SamSam Ransomware: How to Identify and Mitigate the Risk

SamSam ransomware, which hit the city of Atlanta's systems in late March 2018, continues to be a threat. The most recent iteration leverages brute force remote desktop protocol (RDP) as an attack vector.
Updated on August 22, 2018
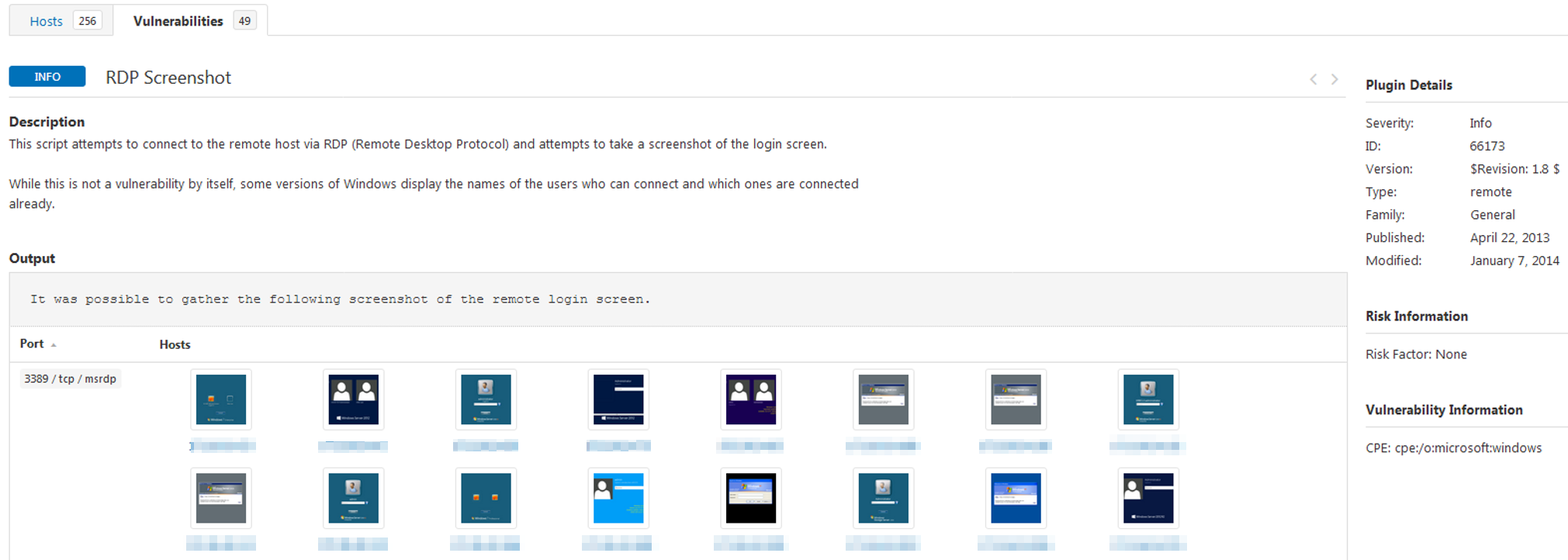
The latest iteration of SamSam attacks primarily leverages brute force RDP via tools like NLBrute while it previously leveraged JBoss/deserialization vulnerabilities. Plugin 66173 will detect exposure of remote RDP targets (rdp_logon_screen.nbin)
Remote RDP widens your attack surface and can be an easy way for attackers to get into your network. If you must use remote RDP, Two-Factor Authentication (2FA) along with VPN / access control mechanisms will reduce some of the risk. In addition to locking down RDP, we recommend following best practices such as tested and reliable backups, password complexity, least privilege and network segmentation. Tenable also has the CIS Policy Compliance Audit templates available for a wide range of Microsoft operating systems. Scanning and applying the recommendations in these audits can also potentially reduce data theft risk..
Note: In one 2017 incident, the SamSam actors disabled the endpoint security for a number of hosts on the target network, enabling additional damage to take place. This damage highlights the need for a more balanced approach to network defense that provides an array of protections including host-based and network-based vulnerability detection - something we can also help with.
