Tenable Issues Shellshock Detection Plugins, Wizard, Dashboard
As many of you know, a major vulnerability was discovered yesterday. CVE 2014-6271 and CVE 2014-7169, known as “Shellshock” in the media, affects Linux and OS X and Unix systems that use any version of Bash 4.3 and lower. The Bash shell is one of several different command shells used with Unix and is also a way to invoke scripts. What makes Shellshock unique is the impact it could have on the security of the Internet and the difficulty in detecting all attack vectors. In short, Shellshock’s effect could be similar to Heartbleed’s impact.
Due to the ease of exploit, Shellshock is a prime candidate for a worm
The Shellshock vulnerability allows a variety of remote attacks, most likely through Linux web servers that run scripts, but also through popular services like Secure Shell (SSH) and even internal network protocols such as DHCP servers running on Unix. It also allows a variety of privilege escalation attacks where a non-administrator Unix user could cause commands to be run as root.
The potential for attackers utilizing Shellshock is huge. With millions of Unix and Linux servers being vulnerable and running web services that hackers can connect to, the attack surface is staggering. Not all of the attack vectors have been discovered, but just Linux running Bash and mod_cgi accounts for a significant number of systems. The ease of attack is also a big concern; a crafted HTTP post with the right characters can enable any would-be attacker to upload files, modify HTML, or dump system files for further analysis.
The attack surface is staggering
On the surface, the general public does not appear to be at risk due to Windows being the consumer’s platform of choice. But attackers could easily upload malware to trusted destinations on the Web to infect uninformed visitors. Due to the nature of the vulnerability and the pervasiveness of Bash, some of the “Internet of Things” devices we now have in our homes and businesses could also be vulnerable, leaving home users with a significant security risk.
Unfortunately, due to the ease of exploit, Shellshock is a prime candidate for a worm. We could be looking at another SQL Slammer-like worm. But instead of 100,000 servers being affected, it could be more like 100,000,000, which could be catastrophic. It is of critical importance that you scan your networks now with Nessus or SecurityCenter to identify where Bash is installed and update it with the patches that are being released by the operating system vendors.
Update: Wizard and Plugins added to Nessus
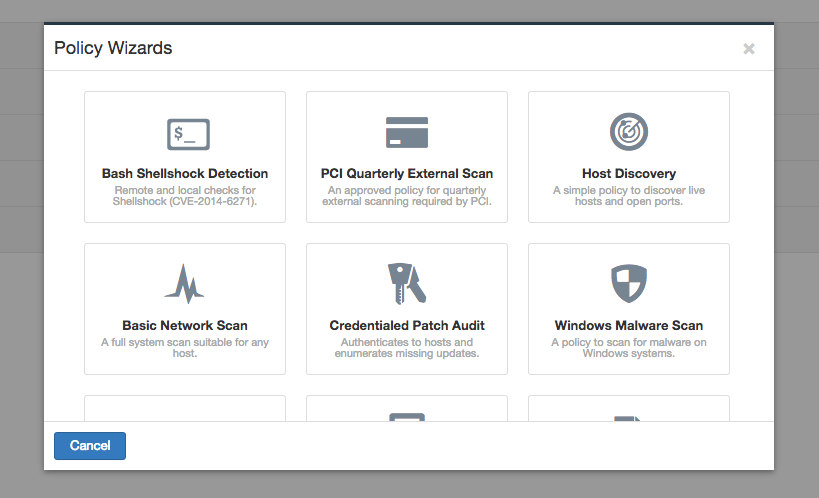
Tenable has released a series of Nessus plugins to do patch checks, to test for the Shellshock vulnerability via SSH with an authenticated scan, and to test for the vulnerability via HTTP(S). Visit the Nessus Newest Plugins page for the complete list of available plugins.
The Nessus scanner also has a new Policy Wizard for Bash Shellshock Detection. When you create a new policy and run the wizard, it will download and use the Bash plugins. Brief instructions are in our Discussions forum.
Update: Dashboard and Report added to SecurityCenter
SecurityCenter now includes a Shellshock dashboard and report to help determine if your systems are vulnerable to Shellshock. These components are available in the SecurityCenter Feed.
Learn more
- Dashboards
- Nessus
- Plugins
- SecurityCenter



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success