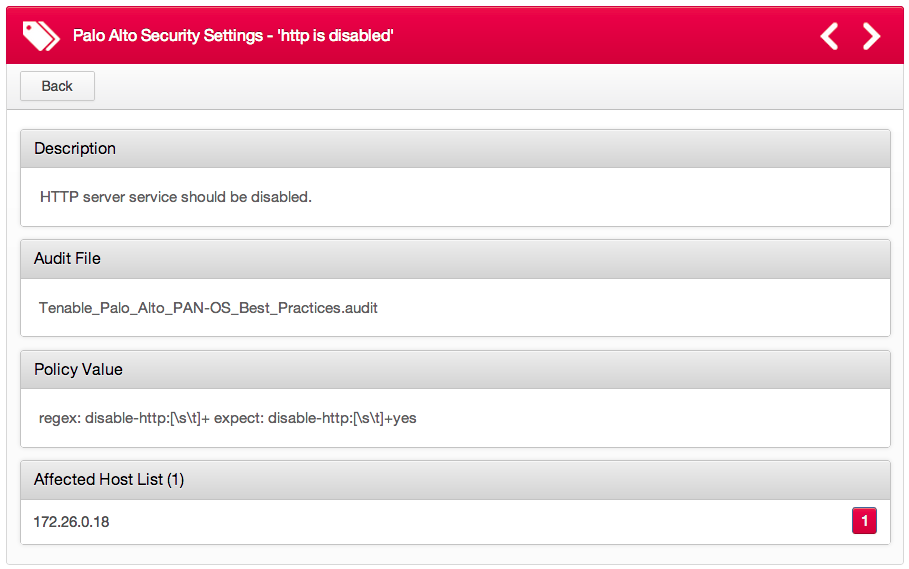
Auditing the firewall management settings allows you to harden the firewall itself. Ensuring all management protocols are using encryption is just one example. Several more checks exist for DNS, NTP, and update server settings.
For example, the Palo Alto firewall will implement anti-virus techniques that will "protect against malware embedded within compressed files and web content". In order to provide these services, the firewall must maintain a set of anti-virus policies. Using the configuration auditing now available in Nessus, you can detect when the anti-virus policies on your firewall are missing or out of date.
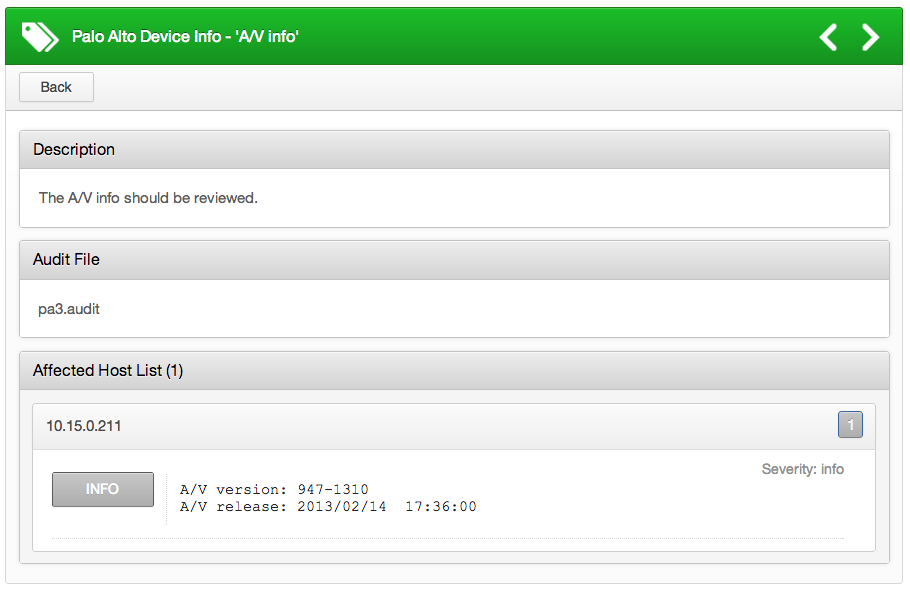
Nessus also includes checks to ensure the Palo Alto device is running the latest threat information, URL filtering, and global protect information.