Ransomware details
SamSam ransomware was active in early 2016 and is now making a comeback. This ransomware has been identified in attacks that shut down systems at the Colorado Department of Transportation in February 2018 and Hancock Heath, a regional hospital in Indiana, in January 2018. SamSam ransomware exploits older, unpatched JBoss system and Java deserialization vulnerabilities. It's known to initiate via RDP brute force attacks.
The vulnerabilities exploited by SamSam include those identified in the following CVEs:
- CVE-2010-0738
- CVE-2012-0874
- CVE-2010-1428
Identifying affected systems
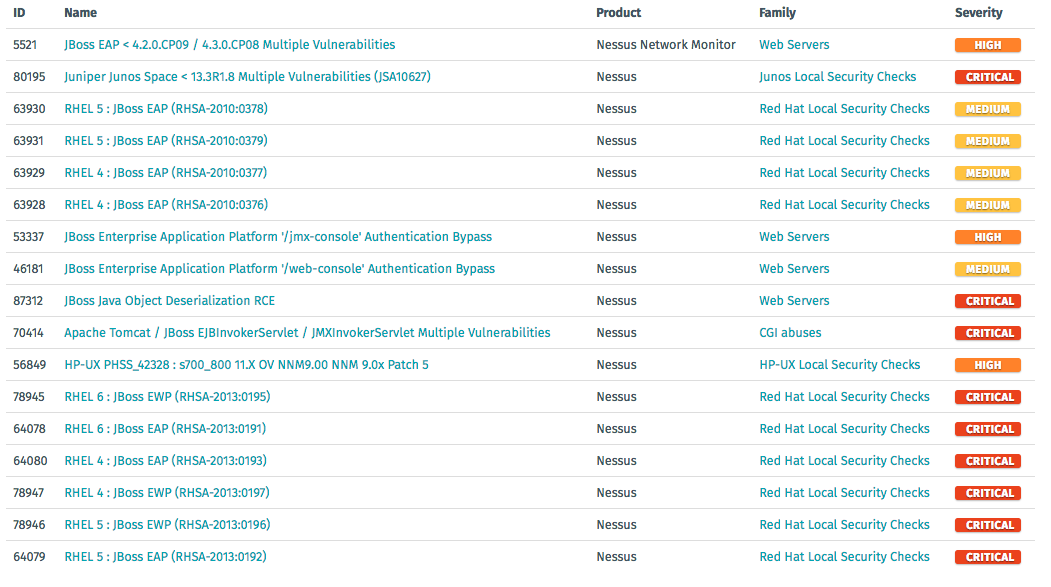
Tenable detects these vulnerabilities via the following plugins:
What should you do?
There are patches available for the vulnerabilities exploited by the SamSam ransomware. We advise upgrading JBoss servers to the latest version. To protect against RDP brute forcing of credentials, we also recommend restricting access and instituting a strong password policy.
Tenable developed Nessus® plugins to detect these vulnerabilities for Tenable.io Vulnerability Management, SecurityCenter and Nessus Pro. Specifically, these plugins identify vulnerabilities that would allow a remote attacker to utilize the JBoss flaw to gain access to sensitive information. In addition, Tenable.io Container Security has detection for the vulnerabilities in Docker container images.
