Detecting Credit Cards, SSNs and other Sensitive Data on UNIX/Linux Systems
Nessus, Nessus Enterprise and Nessus Enterprise Cloud users can now remotely scan UNIX and Linux systems for the presence of sensitive information such as credit/debit card numbers, SSNs, company confidential information, and more.
What Can I Discover?
New configuration auditing capabilities have been added for Nessus users to remotely check UNIX and Linux systems for the presence of sensitive information. This capability has been available on Windows systems for some time; you can refer to the blog post titled "Detecting Credit Cards, SSNs and other Sensitive Data at rest with Nessus" for additional information. The Windows sensitive file content checks have been re-created for UNIX/Linux systems, which include the ability to detect:
- Credit/Debit card numbers (VISA, Mastercard, American Express, and a generic check)
- PII such as Social Security Numbers (including US and international), EDI health claim numbers, drivers license numbers, and Employee Identification Number (EIN)
- Adult content
- Company confidential information (Payroll, NDA, source code, wire transfer information, generic confidential information, financial statements)
PCI Compliance
Credit/debit card information stored in clear-text on remote systems is valuable information to attackers and indicates failure in accordance with the Payment Card Industry Data Security Standard. Primary Account Numbers (or PANs) must be securely deleted or protected according to the requirement set forth in the PCI DSS.
The PCI DSS states that the first step in the compliance process is to validate cardholder data flows and storage areas to accurately determine the systems that are in scope for PCI compliance. Cardholder data may not be stored in a readable format, so being able to identify storage locations of cardholder data is key.
Configuration & Features
Nessus now supports the following:
- Cross-platform support including Red Hat/CentOS, SunOS, AIX, HP-UX, Mac OS X, BSD
- LUHN support - LUHN is the formula used to determine if a credit card number if valid or not. Credit cards numbers not verified by the LUHN algorithm are typically not of interest, so Nessus can now ignore non-valid credit card numbers.
