Nessus Now Secures NetApp Data ONTAP
The Nessus vulnerability scanner now performs configuration and compliance audits for NetApp storage devices.
Securing All Three Layers
Nessus recently added capabilities to perform configuration and compliance audits in two major areas of the enterprise. First, Tenable added the ability to audit enterprise Cisco networking equipment, namely Cisco's Nexus NX-OS. Then, we expanded and greatly enhanced support for auditing VMware vSphere and vCenter. Now, we've added support for auditing NetApp Data ONTAP storage devices. The new .audit is primarily based off the NetApp hardening guides (technical reports TR-3649 and TR-3996).
The ability to audit the environments mentioned above provides enterprises with the tools to manage configuration and compliance at the core of the enterprise. Namely, you can now control the security of the configurations in your virtualization platform, networking virtualization backbone, and storage environment.
I've often found that organizations lack focus when it comes to securing virtual infrastructure devices. In their defense, they're complicated to set up and maintain, and configuration and compliance auditing adds another layer of complexity by enforcing hardening standards. However, if an attacker were to gain access to these devices, it would be the equivalent of allowing them to enter the data center and access all of your systems directly. This is especially true with storage systems; a compromised storage controller gives an attacker direct access to all of your data. (However, you should be securing and hardening all three layers – virtualization, networking, and storage!)
For companies that need to adhere to strict compliance requirements with regards to data handling, data retention (e.g., e-mail), and data duplication (e.g., back-up), this is a big plus. With NetApp Data ONTAP, all this can be done with a simple switch of an option.
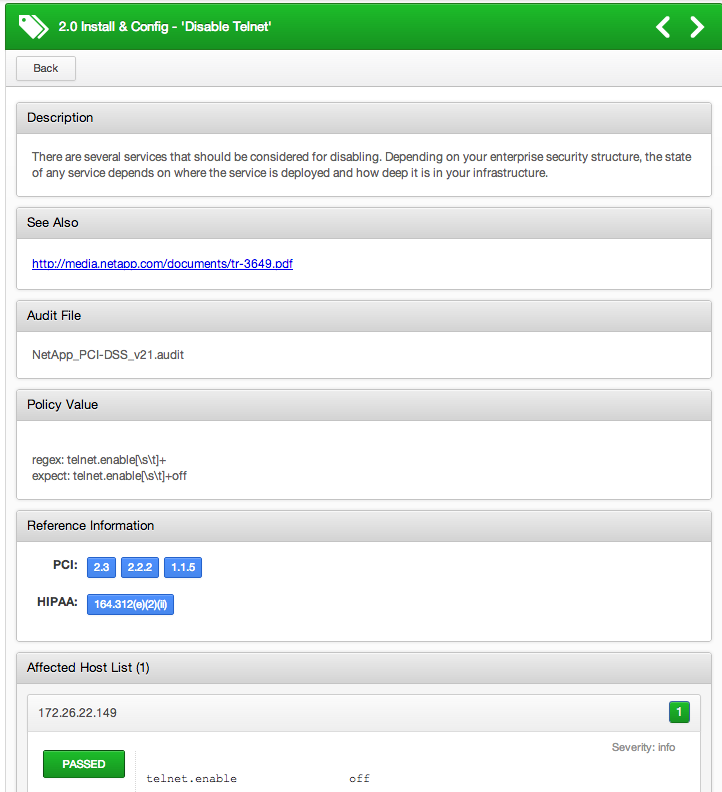
Note that Nessus .audits have PCI and HIPAA cross-references wherever applicable.
Getting Started Auditing NetApp Data ONTAP
The NetApp storage compliance checking plugin logs into the system using SSH. Nessus executes the 'options' command and performs the audit against the output. Provide Nessus with root-level credentials to the NetApp appliance, upload a NetApp audit policy into your Nessus policy, and enable Plugin ID #66934 (NetApp Data ONTAP Compliance Checks).
