Using Security Metrics to Drive Action
We asked 33 security experts how they communicate security program effectiveness to business executives and the Board.
They share their recommendations and best practices in this ebook. If you’re a security professional, you’ll find their insights indispensable for helping you better communicate with business executives and Board members who often do not speak the security language. Download this ebook to learn about:
- Security Metrics That Tell a Story to the Board
- Security Metrics That Help Boards Assess Risk
- Security Metrics for Threat Management
- Security Metrics that Drive Action in the Financial Services Industry
Contributors include:
- Aanchal Gupta; Skype, Microsoft
- Aaron Weller; PricewaterhouseCoopers
- Adam Ely; Bluebox Security
- Andrew Storms; New Context
- Ben Rothke; Nettitude, Ltd.
- Charles Tholen; Cognoscape, LLC
- Chris Mark
- Daniel Riedel; New Context
- Dave Shackleford; Voodoo Security
- David MacLeod; Welltok
- Ed Adams; Security Innovation, Inc.
- Elena Kvochko; Barclays
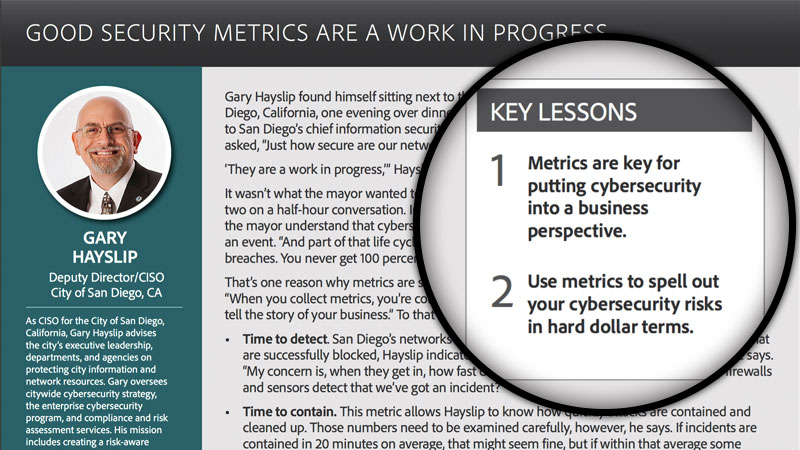
- Gary Hayslip; City of San Diego
- Genady Vishnevetsky; Stewart Title Guarantee Company
- J. Wolfgang Goerlich; CBI (Creative Breakthroughs, Inc.)
- Jake Kouns; Risk Based Security
- Jason Remillard; Deutsche Bank
- Jonathan Chow; Live Nation Entertainment
- Julian Waits; PivotPoint Risk Analytics
- Keyaan Williams; EC-Council
- Nikk Gilbert; ConocoPhillips
- Omkhar Arasaratnam; Deutsche Bank
- Prasanna Ramakrishnan; Career Education Corporation
- Robin “Montana” Williams; ISACA
- Roota Almeida; Delta Dental of New Jersey
- Roy Mellinger; Anthem, Inc.
- Scott Singer; PaR Systems, Inc.
- Shawn Lawson; Silicon Valley Bank
- Steven Parker; The Advisory Board Company
- Tim Prendergast; Evident.io
- Trevor Hawthorn; Wombat Security Technologies
- Troels Oerting; Barclays
- Vikas Bhatia; Kalki Consulting
- Tenable Security Center Plus
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success