Tenable One Vulnerability Management
By unifying vulnerability insights with broader security data in the Tenable One exposure management platform, you gain the precision needed to prioritize the most critical exposures, drive faster remediation, and secure your modern attack surface with a single, unified experience.
Quick links
View Tenable’s specialized vulnerability management tools tailored to your unique environment
Exposure management begins with vulnerability management
Discover, prioritize, and remediate critical vulnerabilities
Tenable One Vulnerability Management reviews
Tenable is the only vendor to be named a Customers’ Choice in the 2025 Gartner® Peer Insights™ Voice of the Customer for Vulnerability Assessment

tenable one
The world’s only AI-powered exposure management platform
Tenable One reduces cyber risk by unifying security visibility, insight and action across the entire attack surface, helping organizations quickly find and fix critical weaknesses.
Discover why industry experts choose Tenable
FAQs
-
What are the vulnerability management capabilities of Tenable One?
-
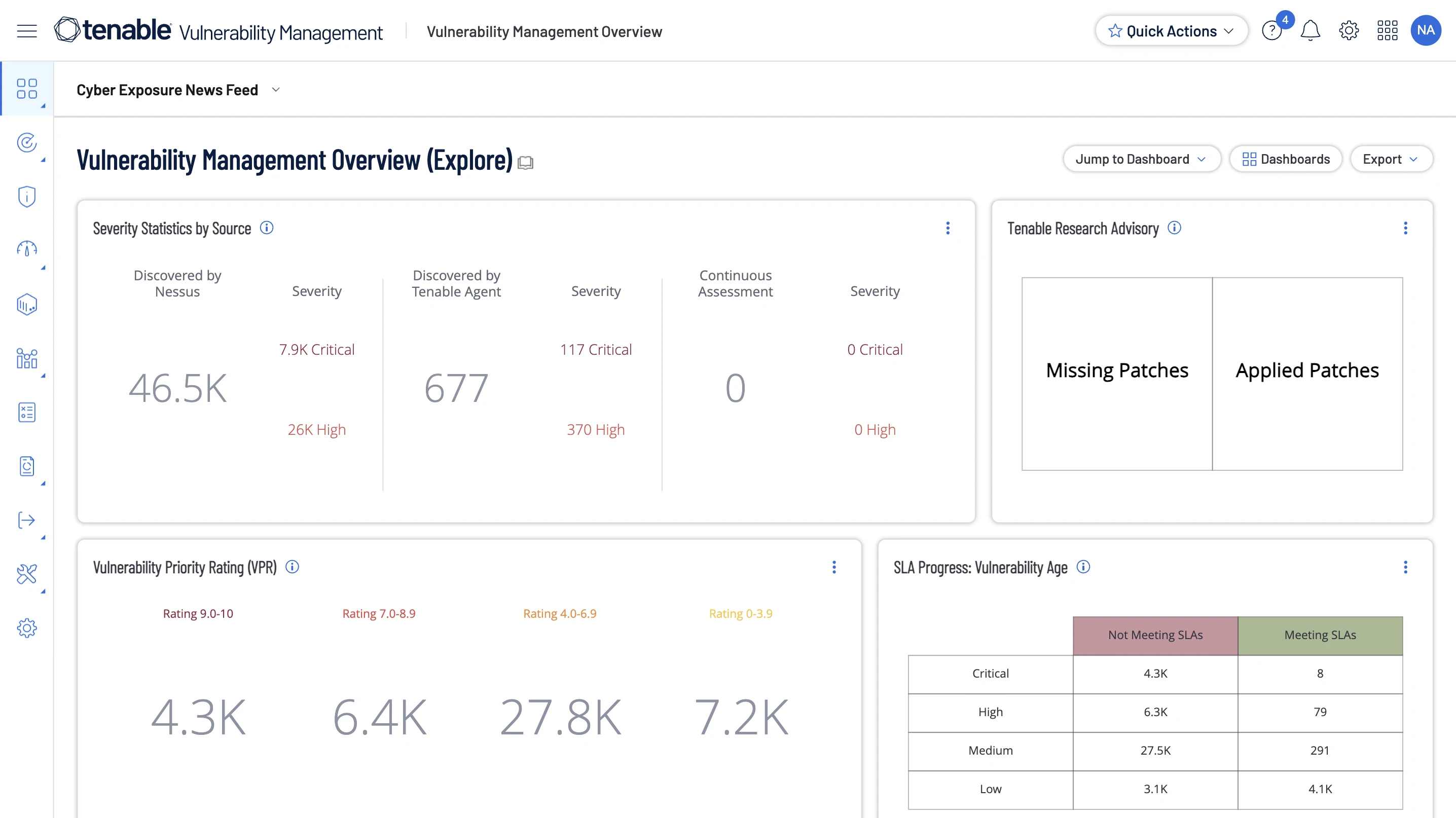
