Tenable Introduces Agent-Based Scanning in Nessus Manager

Note: Nessus Cloud is now a part of Tenable.io Vulnerability Management. To learn more about this application and its latest capabilities, visit the Tenable.io Vulnerability Management web page.
Today, Tenable announced Nessus Agents, a new scanning method available in Nessus Manager, an improved version of the award-winning Nessus vulnerability management platform designed with enterprise users in mind. This article will introduce you to Nessus Agents, suggest a few scenarios where you'll find them useful, and let you know how to get started using them.
Nessus Agents are lightweight programs installed locally on a host
Nessus Agents are lightweight programs installed locally on a host – a laptop, virtual system, desktop, and/or server. Agents receive scanning instructions from a central Nessus Manager server, perform scans locally, and report vulnerability, compliance and system results back to the central server. Nessus Agents alleviate some of the biggest headaches of traditional network scanning, such as scanning without credentials or scanning assets that aren't always connected to the local network.
No credentials required with agent-based scanning
Does this sound familiar: you're responsible for scanning, but it’s challenging to access and maintain a list of credentials for various systems? Nessus Agents are an excellent way to overcome this challenge. While you still have the option to do agent-less scans with credentials, agents give you an alternative for scanning systems where you don't have credentials, or when it would be challenging to get or manage credentials.

