by Stephanie Dunn
October 10, 2016
Vulnerable devices and applications on an organization's network pose a great risk to the organization. Vulnerabilities such as outdated software, susceptibility to buffer overflows, and risky enabled services are weaknesses in the network that could be exploited. These vulnerabilities could allow attackers to compromise the network and steal or destroy sensitive data.
The federal government relies heavily on external service providers and contractors to assist in carrying out a wide range of federal missions. Sensitive but unclassified federal information is routinely processed by, stored on, or transmitted through nonfederal information systems. Failing to properly protect this Controlled Unclassified Information (CUI) could impact the ability of the federal government to successfully carry out required missions and functions.
The National Institute of Standards and Technology (NIST) created Special Publication 800-171 "Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations" to provide recommended requirements for protecting the confidentiality of CUI. Federal agencies should use these requirements when establishing contracts and agreements with nonfederal entities that process, store, or transmit CUI.
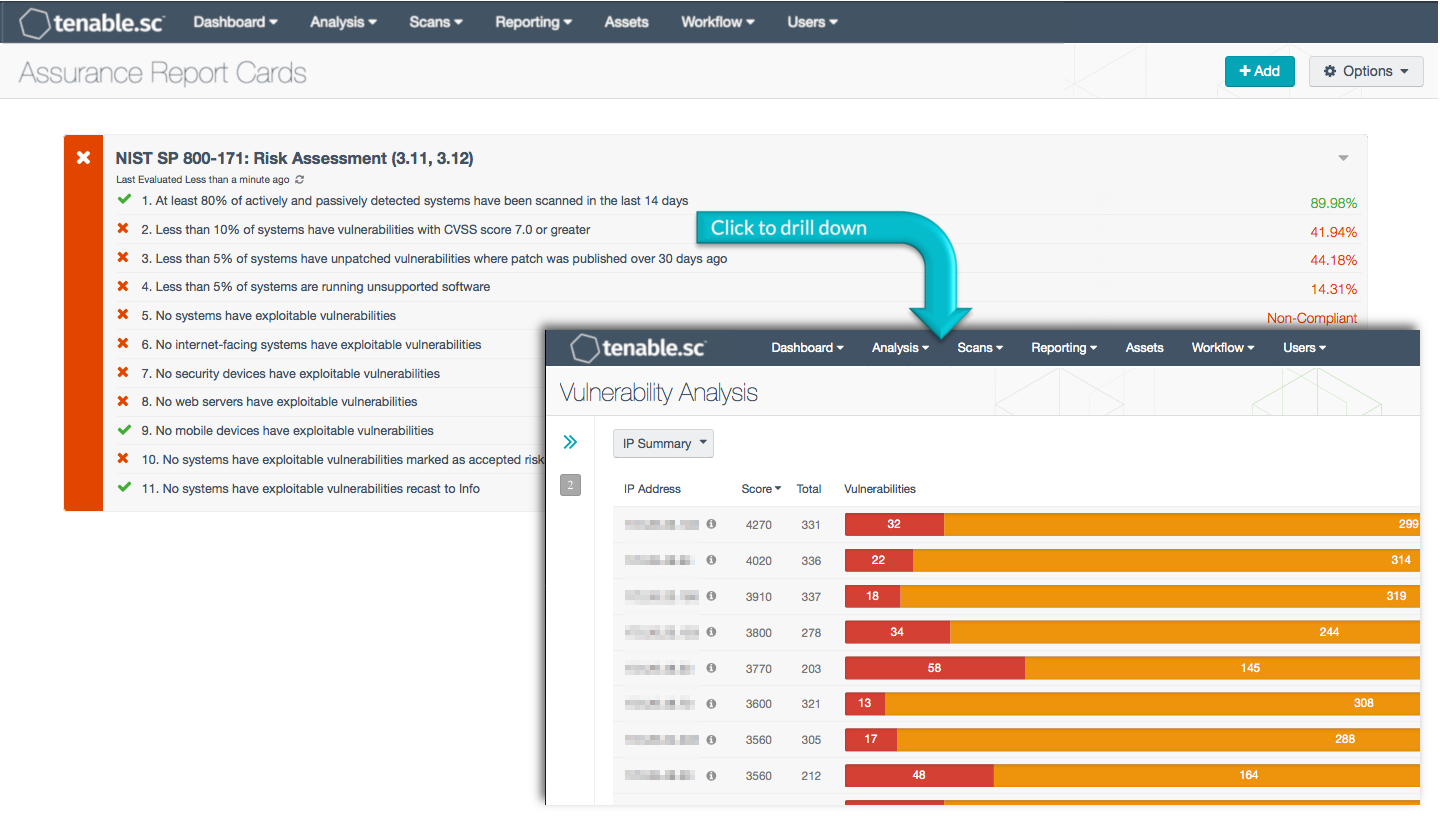
This Assurance Report Card (ARC) aligns with the Risk Assessment (section 3.11) and Security Assessment (section 3.12) families of security requirements in NIST SP 800-171. These families are closely related and focus on risk assessment and vulnerability management. Using this ARC, an organization will be better able to assess risk and identify and manage vulnerabilities. This information will assist the organization in securing their systems that process, store, or transmit CUI.