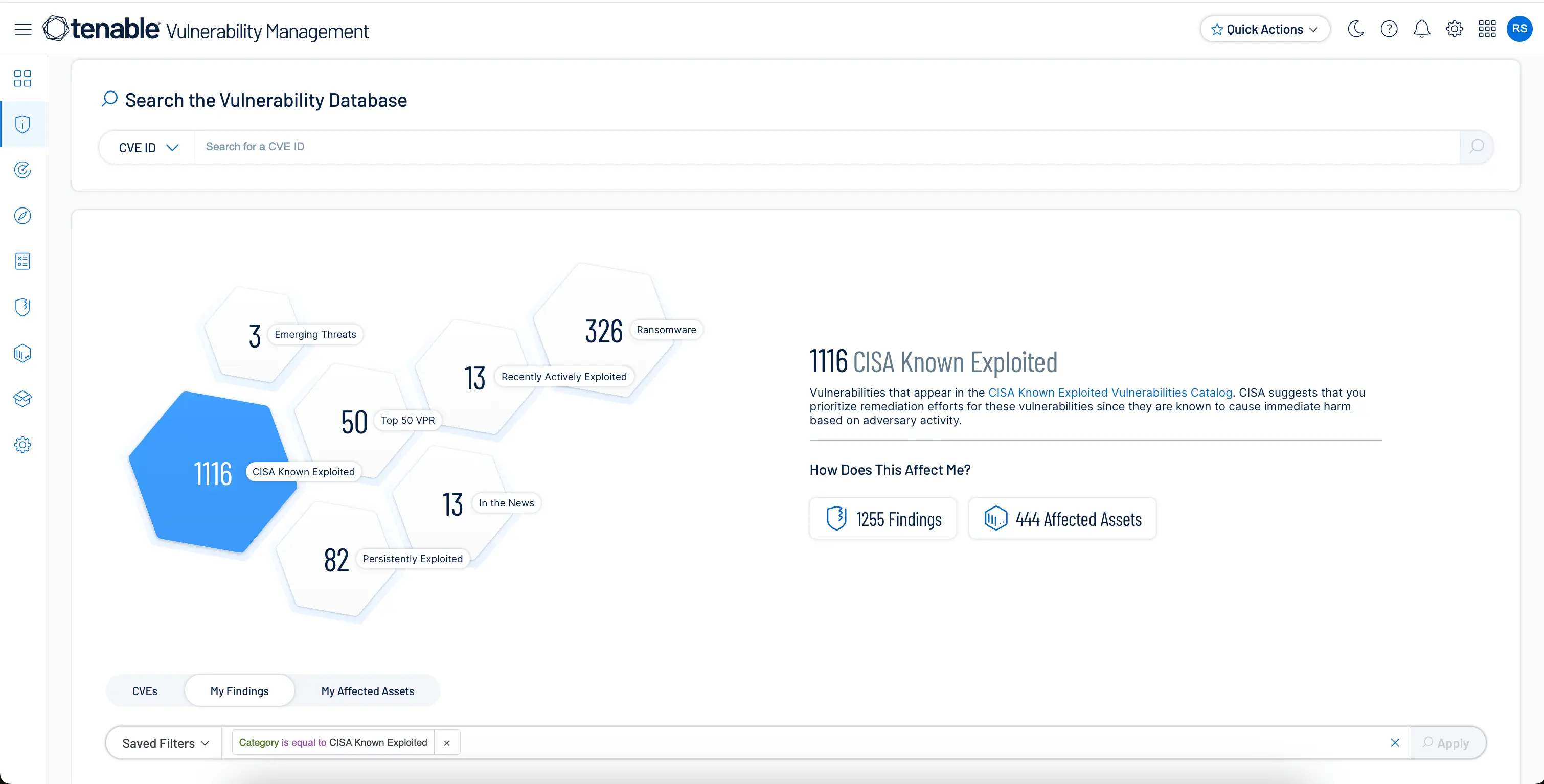
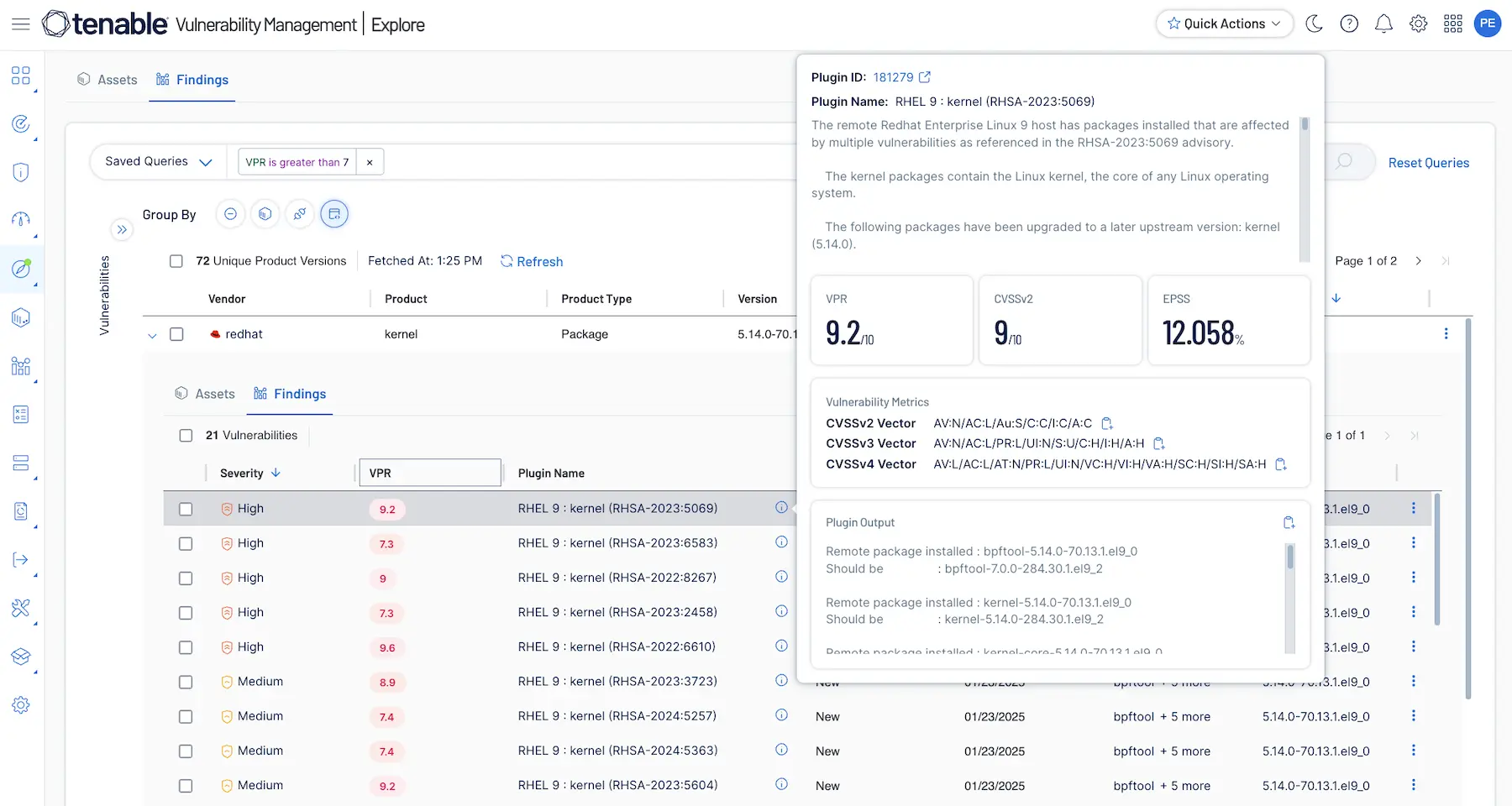
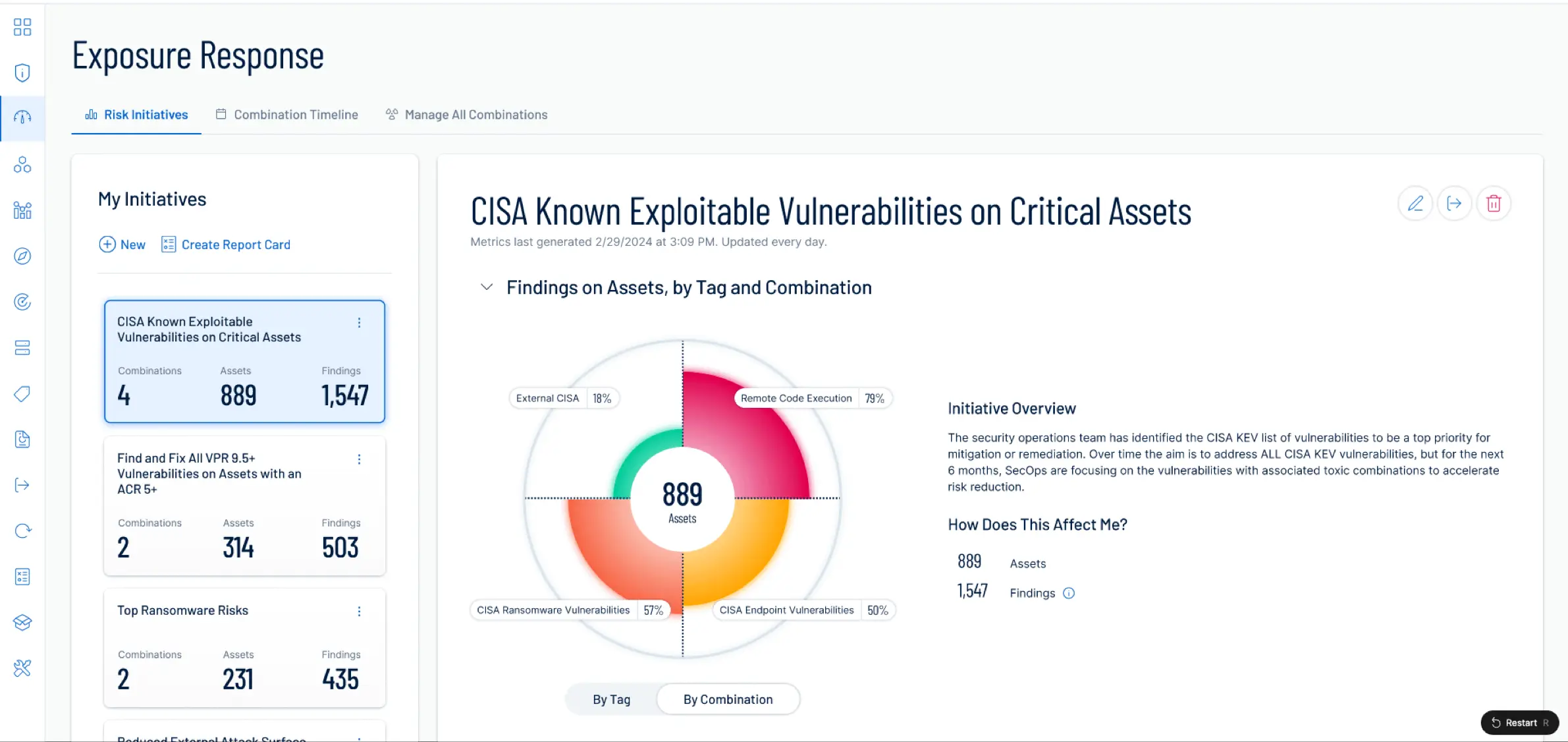
Vulnerability management is a critical capability of the Tenable One platform. Tenable One Vulnerability Management gives you full network visibility to predict attacks and quickly respond to critical vulnerabilities. Continuous, always-on discovery and assessment provide the visibility you need to find all assets on your network, as well as hidden vulnerabilities on those assets. Built-in prioritization, threat intelligence, and real-time reporting help you understand your risk and proactively disrupt attack paths. Built on leading Tenable Nessus technology and managed in the cloud, Tenable One gives you complete visibility of the assets and vulnerabilities on your network so you can quickly and accurately understand your risk and know which vulnerabilities to fix first. Expand beyond vulnerabilities with the Tenable One Exposure Management Platform to cover AI platforms, cloud workloads, containers, OT systems, and identity systems and protect your entire modern attack surface.
