by Cody Dumont
Managing workstation vulnerabilities is often so time intensive that infrastructure vulnerabilities may be overlooked. Tenable Security Center provides the ability to track vulnerabilities for VMware solutions. When analyzing threats to the virtual infrastructure, the security professional should include active and passive detection methods. This report provides a summary and detailed view of the current threats to virtual infrastructure.
Virtualization environments include a combination of hypervisors, management servers, often a large number of virtual machines, and can be complicated. Integrating Tenable Security Center allows the organization to scan these environments for a comprehensive view of vulnerability data and compliance data using the audit files. The VMware integration collects information from vCenter servers, ESXi servers, or a combination of both. The analysis of the virtual infrastructure begins with configuring scan policies to use the authentication category miscellaneous and the settings for VMware ESX SOAP API and VMware vCenter SOAP API, and also using the VMware vCenter API credential.
During the scanning process, Nessus uses unauthenticated API calls to identify the versions of both ESXi and vCenter servers and a majority of of the VMware vulnerability checks are based on the versions of ESXi and/or vCenter. In cases here vCenter manages ESXi servers, the ESXi version information can also be obtained from the vCenter server, which requires successful authentication. Additionally Security Center is able to collect VMware Installation Bundles (VIBs) with successful authentication to vCenter or ESXi. The auto-discovery feature enable Nessus to enumerate the ESXi hosts and virtual machines and add them as targets to be scanned. As with many other assets, Tenable Security Center uses authenticated sessions to audit VMware environments for compliance. Compliance checks are targeted, credentialed checks of ESXi and/or vCenter servers based on the targets listed in the settings.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- SecurityCenter 5.9.0
- Nessus 6.1.1
- PVS 4.0.3
Leveraging Tenable Security Center reports enables operations teams to verify that appropriate protections are in place for virtualized environments. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives.
Chapters
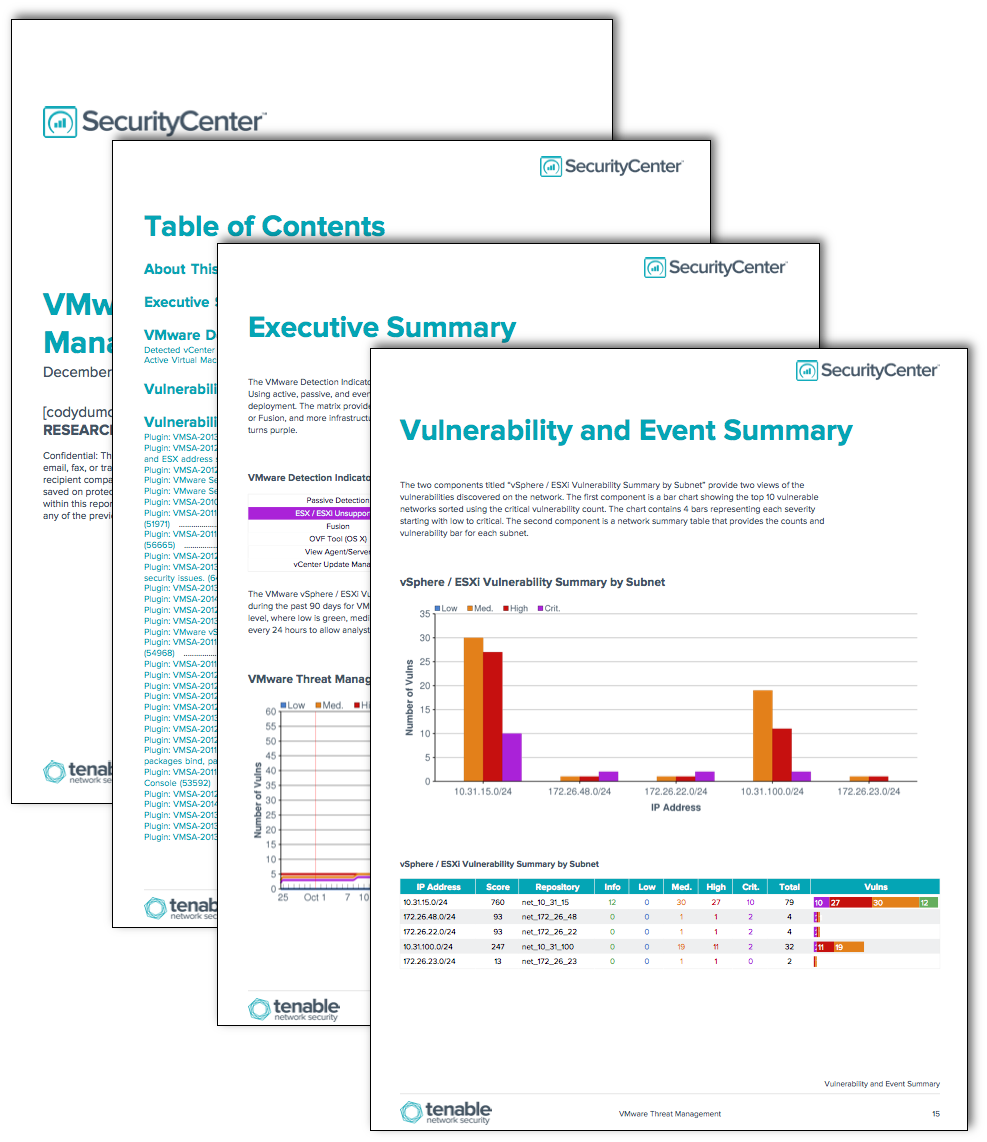
Executive Summary: This chapter provides an executive summary view of VMware related threats. The elements provide IT leaders with a current view and understanding of risks identified using credentialed scanning and host audit scanning. There are serval components showing vulnerability trending, current vulnerabilities vy year, and compliance setting related to VMware hypervisors.
VMware Detection Details: This chapter displays a list of VMware plugins used for the detection services, software enumeration, and other asset inventory purposed. The filter search for VMWare in the plugin name and only selects the informational severity levels. The table provides the plugin detected along with a detailed list of all assets with the plugin present.
VMware Security Advisories: This chapter provides two views of the vulnerabilities discovered on the network. The elements highlight the vulnerable networks using bar charts and tables for each subnet.
Vulnerability Details: The chapter provides a detailed summary of all vulnerabilities.
Audit Details: The chapter provides a detailed summary of all VMWare audit checks.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success