More details on each of the policy statements included in the ARC are given below. Clicking on a policy statement will bring up the analysis screen to display more details related to that policy statement. The ARC policy statement parameters are guides that can be customized as necessary to meet organizational requirements.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Tenable.sc Feed under the category Compliance. The ARC requirements are:
- Tenable 5.4.0
- Nessus 8.4.0
- LCE 6.0.0
- NNM 5.9.0
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in risk assessment and vulnerability management. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines hosts to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient devices. Passive listening collects data to continuously monitor traffic and discover additional vulnerabilities. Tenable.sc CV provides the organization with detailed vulnerability discovery and remediation tracking, in order to safeguard critical assets and sensitive information.
ARC Policy Statements
At least 80% of actively and passively detected systems have been scanned in the last 14 days: This policy statement displays the percentage of total systems that have been scanned in the last 14 days. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems on the network are detected both passively by the Tenable Nessus Network Monitor (NNM) and actively by Tenable Nessus. All systems should be actively scanned by Nessus to ensure that all current vulnerabilities are discovered and that remediation efforts are effective.
Less than 10% of systems have vulnerabilities with CVSS score 7.0 or greater: This policy statement displays the percentage of total systems that have vulnerabilities with CVSS score of 7.0 or greater. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. The Common Vulnerability Scoring System (CVSS) is an open industry standard for assessing the severity of computer system security vulnerabilities. The CVSS attempts to establish a measure of how much concern a vulnerability warrants, compared to other vulnerabilities, so efforts can be prioritized. The scores range from 0 to 10. Vulnerabilities with a base score in the range 7.0-10.0 are the most critical and should be patched.
Less than 5% of systems have unpatched vulnerabilities where patch was published over 30 days ago: This policy statement displays the percentage of total systems that have unpatched vulnerabilities with a patch published over 30 days ago. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Unpatched vulnerabilities can leave systems exposed to exploitation and should be patched within 30 days of patch publication.
Less than 5% of systems are running unsupported software: This policy statement displays the percentage of total systems that are running unsupported software. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This policy statement looks for unsupported software on a network, which can include outdated operating systems, applications, browsers, and other software. Unsupported software can be prone to vulnerabilities, which can present serious security risks for an organization. Some systems may not be capable of being patched due to lack of vendor support, end-of-life, or other business requirements. Unsupported software should be monitored regularly to determine whether software can and should be updated.
No systems have exploitable vulnerabilities: This policy statement displays non-compliant if any systems have exploitable vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems with exploitable vulnerabilities can expose the network to increased risk of malicious activity and should be patched.
No internet-facing systems have exploitable vulnerabilities: This policy statement displays non-compliant if any internet-facing systems have exploitable vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploitable vulnerabilities on internet-facing systems can leave the network exposed to malicious activity and need to be remediated.
No security devices have exploitable vulnerabilities: This policy statement displays non-compliant if any security devices have exploitable vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploitable vulnerabilities on security devices such as firewalls and VPN devices can expose the network to a high level of risk and should be remediated.
No web servers have exploitable vulnerabilities: This policy statement displays non-compliant if any web servers have exploitable vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploitable vulnerabilities on web servers expose the network to attack and should be remediated.