-
I require an on-premises solution for vulnerability management. What are my options with Tenable?
-
Tenable Security Center is Tenable’s on-premises vulnerability management solution that gives you a comprehensive view of all the assets and vulnerabilities on your network so you can understand cyber risk and know which vulnerabilities to fix first.
Tenable Enclave Security empowers you to know, expose, and close IT and container weaknesses across your modern infrastructure. Built for highly secure environments, you get industry-leading vulnerability management and modern workload protection to help continuously discover and analyze IT and container assets to understand vulnerability exposures and prioritize high-risk vulnerabilities for remediation. Tenable Enclave Security supports your organization’s strict cloud security and data residency requirements, including FedRAMP High, Impact Level 5, and air-gapped environments.
For a comprehensive understanding of these offerings, contact your Tenable certified partner or Tenable representative for more information.
-
Can Tenable One help me identify AI vulnerabilities?
-
Yes, Tenable One continuously discovers AI across your entire organization, whether it’s running internally or externally, on premises or in the cloud, to give you a complete, risk-aware view of where AI operates, how it is connected, and where it creates exposure. By correlating these relationships, Tenable One helps security teams prioritize the AI exposures that matter most and reduce AI risk across all environments.
Use Tenable One to:
- Discover AI running inside your organization, whether it’s approved, unapproved, or embedded. Maintain a unified, up–to-date view of AI software, libraries, models, and services operating across your organization. See which AI components are outdated, vulnerable, or misconfigured so you can prioritize remediation based on real risk.
- Protect AI workloads and agents. Identify and prioritize risky configurations in cloud-based AI workloads and model environments that could expose models, agents, data, or APIs.
- Detect and respond to prompt injection attempts, jailbreak behavior, and malicious instructions designed to manipulate AI systems. Isolate erratic and misbehaving agents.
- Govern AI usage. Identify sensitive data, intellectual property, and PII being shared with AI platforms and agents. Surface AI-related risks with precise context, including the AI engine, user, and specific interaction or session involved, enabling rapid understanding and response.
Unlike point AI security tools that surface isolated findings, Tenable One correlates AI, infrastructure, agents, and data exposure into a unified view, so you can reduce AI risk across all environments, even as your developers leverage AI for scale and productivity.