- Current checks support file types of PDF, DOC, XLS, and more. This list is customizable by the Nessus user.
In order to run a scan for sensitive data against UNIX and Linux targets, you will need the following:
- Root-level privileges on the remote host and SSH access to the targets (for instructions on setting up credentialed scanning, please refer to the document Nessus Credential Checks for Unix and Windows).
- Activation of Plugin ID #72095 (Unix File Contents Compliance Checks).
- One (or more) of the new audit files in the new UNIX/Linux Sensitive Content Audit category", which can be downloaded from the Tenable Support Portal.
- New Feature: Optionally, you are able to turn on/off the setting to check for a valid LUHN test. Setting the LUHN value in the audit file to “YES” tells Nessus to only report credit card numbers that are LUHN verified. LUHN checking is also now available in the Windows Sensitive Content Auditing checks.
The results for the new UNIX sensitive content auditing checks, specifically looking for cardholder data, are as follows (click for a larger image and to see both a passed and failed result):
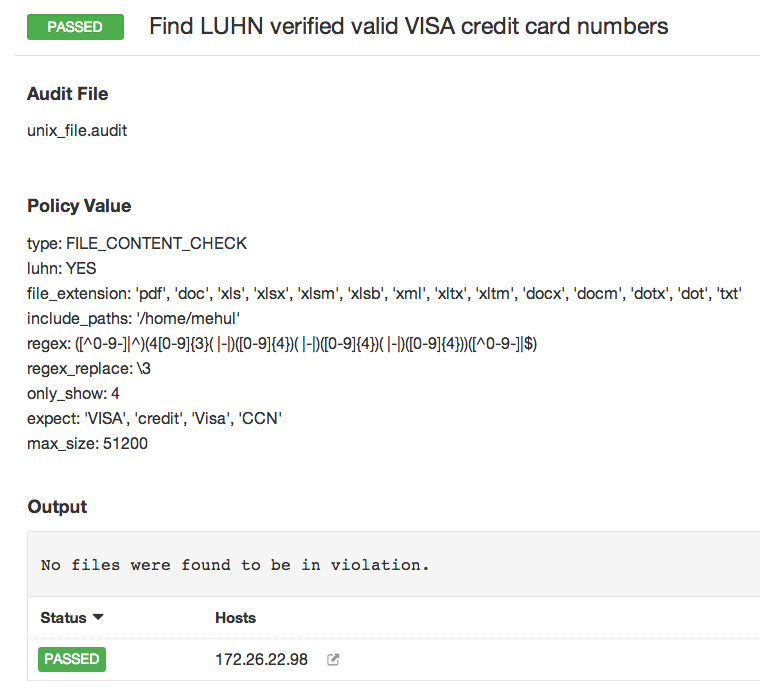
Click for larger image
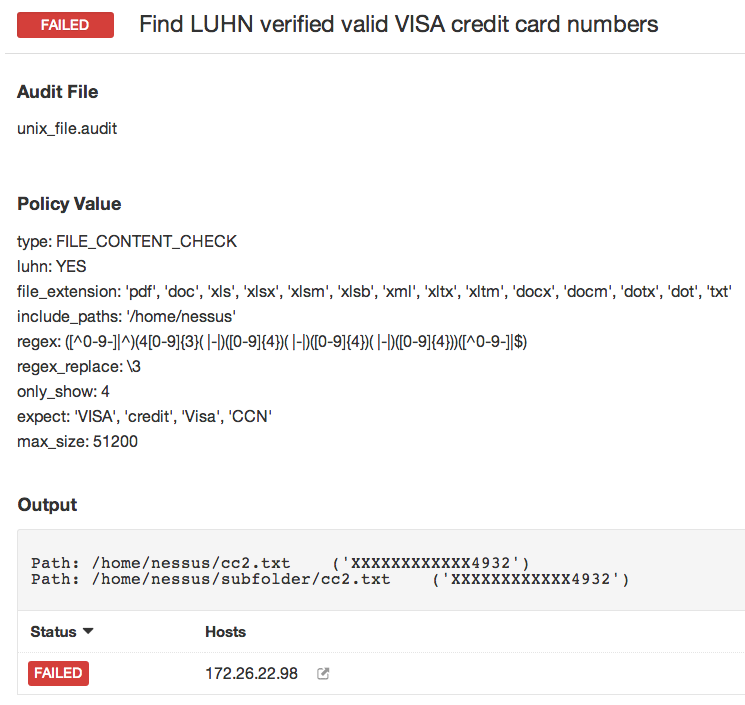
Click for larger image
Checking for PII (Personal Identifiable Information)
Many organizations face challenges when they are required they store and protect PII such as Social Security Numbers. Several US states have put laws in place to help safeguard this information. Despite these regulations, breaches involving Social Security Numbers are still occurring, including a large one last month where 50,000 full and partial SSNs were stolen as a result of a breach at Arkansas State University. Continuously monitoring your systems for the presence of PII, such as Social Security Numbers, is important and Nessus can be used to discover such cases, as shown below:
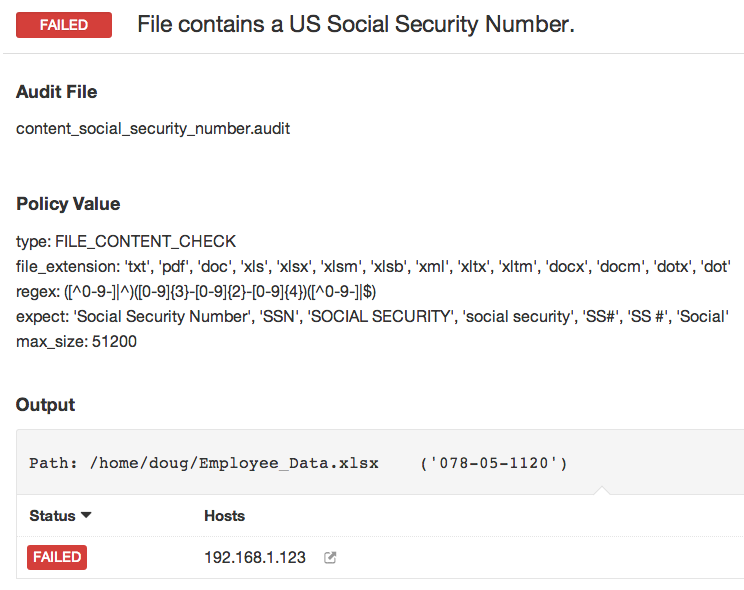
Click for larger image
For more information about this feature, please refer to the Tenable Discussions Forum entry that contains more technical details about the checks themselves. Tenable customers can go to the Tenable Support Portal and download the new audit file, which can be implemented in all Nessus and SecurityCenter products.
Learn more
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success