Tenable One Cloud Exposure
Prevent cloud breaches and reduce cloud risk by closing gaps that misconfigurations, risky entitlements, and vulnerabilities create across multi-cloud and hybrid environments — all in one powerful CNAPP.
Quick links
View Tenable’s specialized cloud security tools tailored to your unique environment
Close cloud exposures with visibility and context across multi-cloud environments
Find, prioritize, and reduce cloud security risks with accuracy and confidence
Choose Tenable One Cloud Exposure, part of the Tenable One Exposure Management Platform, to get deep insight into all your cloud resources, identities, and risks. Extend exposure management to secure your entire attack surface, including multi-cloud and hybrid cloud environments.
Tenable One Cloud Exposure reviews
Tenable named a Customers’ Choice in the 2025 Gartner® Peer Insights™ Voice of the Customer for Cloud-Native Application Protection Platforms

tenable one
Available through Tenable One: The world’s only AI-powered exposure management platform
Tenable One solves the central challenge of modern security: a deeply divided approach to seeing and doing battle against cyber risk. We remove risk by unifying security visibility, insight and action across the attack surface to rapidly expose and close gaps. Customers use Tenable One to eradicate priority cyber weaknesses and protect against attacks—from IT infrastructure to cloud environments to critical infrastructure and everywhere in between.
CNAPP FAQs
-
Where can I find documentation and release notes on Tenable Cloud Exposure Management?
-
Technical documentation for Tenable products is at https://docs.tenable.com. You must log in to your Tenable Cloud Exposure Management account to view release notes and documentation. Contact a Tenable representative for access to technical documentation and release notes.
-
What is the difference between Tenable Cloud Exposure Management and Tenable One?
-
Tenable Cloud Exposure Management can be purchased as a standalone product or as part of the Tenable One Exposure Management Platform. When combined with Tenable One, Tenable Cloud Exposure Management provides a comprehensive view of your entire IT environment, encompassing traditional networks, on-premises servers, operational technology, and public clouds. By purchasing Tenable Cloud Exposure Management as part of Tenable One, organizations can consolidate their Tenable purchases into a single contract and access additional features, such as exposure views.
-
What clouds and cloud native tooling does Tenable Cloud Exposure Management integrate with?
-
Tenable Cloud Exposure Management integrates with all major cloud providers (AWS, Azure, GCP) in addition to a number of cloud provider services such as AWS Control Tower and Entra ID. Integrate Tenable Cloud Exposure Management with your ticketing, notification, and SIEM tools to support the creation of tickets and the sending of push notifications and utilize standard communication tools such as Jira, Slack, Microsoft Teams and email integration tools to scale the tool within your organization.
-
What identity providers does Tenable Cloud Exposure Management support?
-
Tenable Cloud Exposure Management integrates with numerous IdPs including Entra ID, Google Workspace, Okta, OneLogin and Ping Identity. These IdP integrations reveal a complete inventory of federated users and groups associated with your cloud accounts and provide permission analysis and identity intelligence.
