by Cody Dumont
September 26, 2014
A critical vulnerability in bash (Bourne Again SHell) versions through 4.3, the default shell for many Linux and Unix distributions including Mac OS X, presents a critical security concern for network-attached devices that use bash, especially those with an attack vector that can be exploited remotely (e.g., web servers, SSH servers, and likely much more). This vulnerability, known as ‘Shellshock’, may be potentially bigger than Heartbleed and much easier to exploit. This dashboard presents several components that can assist an organization in determining if it has systems vulnerable to Shellshock. These components display alerts from several new plugins released by Tenable to detect Shellshock (CVE-2014-6271,CVE-2014-7169,CVE-2014-6277,CVE-2014-7186,CVE-2014-7187,CVE-2014-6278).
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Security Industry Trends.
The dashboard requirements are:
- SecurityCenter 4.8.1
- Nessus 5.2.7
- LCE 4.4.0
- PVS 4.0.2
Tenable’s SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with the Tenable Passive Vulnerability Scanner (PVS), as well as log correlation with the Tenable Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network, and can react quickly to threats such as Shellshock.
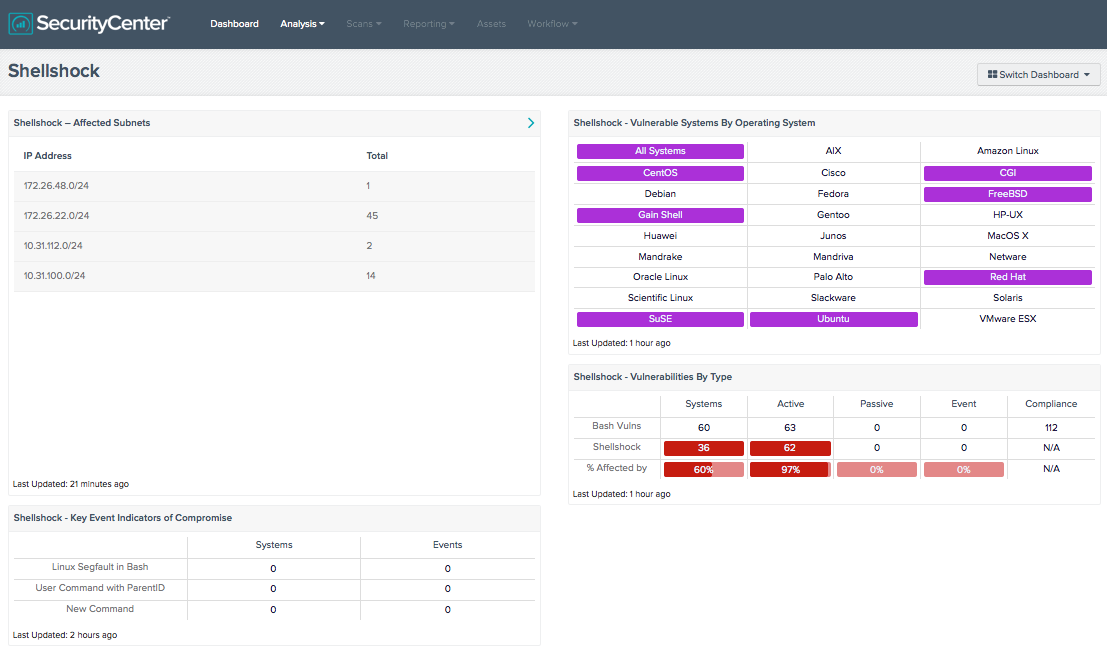
Shellshock – Affected Subnets: This component displays the Class C subnets of the network that contain systems that are vulnerable to Shellshock. The Total column displays the number of vulnerable systems on each subnet. Further investigation and remediation of these systems is needed.
Shellshock – Key Event Indicators of Compromise: This component displays the number of events that might be potential indicators of exploitation of the Shellshock vulnerability. For each event, the counts of systems and events are displayed. If any of these counts are non-zero, further investigation for the Shellshock vulnerability is needed. The ‘Linux Segfault in Bash’ denotes that a segmentation fault occurred in a running Linux process. The ‘User Command with ParentID’ denotes that a non-root user issued commands. The ‘New Command’ denotes that a new process not seen used before was encountered. These events might indicate exploitation of the Shellshock vulnerability, as described in Detecting Shellshock with LCE Process Accounting.
Shellshock – Vulnerable Systems by Operating System: This component displays indicators for each *nix operating system. Purple indicators denote that systems exist on the network with that operating system which are vulnerable to Shellshock. Further investigation and remediation of these systems is needed.
Shellshock – Vulnerabilities by Type: This component displays information about systems on the network with vulnerabilities related to bash. The first row contains detected general bash vulnerabilities, the second row contains detected Shellshock specific vulnerabilities, and the third row calculates the percentage of the general bash vulnerabilities that are Shellshock vulnerabilities. The first column shows the count of systems and the next four columns show the vulnerabilities detected actively, passively, via events, and via compliance checks (note that there are currently no compliance checks for the Shellshock vulnerability).