Auditing Red Hat Enterprise Virtualization (RHEV) with Nessus v6
There was a time in early 2000 when the word "virtualization" was synonymous with VMware, and rightly so. After all, VMware started the second coming of this revolutionary technology after IBM. But open source hypervisor solutions such as Xen and KVM have been slowly nibbling at this market share and have made names for themselves in the past decade. Today, it is not uncommon to see multi-hypervisor deployments in a typical data center.
Over time, virtualization technology has matured, and the hypervisors that form the basis of this technology have become feature rich. For basic tasks such as managing virtual machine life cycles or live migration, most major hypervisors are on par with the rest. But as technology essentially becomes a commodity, it’s normal for end users to try out cheaper alternatives to migrate either their existing virtual infrastructure or when building a new one. This is especially true for use cases that are not mission critical (low end quality assurance/development environments) and where an SLA drop from 99.99% to 99% doesn't trigger heartburn. Red Hat Enterprise Virtualization (RHEV), based on KVM, is precisely that solution with enterprise level support.
Nessus support for hypervisors
Tenable has offered solutions to audit virtual infrastructure for quite some time. We first added support for VMware vSphere/vCenter more than a year ago and followed it up by adding support for Citrix XenServer. And through support for WMI/PowerShell calls in an .audit file, Nessus customers could always run audits against Microsoft Hyper-V. Of the four major hypervisors, KVM was the only hypervisor that eluded us so far.
Nessus v6 supports auditing RHEV, the Red Hat Enterprise Virtualization product based on the KVM hypervisor
With the release of Nessus v6, Tenable has added support for auditing RHEV, which is an enterprise virtualization product produced by Red Hat, based on the KVM hypervisor. The product is based on the oVirt project, which is its free, bleeding edge twin.
The TNS RHEV Audit
The TNS Red Hat Enterprise Virtualization (RHEV) Audit taps into the RHEV API via the RHEV-Manager (RHEV-M), and reports comprehensive information that you may want to know about your RHEV setup in a Nessus report. For example, details include the list of users, running VMs, and stopped VMs across one or more RHEV-Hosts managed by RHEV-M. Admittedly, calling this audit a best practice audit would be a stretch, but calling it a connector is appropriate. The reason is because the APIs don't expose the same level of detail that you would expect from similar competing vendors such as VMware and Microsoft, and there isn't a best practice guide for RHEV from Red Hat either. Also, ssh access is disabled to the RHEV-Host, which limits the ability to audit.
If you are an RHEV/oVirt product manager reading this post, my humble call to action is for you to release a best practice guide for RHEV. Most enterprises won't touch a technology if it doesn’t meet their specific compliance standards, and if there is no way to audit the technology, that deployment will likely not happen.
Nessus supports calling any API action via an .audit exposed by RHEV-M under:
https://rhev-m-target/ovirt-engine/api
and then includes results from those calls in a Nessus report.
Sample results
For example, here is a check that reports on all virtual machines:
<custom_item>
description : "RHEV: VMs"
request : "/api/vms"
</custom_item>You can also run queries for API actions that support searches. For example, the following query runs a search for VMs that are up and running:
<custom_item>
description : "RHEV: Running VMs"
request : "/api/vms?search=status=up"
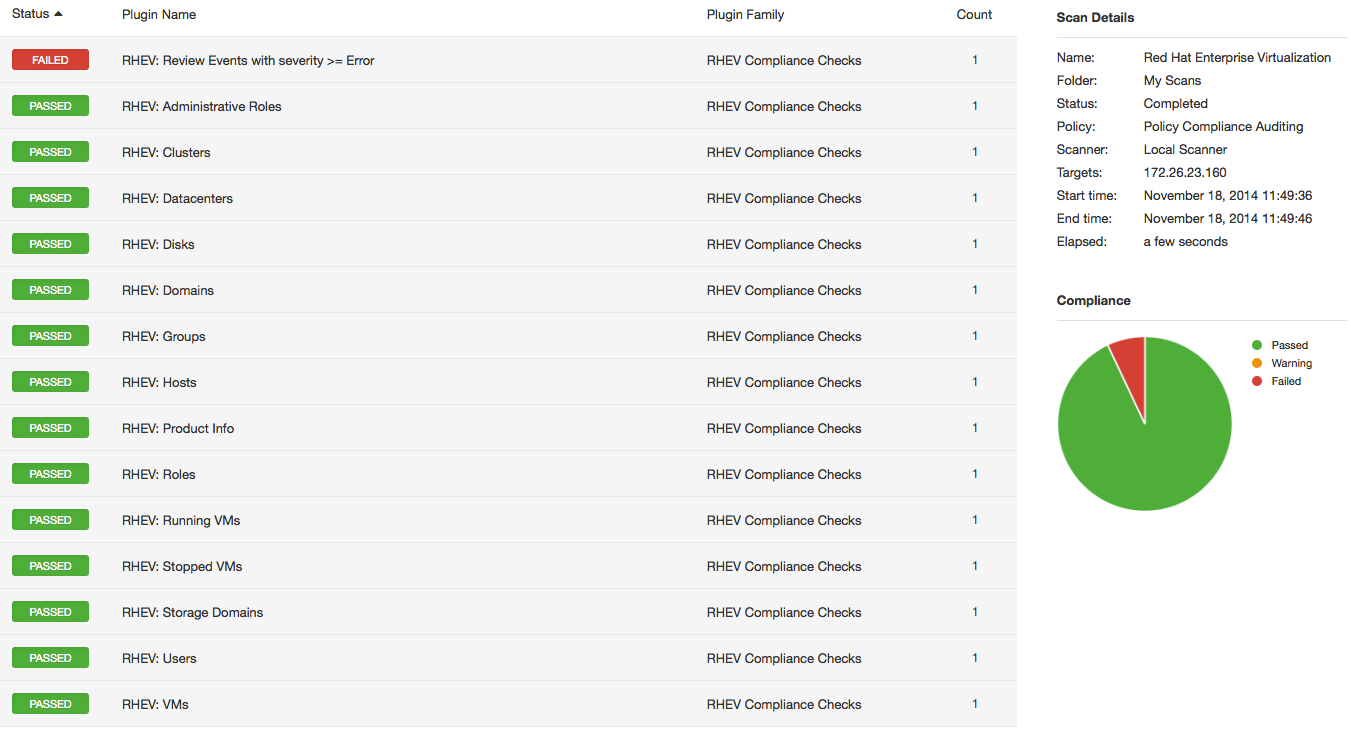
</custom_item>Here is a sample report from the RHEV audit:
For more technical details, check the Tenable Discussion Forum for RHEV audit posts.
Conclusion
With support for RHEV, Nessus has now added support for all major enterprise virtualization offerings. But we are not stopping there; we are keenly aware that next-generation enterprise applications will be built in either a private, public or a hybrid cloud, and so we have already added support for Amazon AWS. Our current lineup now supports both enterprise virtualization and next-generation cloud technologies, and we have a lot more to come. Watch for more updates in the Nessus feed.
Learn more
- Nessus
- Plugins
- Security auditing
- Virtualization



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success