Tenable One OT Exposure
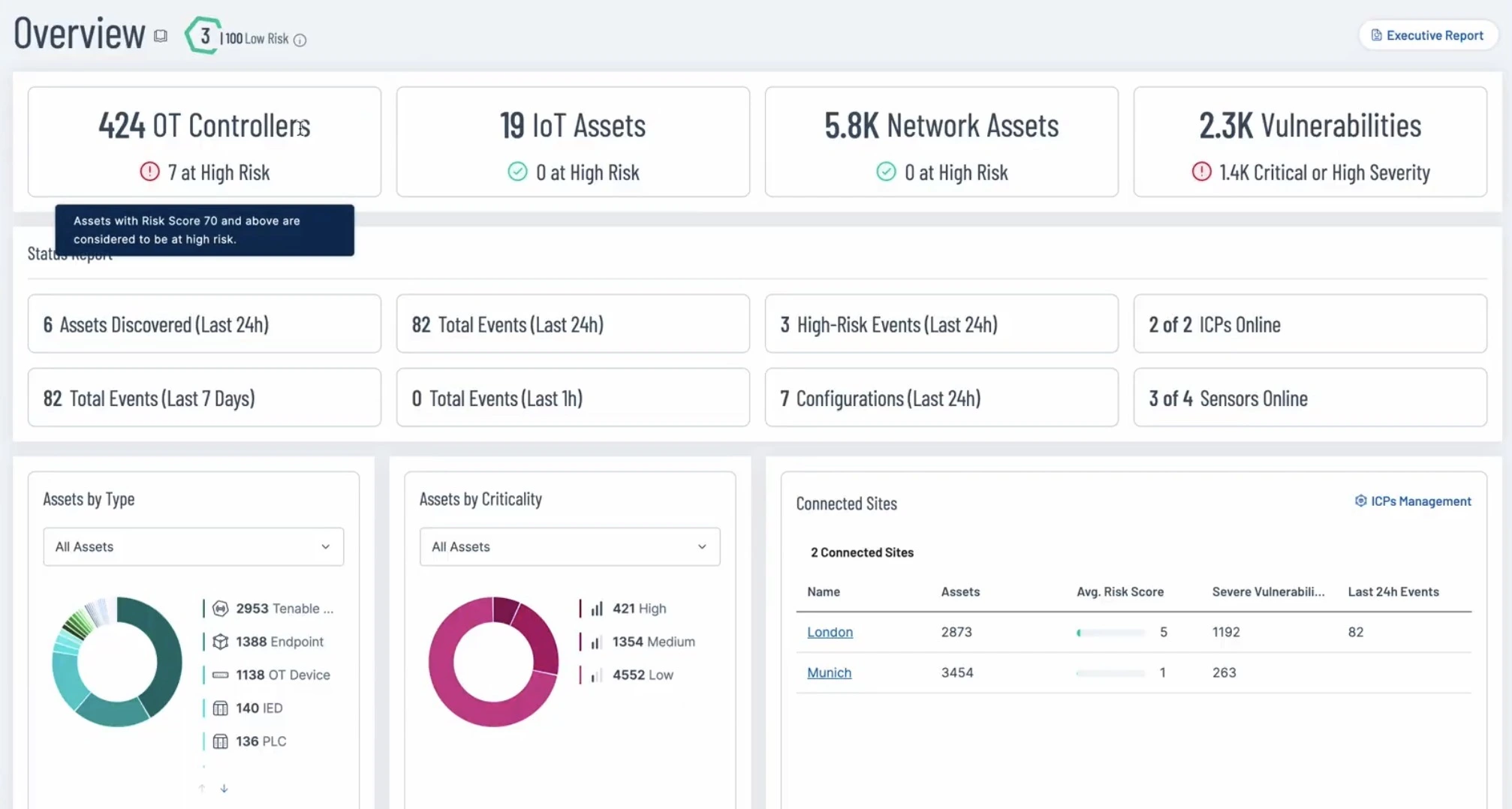
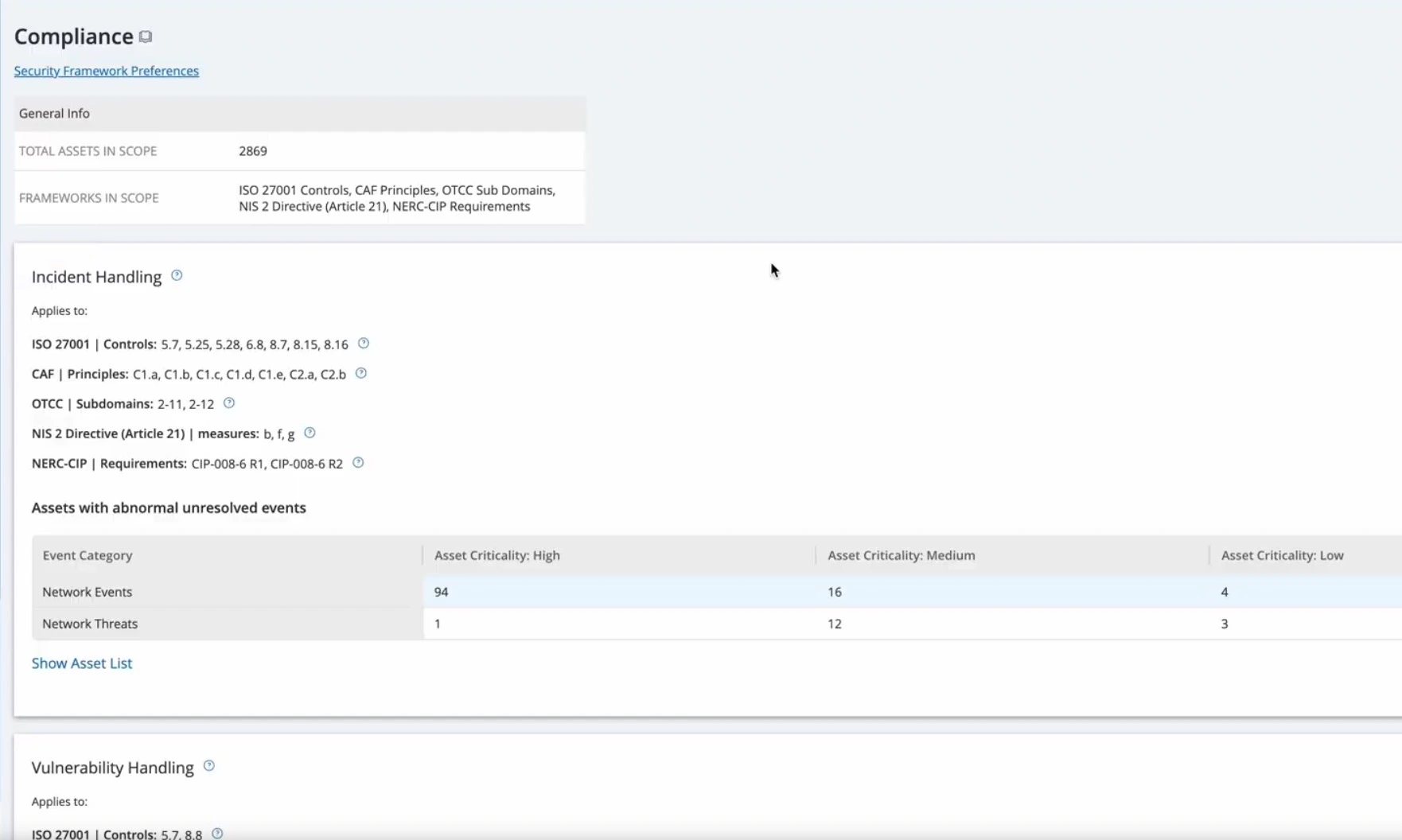
Stop reacting to fragmented alerts and start managing OT security across your entire cyber-physical ecosystem. Unify your digital and physical attack surface with Tenable One OT Exposure. Combine deep visibility with industry-leading exposure intelligence to protect critical infrastructure without disrupting innovation and operations.
The world’s #1 exposure management platform for converged OT/IT environments
Get comprehensive protection for cyber-physical systems (CPS)
Secure your operational environment and mission-critical infrastructure with a purpose-built platform for CPS security.

tenable one
The world’s only AI-powered exposure management platform
Tenable One reduces cyber risk by unifying security visibility, insight and action across the entire attack surface, helping organizations quickly find and fix critical weaknesses.
See why customers choose Tenable One for OT security
OT security FAQs
Find answers to common questions about Tenable One OT Exposure.
-
How does Tenable One OT Exposure discover assets without disrupting operations?
-
Tenable One OT Exposure uses a "do-no-harm" approach, combining passive network monitoring with patented, vendor-approved Safe Active Querying to communicate with devices in their native protocols.
-
Does Tenable support air-gapped environments?
-
Yes. Tenable offers flexible deployment models to meet specific security and cybersecurity compliance needs:
- Cloud: For rapid scalability, continuous updates, and access to global threat intelligence from Tenable Research.
- On-premises: For full local control, ideal for highly regulated or air-gapped OT networks.
