SANS ICS Summit 2014 Conference

Hold Me, I'm Scared
I've been in the security community for quite some time (15+ years in fact). And while that's not world record, I have heard more than my fair share of security horror stories. Everything from crashing entire server farms to wiping out email for large organizations, and those are just my own horror stories. I knew there was a gap between security and the ICS world, but it goes deeper than that. Devices, systems and software we label "control systems" have a lot of responsibility. They run the electrical grid, water supplies, and oil supplies of the world. And while strides have been made to improve ICS security, we still have a ways to go. Conferences such as this one, well attended by those responsible for security in ICS/SCADA environments, itself is comforting.
Unique Challenges
While I had always heard the argument that ICS were different from traditional IT systems, I may not have realized how different. Below are some really good reasons for the differences:
- Systems are meant to last longer - If you are sitting in a room with IT professionals, ask them how old their laptops are. Chances are the answers will ranges from less than a year to maybe 3 years max. And the ones that answer 3 years admit they are LONG overdue for a new one (if more than 3 years, it may end up like the scene in the TV commercial where the guy purposely spills an entire cup of coffee on his laptop, in hopes on getting a new one!). In the ICS world, equipment is expected to last much longer, 10 years or more. For example, smart meters.
- Systems are designed to trust the network - If we think about how long some of the industries that are using ICS systems have been around, it far pre-dates the Internet. Many of the systems, and resulting culture, are designed and deployed with complete trust for their environment. They were installed in a secure location and accessed only by operators that were in the circle of trust. However, with the evolution of technology and the Internet evolved, the circle of trust goes right out the window. Most SCADA devices today are connected to some sort of network, wireless or wired, that may also be connected to the Internet. While there are true air-gapped networks (and/or systems that are not even communicating over Ethernet), there are several situations where attackers can find SCADA devices to compromise.
- The protocols are numerous and often missing security - When you get hit with the alphabet soup of ICS-related protocols, it can make your head spin. These include Modbus, DNP3, S7 and many more. Many controls systems consumers and vendors will also implement their own specialty protocols as well. With all of the available protocols, it is difficult to implement a security standard. Modbus is the most popular and suffers from lack of authentication.
- Patching - Of course, those in the ICS world are especially sensitive to the negative aspects of patching. That is, applying patches could have grave consequences for the wellbeing of humans (this is yet another aspect that separated ICS from IT: its not just a printer that will malfunction, people could cease to function as a result of patching). The other concerning factor is when it comes to embedded systems and firmware updates. While many have high expectations for firmware updates, "oh, just update the firmware" the say, it’s not that simple. Don't forget, updating the firmware likely entails replacing the kernel, operating system, and file system.
Security: A Balanced Diet
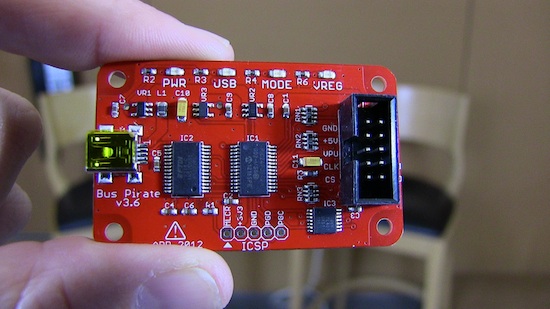
- Protect the hardware - Restricting physical access, and the devices in facilities, is key. So much of what we wear has wireless communications, such as Bluetooth, which can cause system interference or can be used as a catalyst to disrupt or compromise systems. Also, the devices themselves should be restricted as much as possible, and make it difficult for attackers to acquire the hardware and perform analysis. Of course, no matter how hard you try, hardware will fall into the wrong hands, and once an attacker has physical access, there is little that can be done to stop them.
- Protect the firmware - While it’s difficult to implement full AES encryption on many embedded systems, it’s not impossible. This choice is primarily on the vendors, and you as the consumer should gravitate towards more secure solutions. Some devices are just too small and do not have the computing resources. However, Moore's law and all, smaller computers are becoming more powerful, which means we must consider encryption to protect firmware (and more specifically the boot loader).
- Securing the Protocol - Encryption and authentication must be present in the communications protocols. Many of the protocols in use by SCADA systems are not implementing encryption, though Secure DNP3 has been around since 2007. Modbus, for example, is a stateless protocol which does not offer encryption. Modbus assumes you are on a secure network and allows anyone on the network to change values that affect the device (Coils are binary, e.g. turn something on or off and Registers are integers, e.g change the temperature).
- Trust No One - Many of the systems and devices used to support the ICS community, and used in several SCADA systems, are designed to inherently trust their environment. While this may have been okay 15+ years ago, I learned that nothing is truly air gapped and the mindset of trust needs to change. Devices must be hardened to a certain level in order to protect themselves from multiple types of threats, including cyber-attacks that may occur on the inside and outside of the network.
- Stop, Collaborate and Listen - There has been a significant improvement over the past few years in the ICS community surrounding security. The ICS community has some challenges working with operations folks who put a high level of importance on availability, often at the sacrifice of security. However, security awareness of the ICS community is improving, and several methods and techniques from IT security are being implemented by ICS groups in our control systems environments, albeit slowly. Conferences such as the SANS ICS Summit are a step in the right direction.
We're Here to Help
I presented to the audience several great tips and techniques to use Tenable products in controls systems environments, including using the Passive Vulnerability Scanner. Tenable's PVS can enumerate vulnerabilities without impacting the targets as it relies on sniffing the network rather than sending packets. PVS also contains hundreds of signatures for SCADA devices, protocols and vulnerabilities. The Nessus vulnerability scanner can perform credentialed patch and configuration audits for a low impact, high result yield scanning process. Nessus also contains hundreds of signatures for SCADA-related vulnerabilities, and supports the Modbus protocol enumerating coils and registers and putting that information in the results. Tenable's enterprise products such as SecurityCenter and LCE can be used to collect more information, such as logs and vulnerabilities found in your logs as a completely passive way of both new host and vulnerability discovers. Finally, you can tie it all together with SCADA-related SecurityCenter pre-canned dashboards.
This was a fantastic conference and training run by the SANS Institute, can't wait to do it again!
Learn more
- Conferences
- SCADA



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success