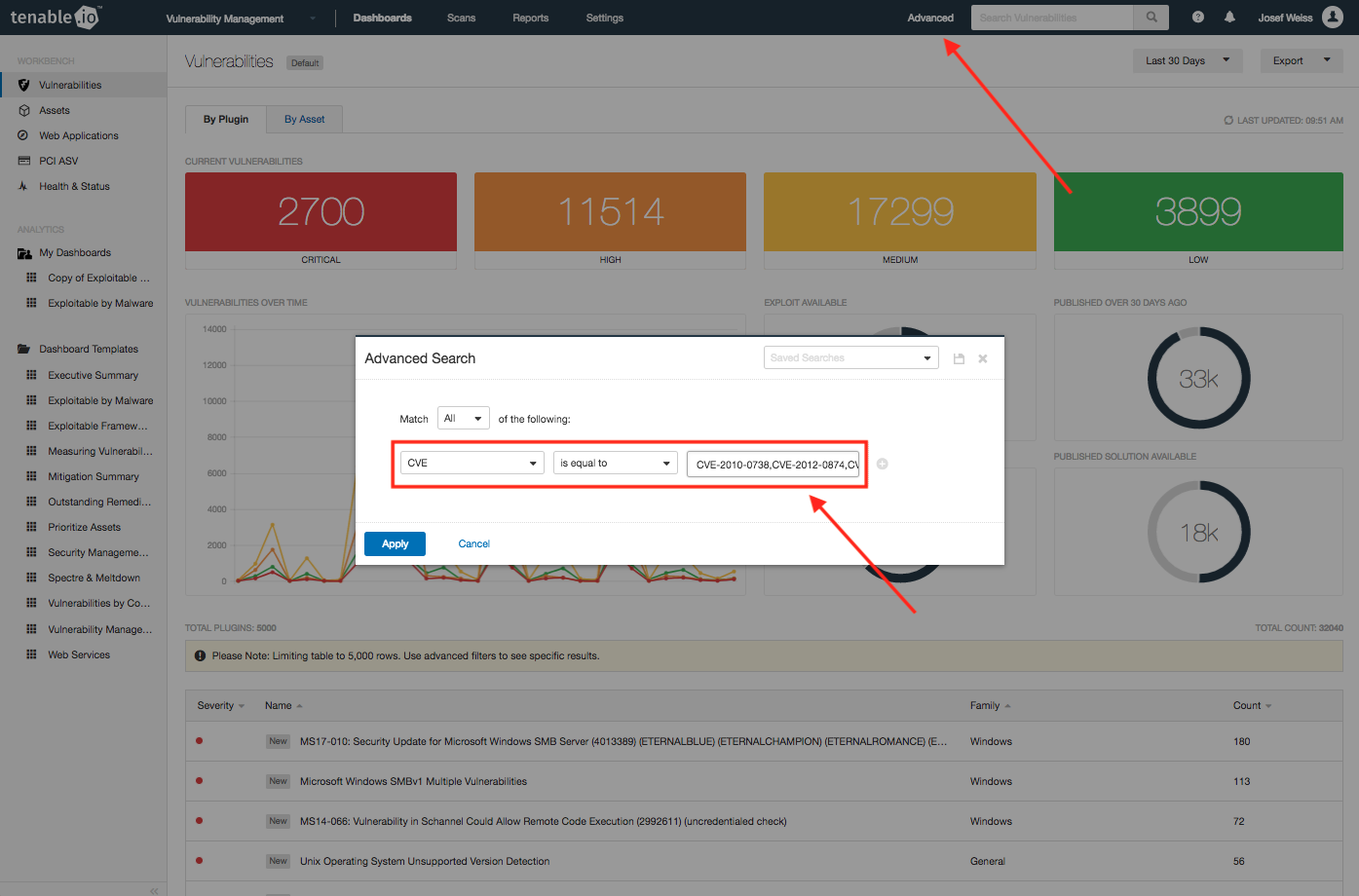
To determine if you’re currently vulnerable to any of the exploits listed above, log into Tenable.io, click the Advanced link located on the top right area of the top navigation bar. Within the Advanced Search pop-up, select “CVE” from the pick list, using default “is equal to”, and enter the listed CVE IDs, separated by a comma. Then, click Apply, as shown in the image below.
Identified vulnerabilities will be displayed on the Vulnerability Workbench. See below.