- Hybrid: A flexible combination that supports global, distributed operations with varying regional requirements.
-
What is the difference between VPR and standard CVSS scores?
-
CVSS measures theoretical severity, while Tenable’s Vulnerability Priority Rating (VPR) uses data science to measure real-world exploitability, helping you focus on the most dangerous threats first.
-
Can Tenable One OT Exposure scale to global operations and multi-site OT environments?
-
Yes. Tenable One scales with the complexity of global enterprises and distributed operational facilities. The Tenable cloud-native platform provides centralized visibility with local context to ensure consistent security policy and governance across all your plants, regions, and industrial networks.
-
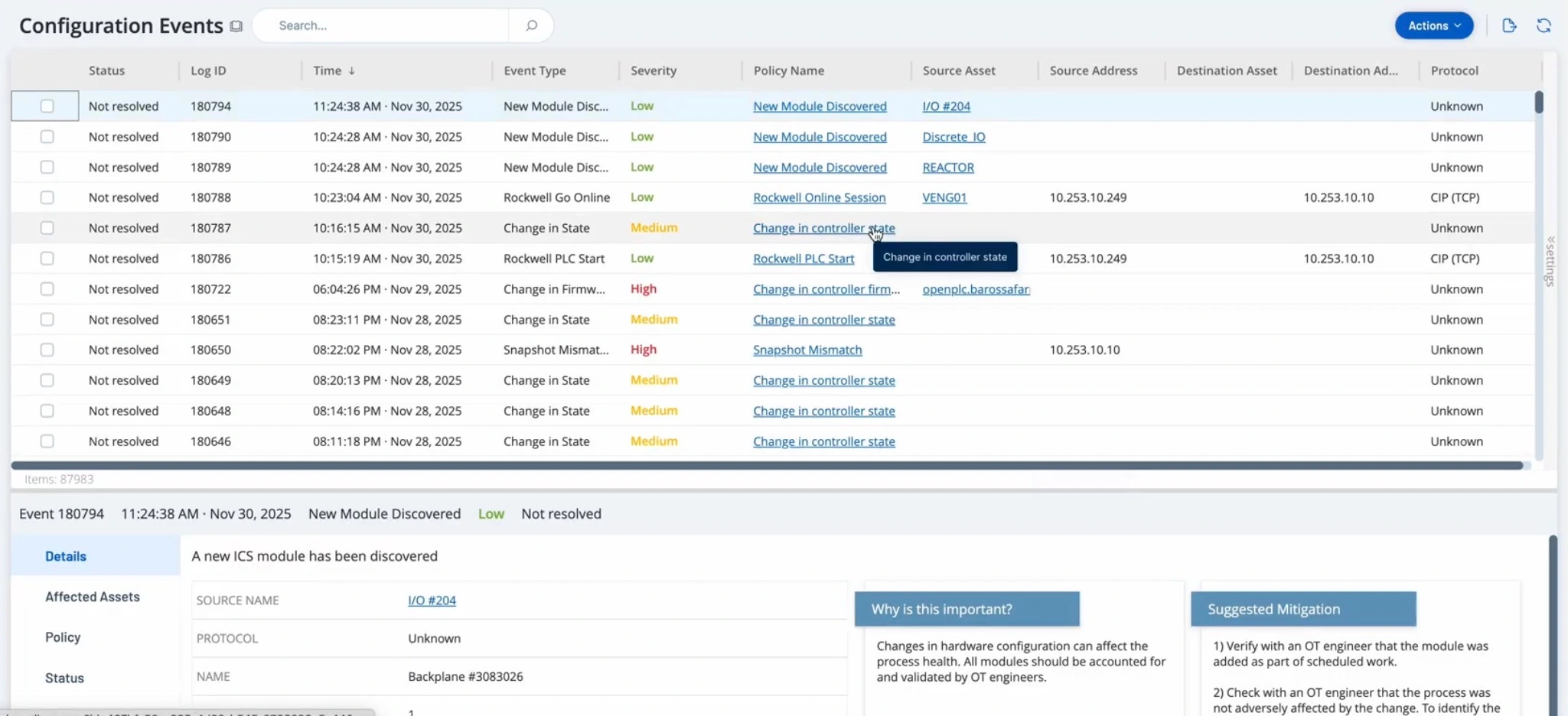
What automated actions can Tenable One OT Exposure take in response to OT threats?
-
Tenable One integrates with your existing security and network infrastructure to enable automated, real-time threat response. Through these integrations, the Tenable exposure management platform can trigger actions such as:
- Blocking malicious communications by updating firewall rules.
- Opening a high-priority ticket in JIRA or ServiceNow with all relevant context.
