Security Implications of Infrastructure Modernization

As oil and gas facilities face increasing pressure to improve production and minimize extraction and refining costs, modernization of sites and systems is inevitable.
The adoption of new technologies in oil and gas facilities is a dual-edged sword.
On one side, there are obvious benefits of implementing industrial internet of things (IIoT) devices to improve efficiencies and reduce operational costs.
On the other, there are inherent risks associated with system upgrades.
Case in point: the Columbia Gas incident in metropolitan Boston in 2018, which produced a series of explosions in Andover, North Andover and Lawrence, Massachusetts. The incident resulted in more than 70 fires, one death, dozens of injuries, 30,000 people evacuated and the destruction or damage of more than 100 structures. About 9,000 customers were left without power.
The New York Times reported that a system upgrade caused gauges that monitor pressure levels to go offline. Unchecked over-pressurization triggered the blasts.
While human error can cause incidents like the one for Columbia Gas, similar incidents could just as easily become the work of terrorists.
Oil and gas executives are acutely aware that once-isolated operational technology (OT) networks charged with refining, mixing and distributing petroleum are increasingly connected to the “outside world” via the industrial internet of things (IIoT).
In addition, modernization inevitably involves some degree of digital transformation, which exposes facilities to more security threats than ever before.
Attacks such as BlackEnergy, Industroyer, VPNFilter and Wannacry are just a few of the malware campaigns that have affected critical infrastructures. The actors in some cases were rogue factions, including nation states, that hacked into industrial networks and caused havoc.
However, the threat from within is also omnipresent and highly significant. Insiders have “the keys to the kingdom” or at least know how to find them.
The IIoT threat
The internet of things (IoT) and IIoT show tremendous promise for improving oil and gas operations.
Increasingly, companies are investing in the cost saving and productivity enhancing benefits of networked smart devices, which can communicate and coordinate with one another via the internet.
The IIoT downside? Few vendors and customers have fully considered security risks associated with the technology.
The introduction of new access points into your company’s network, plus the current lack of security standards for IoT devices, can create holes for punching through perimeter defenses.
However, the planned or (worst-case scenario) unplanned introduction of IIoT devices into your enterprise network creates opportunities for a host of external and internal threat actors, including:
- Terrorists acting alone, independent of an organization or group, or someone incited by an organization or group.
- State-sponsored adversaries acting on behalf of a government, whose activities can span computer-based and physical attacks.
- External cyberattacks caused by hacktivists to promote a political agenda or a social cause.
- Internal attacks created by malicious insiders, such as a disgruntled employee or third-party contractor who is paid to exfiltrate information and/or cause damage to your organization.
- Unintentional mistakes due to human error that cause damage and/or downtime because of incorrect changes to industrial processes or equipment.
Yet another variation — account compromise — resembles an insider attack since it occurs when an external attacker hijacks an authorized user’s account (employee, vendor, integrator, etc.). These are typically achieved using social engineering techniques such as phishing emails and or a “call from the IT department” requesting the user’s ID and password.
Three top security risks in industrial networks
Below are three of the top security risks facing industrial organizations today:
- Default passwords. IIoT manufacturers can pre-configure devices with a default password, which is a time-saver for IT staff. However, this benefit is also a major security flaw. When hundreds of thousands of devices share the same default passwords, attackers can easily compromise organizations that neglect or intentionally decide not to change them.
- Missing patches. Many IIoT devices cannot be patched or vendors do not issue patches for known vulnerabilities, so missing patches are another huge problem for organizations.
- Too many devices to manage. Most organizations have endless IIoT device lists that extend beyond traditional OT to include alarm systems, cameras, thermostats, vending machines, etc. Even an apparently harmless device can pose a threat. For example, you should never connect an IoT coffeemaker to your IT or OT network, since the machine has no security features.
Regardless of the IIoT device type, attackers can use any or all of them as stepping stones to compromise your IT and OT networks.
For example, many IIoT devices have exposed internet ports, which attackers can use to bypass your firewall. Once inside your network, a hacker can do extensive damage to IT and OT infrastructures and move laterally between them. Think data breaches, viruses, ransomware, sabotage and data exfiltration.
Three key defense measures
Protecting refining, petrochemical and distribution networks from insider and outsider threats involves the following three best practices:
- Asset management. Identify and map all devices in your OT environment to keep an up-to-date inventory of them — even of those that aren’t actively communicating over your network. Some software can collect granular information on each device, including firmware versions, PLC backplane configurations and serial numbers.
- Risk and vulnerability assessment. There are many potential attack vectors to defend, so it’s best to focus on your greatest sources of risks and vulnerabilities. This involves automating processes you use to identify and address new vulnerabilities. A vulnerability management system can generate periodic reports of risk levels for each asset in your industrial control system (ICS) network. When the system discovers new vulnerabilities (or when new vulnerabilities are disclosed) you should have a mechanism in place to identify affected devices, remediate threats and verify when your team successfully applies a fix.
- Device and configuration management. Monitor and manage changes in your ICS environment to ensure that device and system configurations are secure and well-documented. This requires maintaining a continuously updated list of version numbers of all installed software and firmware, which you should regularly compare against a list of known vulnerabilities.
Meanwhile, regular OT network scanning can detect unknown devices and unintended changes.
The best solutions issue notifications whenever a new vulnerability appears. They also combine network monitoring with device queries to provide in-depth vulnerability assessments. For example, they provide information on current device firmware versions and associated CVEs, list open ports and calculate accurate, up-to-date risks.
You should also enforce security policies to control which devices can perform certain (privileged) actions, such as code or firmware downloads to industrial controllers. Additionally, policies should mandate that certain devices do not access the internet.
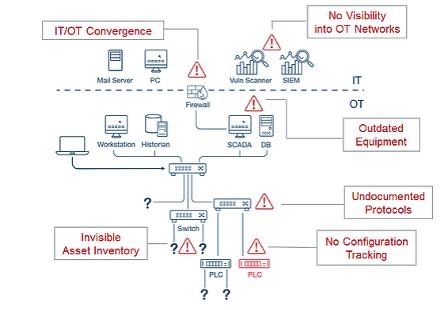
Unifying IT and OT security
With more pressure to increase production and minimize extraction and refining costs, sites and system modernization is inevitable. Meanwhile, it’s necessary to extend the life of mature sites to maintain supply levels, since developing new sources — as well as extraction, transportation, and refining infrastructure — are more costly and complex alternatives.
As a result, monitoring control systems and processes for unintended changes — whether they are the result of malicious attacks or human error — is central to preventing shutdowns. This is an important beneficial byproduct of implementing your OT security program.
In addition to these market pressures, the oil and gas sector must also comply with stringent environmental regulations and standards that cover production, extraction and distribution processes. Here again, active monitoring of OT networks, devices and activity can help detect and prevent problems before they lead to environmental incidents.
One way to combat the broader attack surface created by modernization initiatives — and to mitigate the threat to production and environmental control systems posed by cyber incidents and human error — is to converge IT and OT security groups. While challenging, such collaboration can mitigate those risks and vulnerabilities which span these two infrastructures, simultaneously facilitating implementation of security best practices.
Learn more
Download the white paper, Mind the Gap: A Roadmap to IT/OT Alignment, for more insight into how to address the expanding cyberattack surface in industrial networks.
Learn more
- SCADA




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success