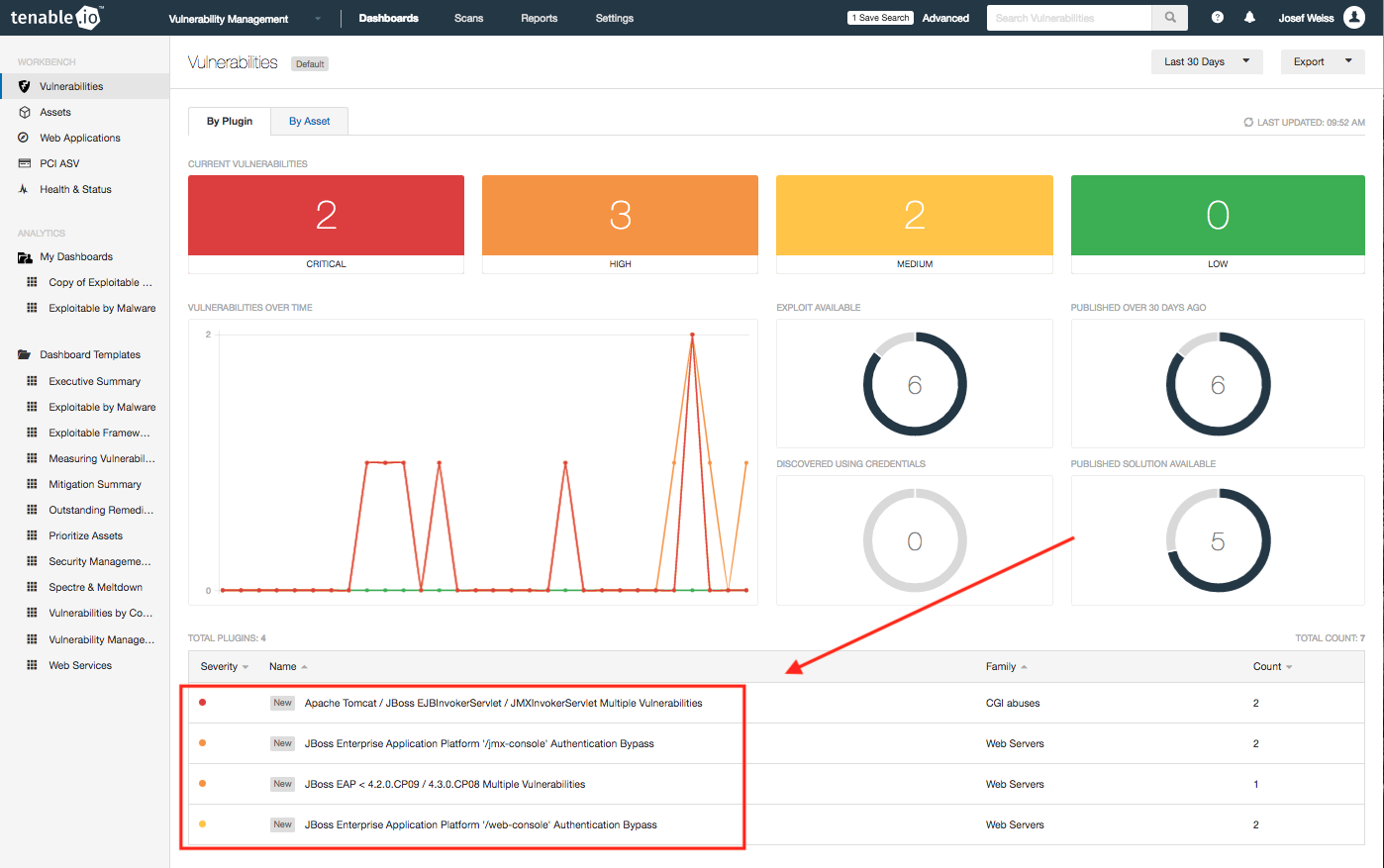
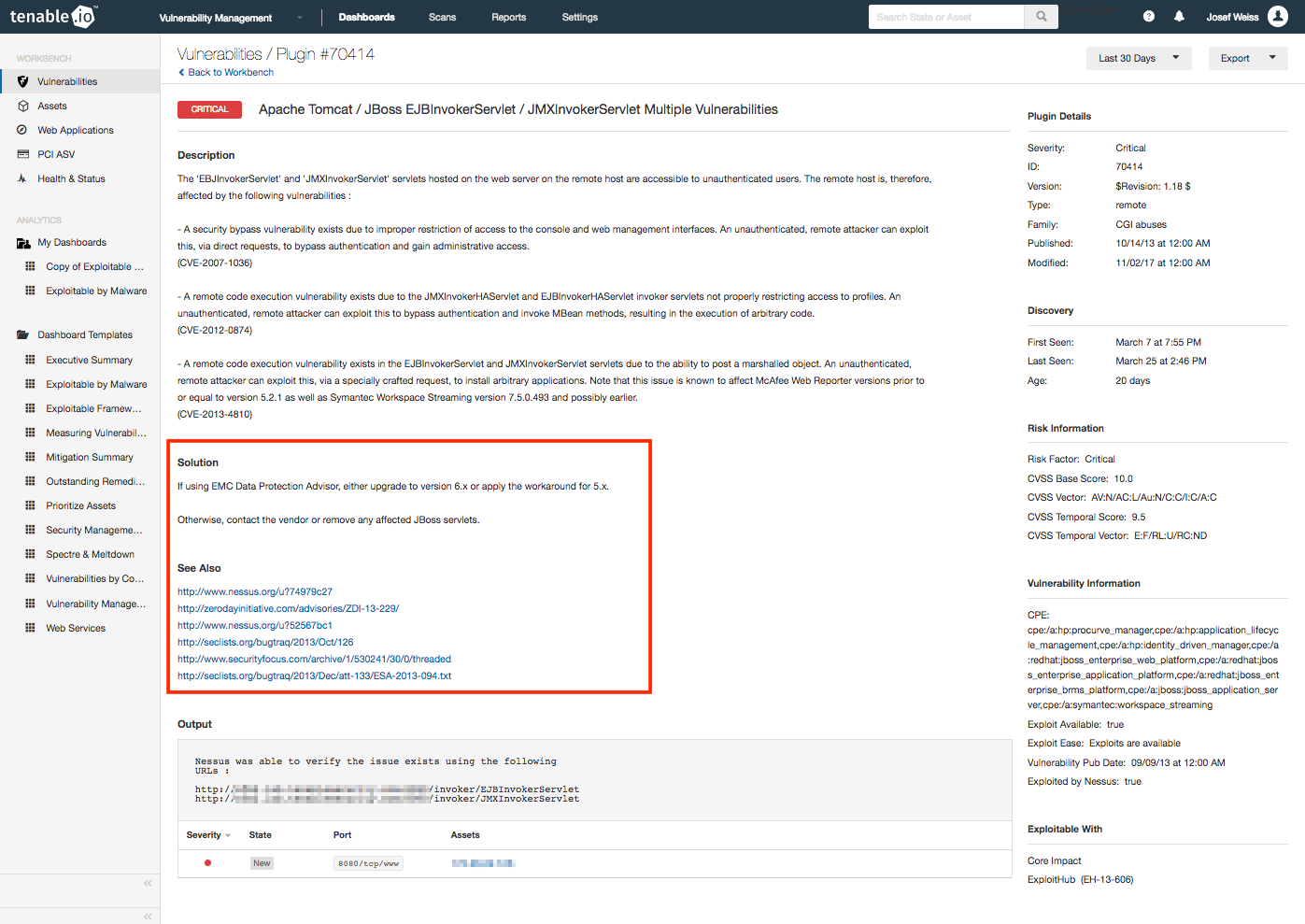
At this point, you may select a specific vulnerability to retrieve details, such as the Description, Solution and References, which will assist in mitigating the vulnerability.