- Automatically initiating a specific workflow in your SOAR platform.
-
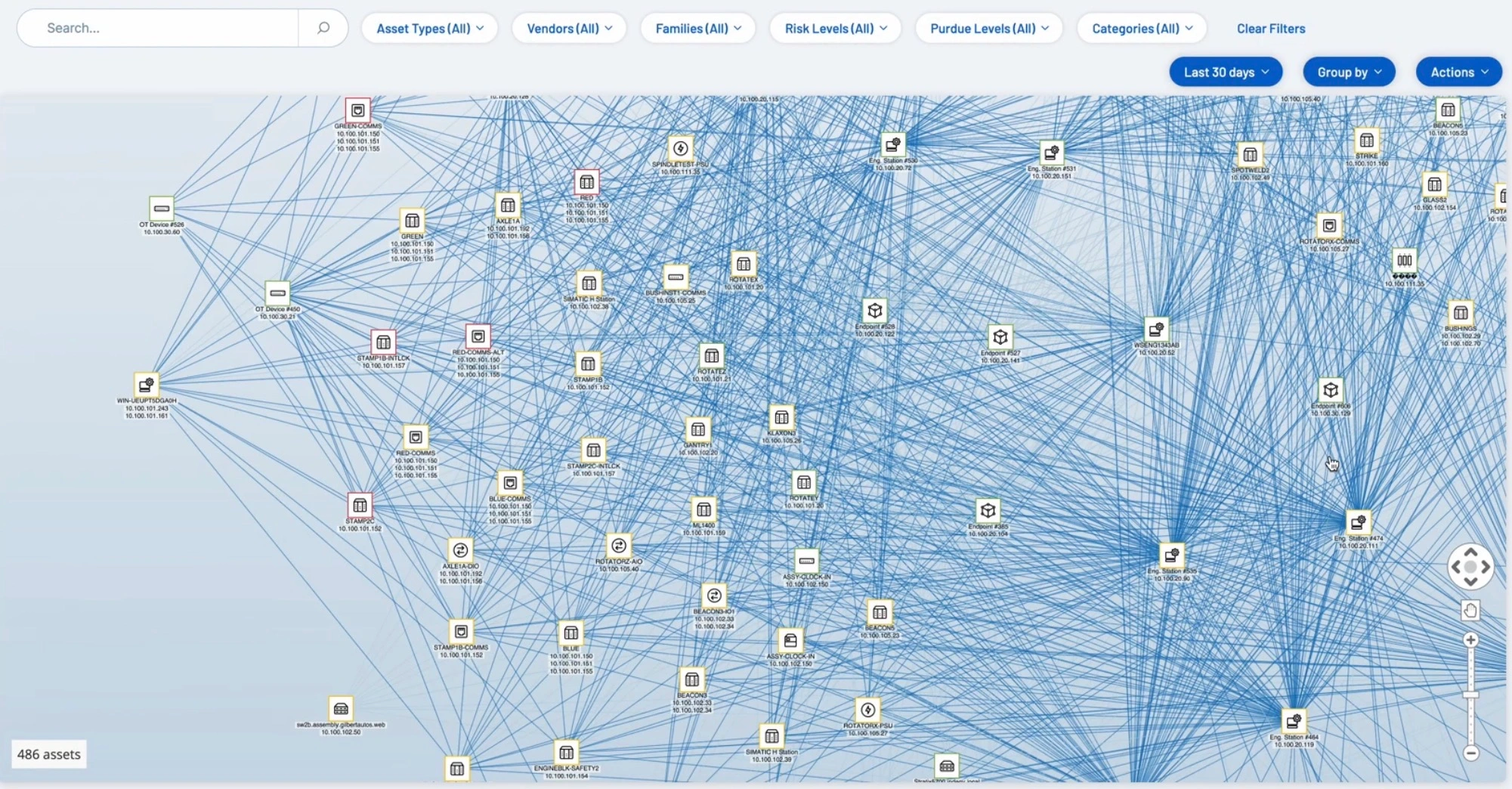
How does Tenable One discover unmanaged, unknown, or shadow OT assets?
-
Tenable One OT Exposure excels at finding every asset in your environment, including legacy, unmanaged, or rogue devices that other tools miss. Tenable One OT Exposure combines powerful discovery methods:
- Continuous traffic monitoring by analyzing network traffic to see every device as it communicates.
- Safe Active Queries using native industrial protocols to accurately identify and classify devices without disrupting sensitive processes.
- File imports and interoperability that support the ability to manually import SCD and ACD files, CSV spreadsheet files, PLC project files, and other commonly used file formats to enrich your security data.


Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success