-
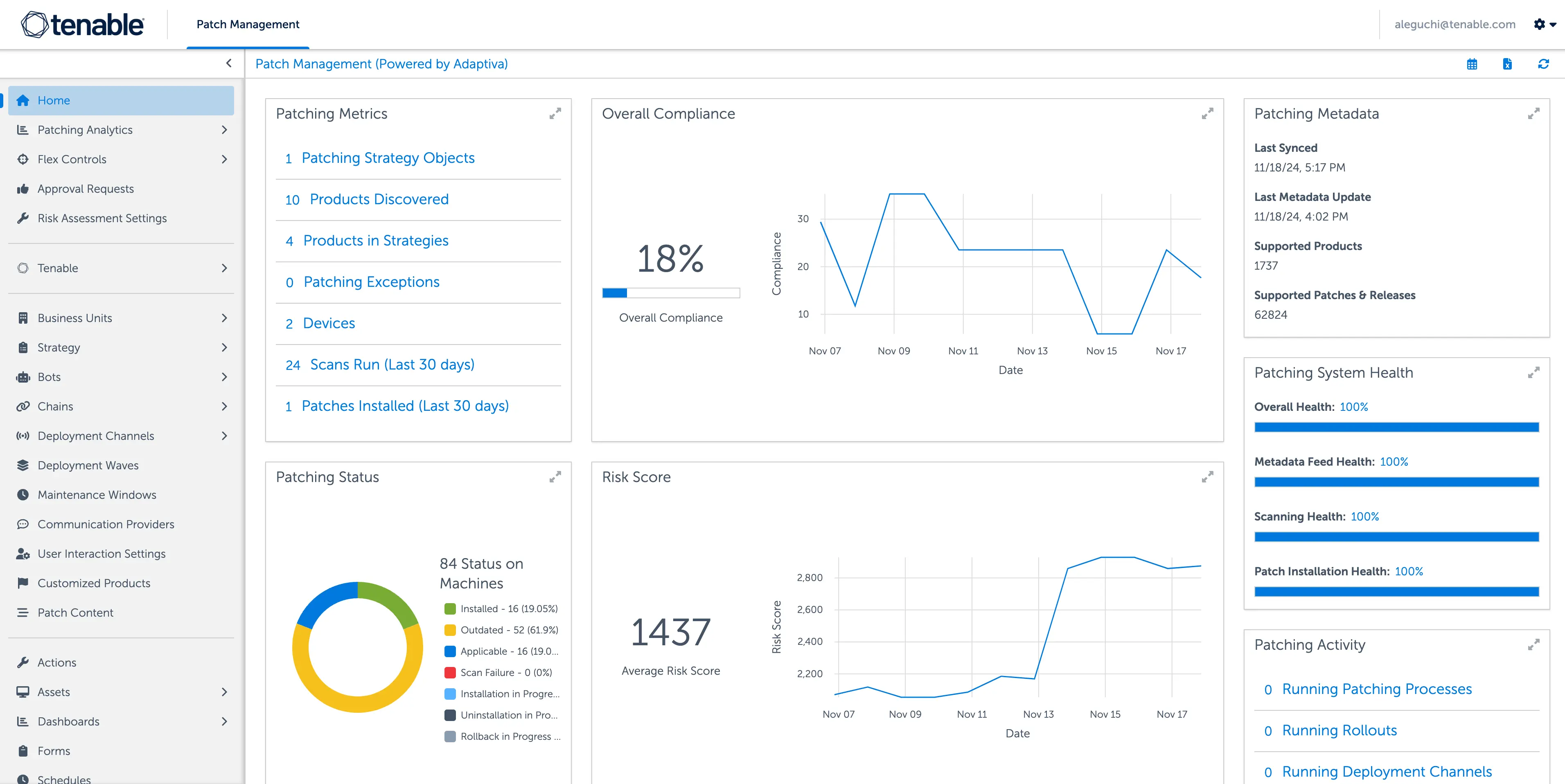
What is Tenable Patch Management?
-
Tenable Patch Management is a patch management module that pairs Tenable’s industry-leading prioritization capabilities with autonomous patch functionality. Automated correlation between vulnerabilities and the most up-to-date remediation action helps your teams overcome bottlenecks that frequently occur between vulnerability prioritization and remediation. Built to scale up or down to fit any organization, Tenable Patch Management enables you to manage settings around deployments, testing, approvals, applications, and more with precision and granularity.
To leverage Tenable One Patch Management, you need a license for Tenable One Vulnerability Management, Tenable Security Center, Tenable One, or Tenable Enclave Security. Learn more here.