Nessus Agents alleviate some of the biggest headaches of traditional network scanning
Since we're talking about systems administrators, we should note that the IT team often expresses concerns about overall agent performance, ongoing management or security. These are valid concerns. But Nessus Agents address these issues with the following features:
- The performance overhead of agents is minimal, and because agents rely on local host resources, they can potentially reduce your overall network scanning overhead.
- Agents can be deployed with your existing software management system. Once installed, agents are automatically kept up to date by Nessus Manager.
- Agents are designed to be highly secure, including leveraging encryption to protect your data.
Scanning laptops and other transient devices
The performance overhead of agents is minimal
Many organizations have employees who telecommute or bring work on their laptops home with them at night. If those laptops at home aren't VPN-connected when a scan is happening, they don't get scanned. And many of those laptops could be compromised. Type “bad things employees do with their work laptops” in your favorite search engine and you'll see responses like: “play games,” “download music,” “buy and sell on auction sites” and more. These aren't necessarily bad activities on their own, but these and other activities like them could potentially result in malware infections and other related issues.
Nessus Agents give you the ability to scan laptops and other transient devices even when they aren't connected to your local network.
How does it all work?
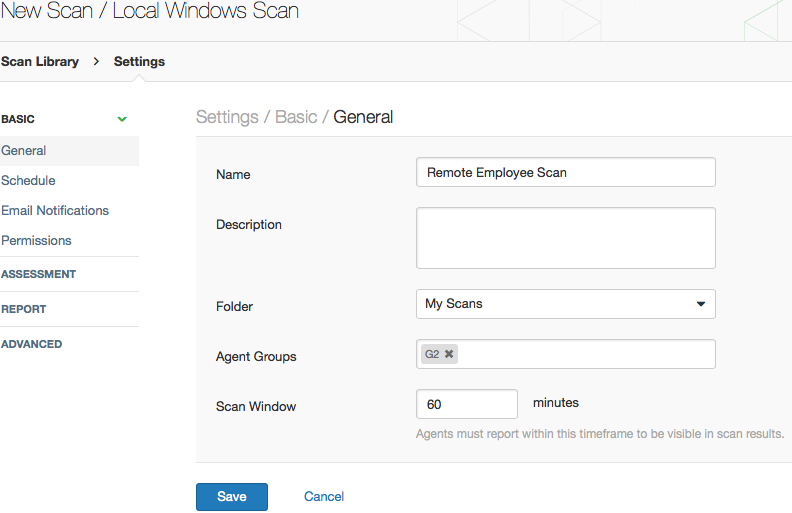
At a high level, starting an agent-based scan will look very familiar to existing Nessus users, with a few slight differences:
- Before you configure your first scan, you must deploy Nessus Agents. Agents are packaged as .msi files, so you can run them from a command line to deploy them manually or use a software management system or scripts.
- Once you've deployed an agent, you'll select a template from the new Agents section of the Scan Library. Instead of selecting a scanner specifying targets as you typically do with Nessus, you'll see an option to select groups of agents to serve as targets for the scan.
- Specify how long a scan is to run; this is the window of time in which targeted agents can check in and upload their results for a particular scan.
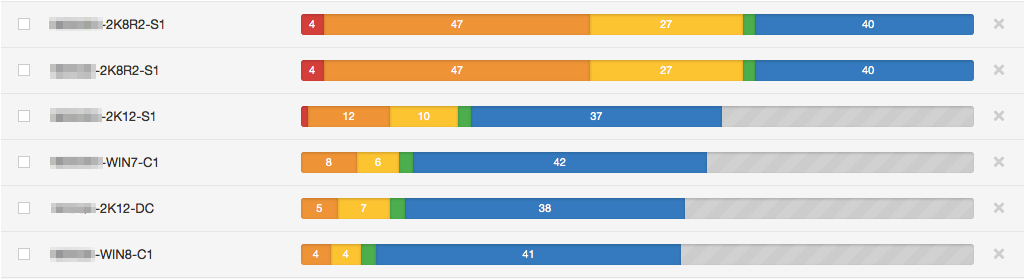
- When the agent connects during the specified window of time, it reports results to the Nessus Manager. An example is shown below. If for some reason an agent cannot connect to the Nessus Manager within the defined window (e.g., an employee is on vacation and hasn't turned on the laptop for a week), it is treated the same way that an offline host would be in a traditional network scan, and doesn't appear in the results.
Nessus Agents are currently supported on 32-bit and 64-bit editions of Windows platforms (excluding Windows XP and Windows Server 2003). Support for additional platforms is planned.
Timing
Nessus Agents will initially be available in the new Nessus Manager, scheduled to release in early March. Support for Nessus Agents in additional Tenable products is also planned.
Resources
If you'd like to learn more about Nessus Agents, the following resources are helpful. Or contact Tenable or one of our many partners.
The Nessus product line
Nessus® Manager 6.3 is the newest member of the Nessus product line. Nessus Manager combines the powerful detection, scanning, and auditing features of Nessus, the world's most widely deployed vulnerability scanner, with extensive management and collaboration functions to reduce your attack surface and eliminate vulnerability blind spots. Nessus Manager enables the sharing of resources including multiple Nessus scanners, scan schedules, policies, and results among multiple users or groups.
Nessus Manager replaces Nessus Enterprise; at renewal time, existing Nessus Enterprise customers can upgrade to Nessus Manager at no additional charge.
Current Nessus customers can update their deployments from the Tenable Support Portal and find answers to common questions in the Nessus FAQ. New customers can download a trial version of Nessus 6.3 from the Nessus Download page.
Nessus is now referred to as Nessus Professional, the single-user vulnerability scanning tool. Nessus Enterprise is replaced by Nessus Manager. Nessus Enterprise Cloud is now replaced by Nessus Cloud.
Nessus, the industry's most widely deployed vulnerability scanner, helps you reduce your organization's attack surface and ensures compliance in physical, virtual, mobile, and cloud environments. Nessus features high-speed asset discovery, configuration auditing, target profiling, malware detection, sensitive data discovery, and vulnerability analysis. With the world's largest continuously-updated library of vulnerability and configuration checks, and the support of Tenable's expert vulnerability research team, Nessus sets the standard for speed and accuracy. You can learn more about Nessus on the Nessus homepage.
Learn more
- Announcements
- Nessus
- Tenable Vulnerability Management (DO NOT USE)
- Vulnerability Management
- Vulnerability Scanning




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success