-
How does Tenable Cloud Exposure Management protect my data?
-
Tenable ensures the safety of your workloads, employing robust encryption and access controls to safeguard sensitive data. It reins in excessive permissions and granting of long-standing access. Tenable protects your sensitive data by reducing the blast radius in the event of a breach. For more information on how Tenable Cloud Exposure Management ensures data protection and privacy of your unique cloud environment, please contact your Tenable representative.
-
Can I use Tenable Cloud Exposure Management without involving third parties?
-
Yes. Tenable Cloud Exposure Management users can purchase in-account scanning as an add-on for their environment. This functionality supports onsite scanning of workloads for organizations beholden to narrow data privacy standards and regulations. In-account scanning is performed in your cloud account, and the data never leaves the environment.
-
How can I purchase Tenable Cloud Exposure Management?
-
To purchase Tenable Cloud Exposure Management you can work with your local certified partner or contact your Tenable representative. Click here to request a demo of Tenable Cloud Exposure Management
-
Does Tenable Cloud Exposure Management support shift-left and IaC security?
-
Tenable Cloud Exposure Management embeds security directly into the development pipeline by scanning IaC templates — including Terraform, CloudFormation, and Kubernetes manifests — for misconfigurations, compliance gaps, and policy violations. This shift-left approach catches risks at the source, reducing costly fixes later and creating a shared security workflow between DevOps and SecOps teams.
-
Which factors does Tenable Cloud Exposure Management take into consideration when prioritizing remediation workflows in the cloud?
-
Tenable Cloud Exposure Management uses a contextual risk model that weighs three dimensions:
- Threat detection and intelligence: Is there active exploitation or a known proof of concept for the vulnerability?
- Exposure context: Is the affected resource publicly accessible, over-privileged, or linked to other weaknesses that create a toxic combination?
- Asset criticality: Does the resource store regulated data (PII/NPI), support revenue-generating services, or operate in a production environment?
By combining these factors, teams move beyond generic severity scores and focus remediation on what actually puts the business at risk and what your true exposure is.
-
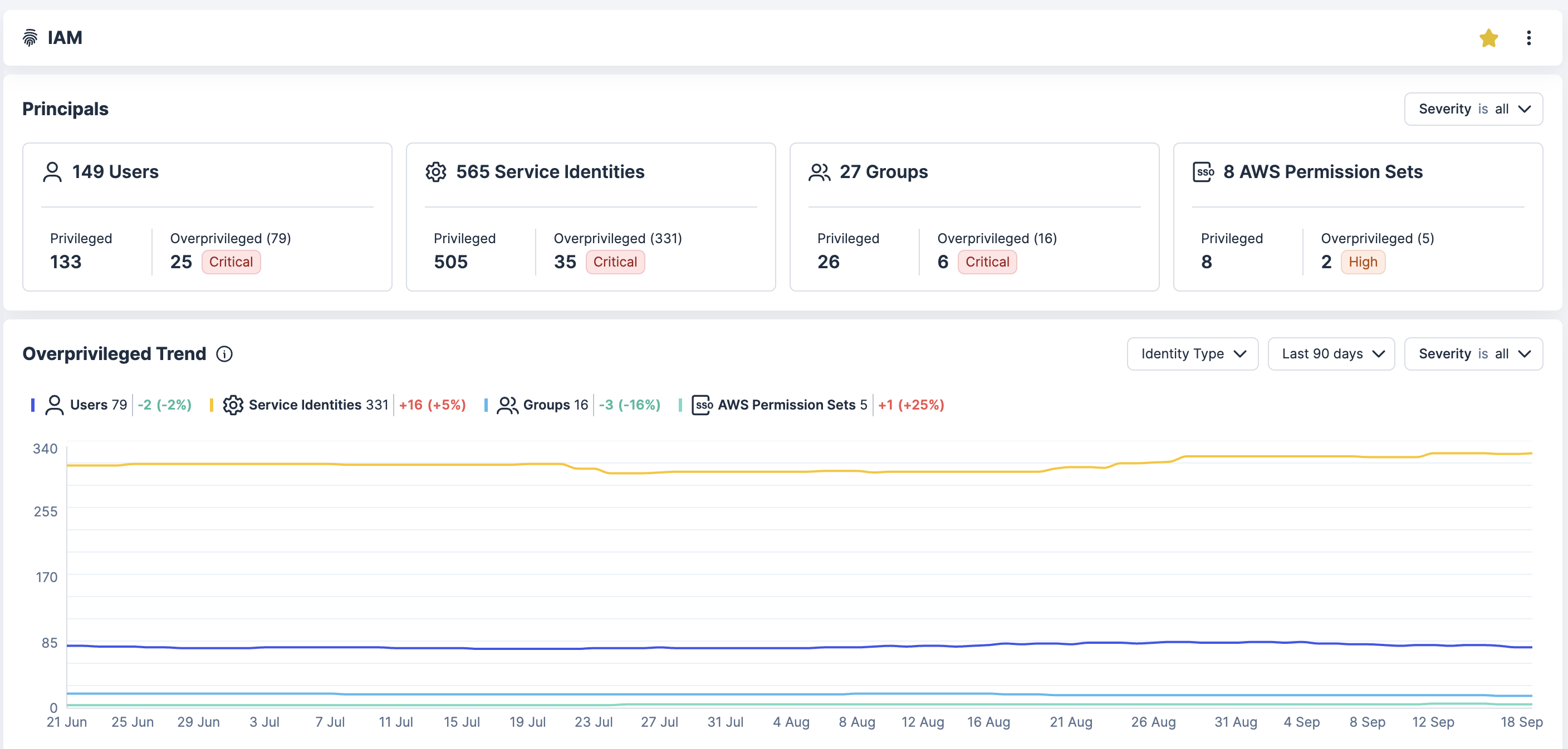
What tools does Tenable Cloud Exposure Management offer to manage cloud identity and access risks?
-
Tenable Cloud Exposure Management includes an integrated CIEM capability that continuously analyzes entitlements across AWS, Azure, and GCP. It maps effective permissions to reveal toxic combinations and hidden attack paths, flags stale or overly broad access, and supports just-in-time (JIT) access controls to enforce least privilege. Automated remediation workflows help security teams right-size permissions at scale without disrupting development velocity.








_EasiestSetup_EaseOfSetup.png)




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success