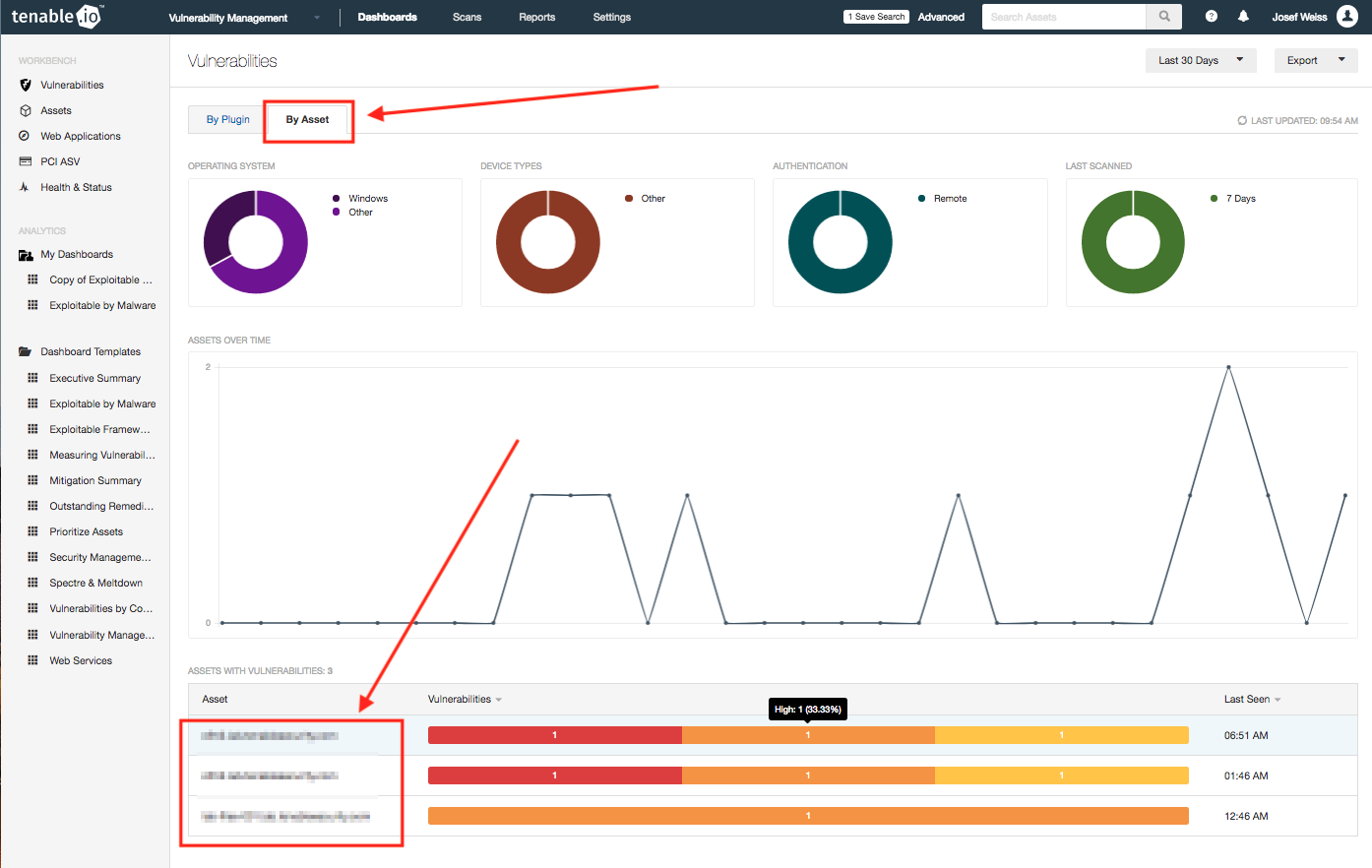
To view information about which specific assets are vulnerable, click the Assets tab on the Vulnerability Workbench. Selecting an asset will also present you with a vulnerability view, which when selected will also take you to the detailed view shown above.
Most ransomware exploits well-known vulnerabilities that already have patches available.
Get more information
- Learn more about Tenable.io, the first Cyber Exposure platform for holistic management of your modern attack surface
- Get a free 60-day trial of Tenable.io Vulnerability Management
- BleepingComputer - SamSam Ransomware Hits Hospitals, City Councils, ICS Firms
Many thanks to Rajiv Motwani, Steve Tilson, Anthony Bettini, Clint Merrill and the entire Tenable Research team for their contributions.
Learn more
- Plugins
- Tenable Vulnerability Management
- Tenable.io Container Security
- Tenable Vulnerability Management (DO NOT USE)
- Vulnerability Scanning



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success