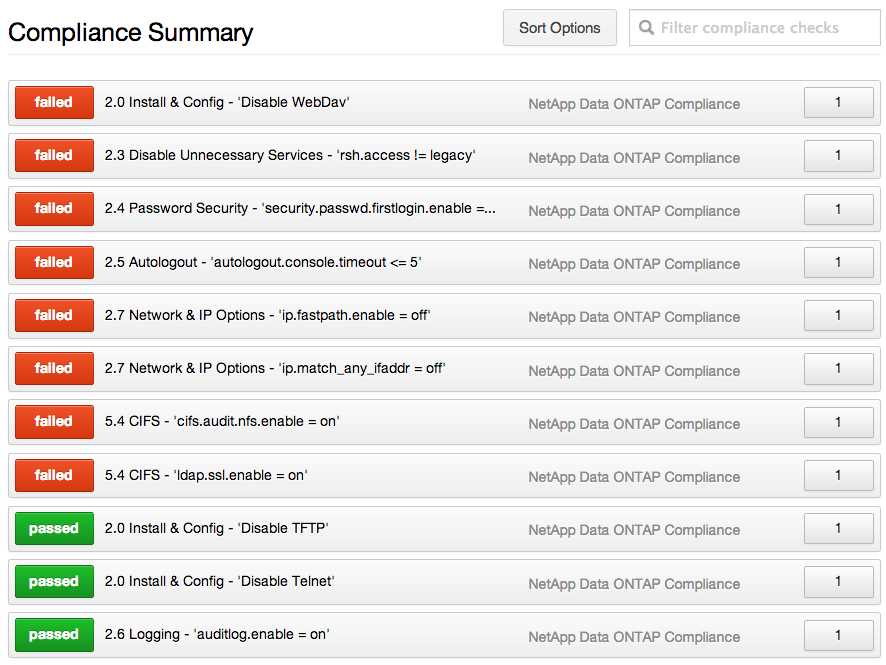
Below is a sample of the NetApp Data ONTAP compliance results which show how many hosts passed and failed each check.
The following screenshot shows that host 172.26.22.149 passed the 'Disable Telnet' check. Note that relevant PCI and HIPAA cross-references are linked.
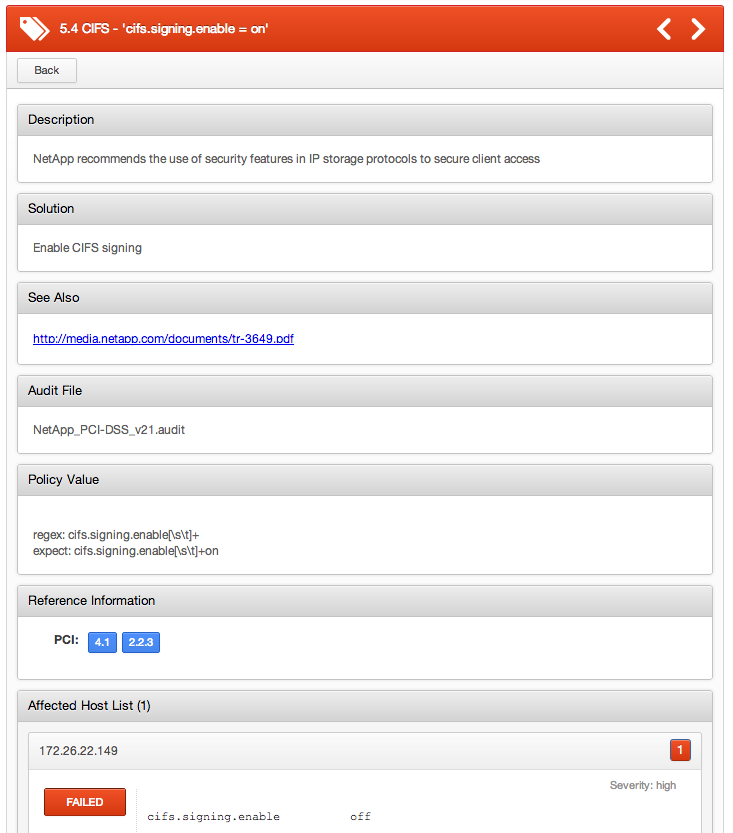
This screenshot shows that host 172.26.22.149 failed the 'cifs.signing.enable = on' check because CIFS signing is not enabled.
In addition to the compliance plugin, other Nessus plugins also report the operating system (OS) version and the last time the filer was rebooted. See the results for Plugin ID #11936 and #56468 for more details.
For More Information
For more information and technical details, please refer to the following posts on the Tenable Discussion Forum.
Learn more
- Nessus
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success