-
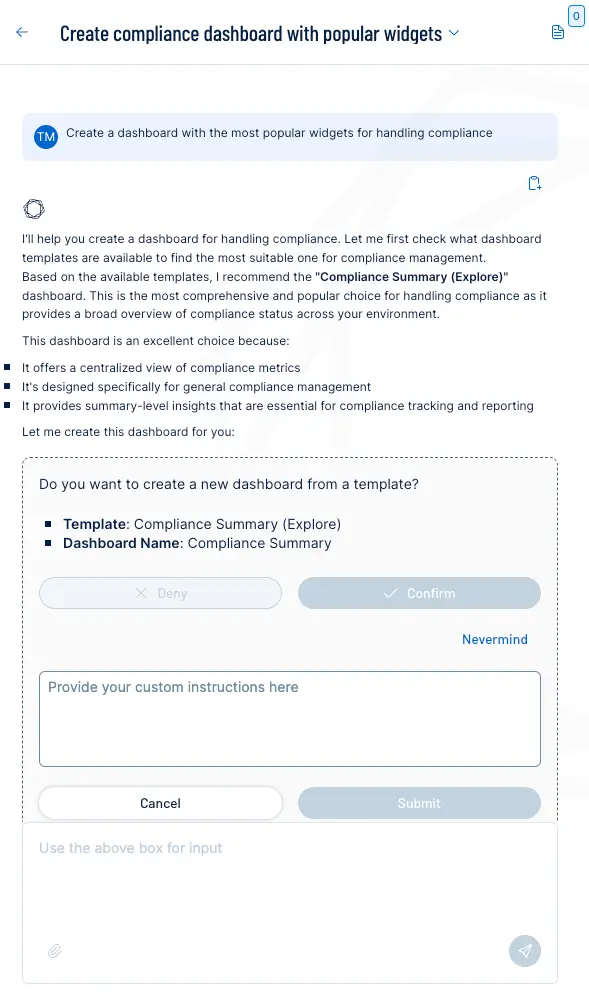
Can Tenable One help me stay compliant with PCI standards?
-
Yes, Tenable PCI ASV helps you stay compliant with PCI standards by streamlining the entire scanning and attestation process. Integrated directly into Tenable One Vulnerability Management and Tenable Web App Scanning, this solution allows you to quickly prepare for PCI DSS Requirements 11.3.1 and 11.3.2. You can manage everything from running scans to resolving disputes in one centralized dashboard, using ready-made templates to fix issues on your own timeline. The process is further optimized by allowing you to carry over disputes and exceptions from one quarter to the next, ensuring a seamless and efficient path to final attestation.
-
How can I protect my hybrid-cloud assets without increasing operational complexity?
-
Vulnerability management practitioners can leverage agentless workload and container vulnerability coverage without complexity through Tenable Cloud Vulnerability Management. This solution allows you to extend your existing vulnerability management best practices into hybrid-cloud environments while unifying visibility across both on-premises and cloud assets. By deploying agentless scanning, you can quickly prioritize and fix vulnerabilities across workloads and correlate risks between containers and traditional infrastructure. This ensures you can scale Tenable's leading security intelligence across every environment—including hybrid and multi-cloud setups—all within a single, unified view.
-
What is an asset?
-
An asset is:
- A physical or virtual device with an operating system connected to a network
- A web application with an FQDN
- An active (not terminated) cloud resource
-
Does Tenable offer a service level agreement (SLA) for Tenable One Vulnerability Management?
-
Yes. Tenable provides the vulnerability management industry’s first uptime guarantee of 99.95% through a robust service level agreement (SLA) with service credits offered if the SLA is not met.
Tenable uses the AWS platform and other leading technologies to ensure high availability for customers. Using fault tolerant and redundant components, Tenable ensures you get the best possible service with minimal downtime.
-
Where can I find documentation and release notes on Tenable One Vulnerability Management?
-
Technical documentation for all Tenable products, including Tenable One Vulnerability Management, is at https://docs.tenable.com.
-
How can I learn more about Tenable One Vulnerability Management?
-
To learn more about Tenable One Vulnerability Management, please visit the Tenable One Vulnerability Management product page, register for a free evaluation or contact your Tenable certified partner or Tenable representative for more information.
-
How can I purchase Tenable One Vulnerability Management?
-
To purchase Tenable One Vulnerability Management, you can work with your local certified partner, contact your Tenable representative or visit tenable.com.





Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success