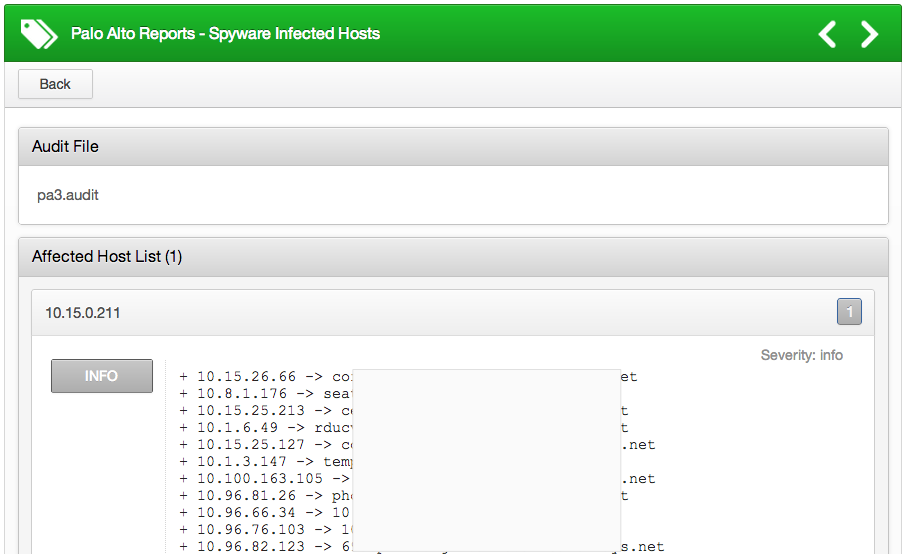
Auditing Palo Alto Reports
One of the nice features of a Palo Alto firewall is that it continuously profiles its network and generates 40+ pre-defined reports on a daily basis. Reports include Top Applications, Top Attackers, Spyware Infected Hosts, and more. Administrators can also generate dynamic reports for different time periods, for example, the last hour. Nessus can now directly query these Palo Alto reports and include them in a Nessus report. For example, here’s a sample of the "Spyware Infected Hosts" report:
Palo Alto firewalls also have application detection, collecting data on which users are using certain applications (e.g., Facebook). Here’s a sample of the “Top Applications” report:
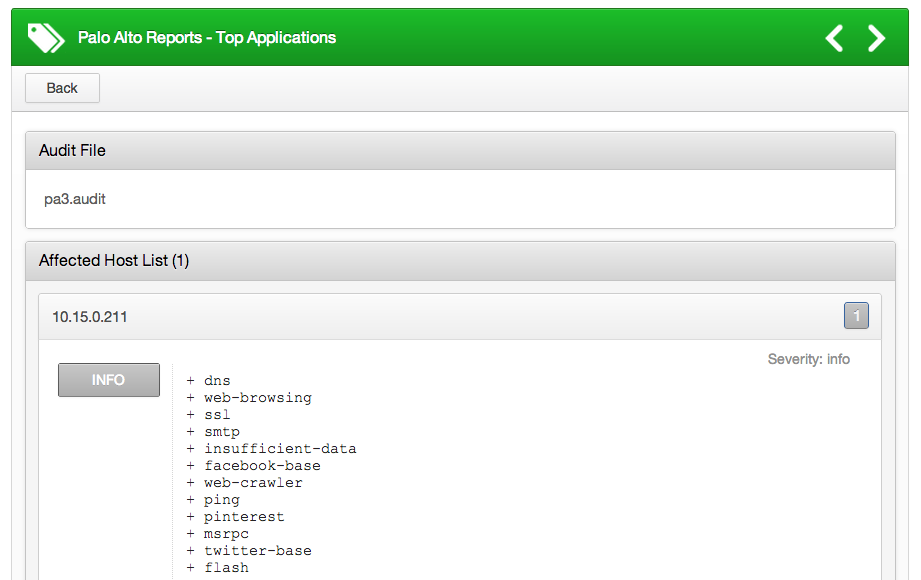
The compliance state of a check can be determined by comparing the output of the 'expect' or 'not_expect' keywords in the .audit file. For example, you can check the "Top Applications" and create a high-severity alert if "ping" is in the list of discovered applications.
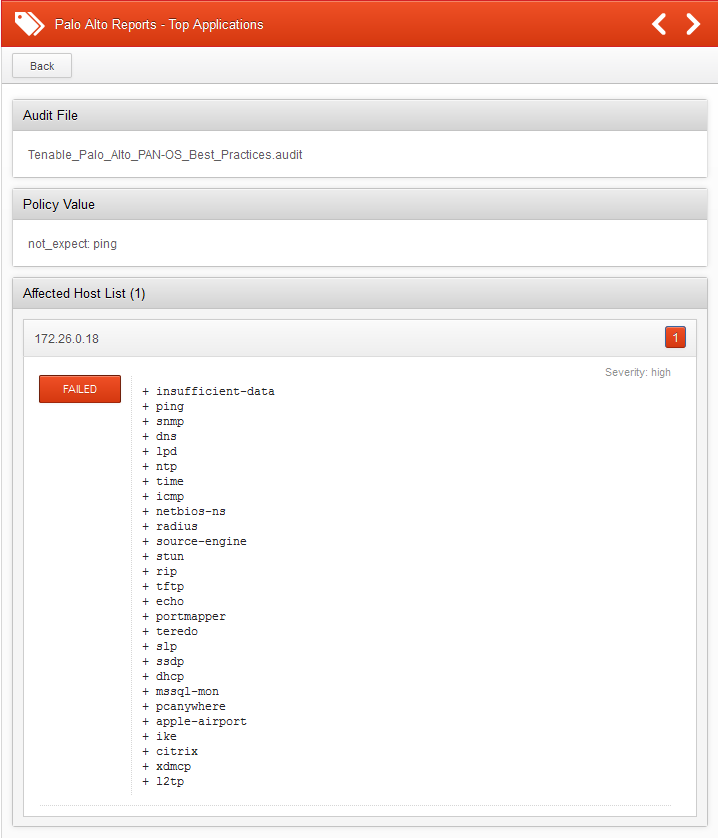
This feature has two benefits. First, users don't need to access different interfaces to get the same data. Second, you can now audit information from the report. For example, if you don’t want Facebook to be used on your network, then administrators can generate a failed report if Facebook appears on the “Top Applications” report.
Conclusion
Nessus ProfessionalFeed customers can download all the latest compliance checks from the Tenable Support Portal.
Auditing the configuration of Palo Alto firewalls further extends Nessus’ capabilities to help secure your company’s infrastructure. For further information about using Nessus to audit your router and firewall configurations, view the following posts:
- Configuration Auditing Cisco Nexus Operating System (NX-OS) with Nessus
- New Nessus Compliance Checks Available for Check Point GAiA
- Nessus Now Audits Juniper Junos Configuration
- Nessus Cisco Compliance Checks
If you like this feature and plan to use it, please leave us a comment!
- Nessus

