Many data protection regulations, such as PCI DSS and HIPAA, levy heavy fines for data breaches of sensitive information. Effective data protection controls are necessary to avoid breaches of regulatory, statutory, or contractual obligations related to sensitive data.
Organizations that handle sensitive data, such as healthcare and credit card information, are required to audit data protection controls on an annual basis. Leveraging Tenable reports enables organizations to protect data in accordance with business risk posture for Confidentiality, Integrity and Availability (CIA).
The National Institute of Standards (NIST) Special Publication 800-53 provides comprehensive guidance for a secure infrastructure, including guidance on data protection and encryption. The information provided in Tenable dashboards and reports enables Risk Managers and Chief Privacy Officers to demonstrate to third parties and regulatory bodies that sensitive data is protected in accordance with Data Loss Prevention requirements.
The NIST Cybersecurity Framework (CSF) is a control framework, which has high level controls that align with
ISO 27001, NIST SP 800-53, and others. The Cybersecurity Framework’s prioritized, flexible, and cost-effective approach helps to promote the protection and resilience of critical infrastructure and other sectors important to the economy and national security. Many regulating bodies accept evidence documentation of compliance with the NIST CSF as assurance that the organization has effective controls in place to meet their security requirements. The HIPAA Security Rule Crosswalk to NIST Cybersecurity Framework is an example of a regulation aligning with NIST.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report is located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments.
The report requirements are:
Tenable.sc 5.9.0
Nessus 10.2.0
Leveraging Tenable reports enables operations teams to verify that appropriate protections are in place for data at rest, data in transit, and removable media. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives.
Chapters
Executive Summary: This chapter provides a summary view on the state of protections controls relating to Certificates, Encryption, and Confidentiality and Protected Information.
Data Protection Details – This chapter provides details on the state of protection controls in the environment for Certificates, Encryption, and Confidentiality and Protected Information, which are described below.
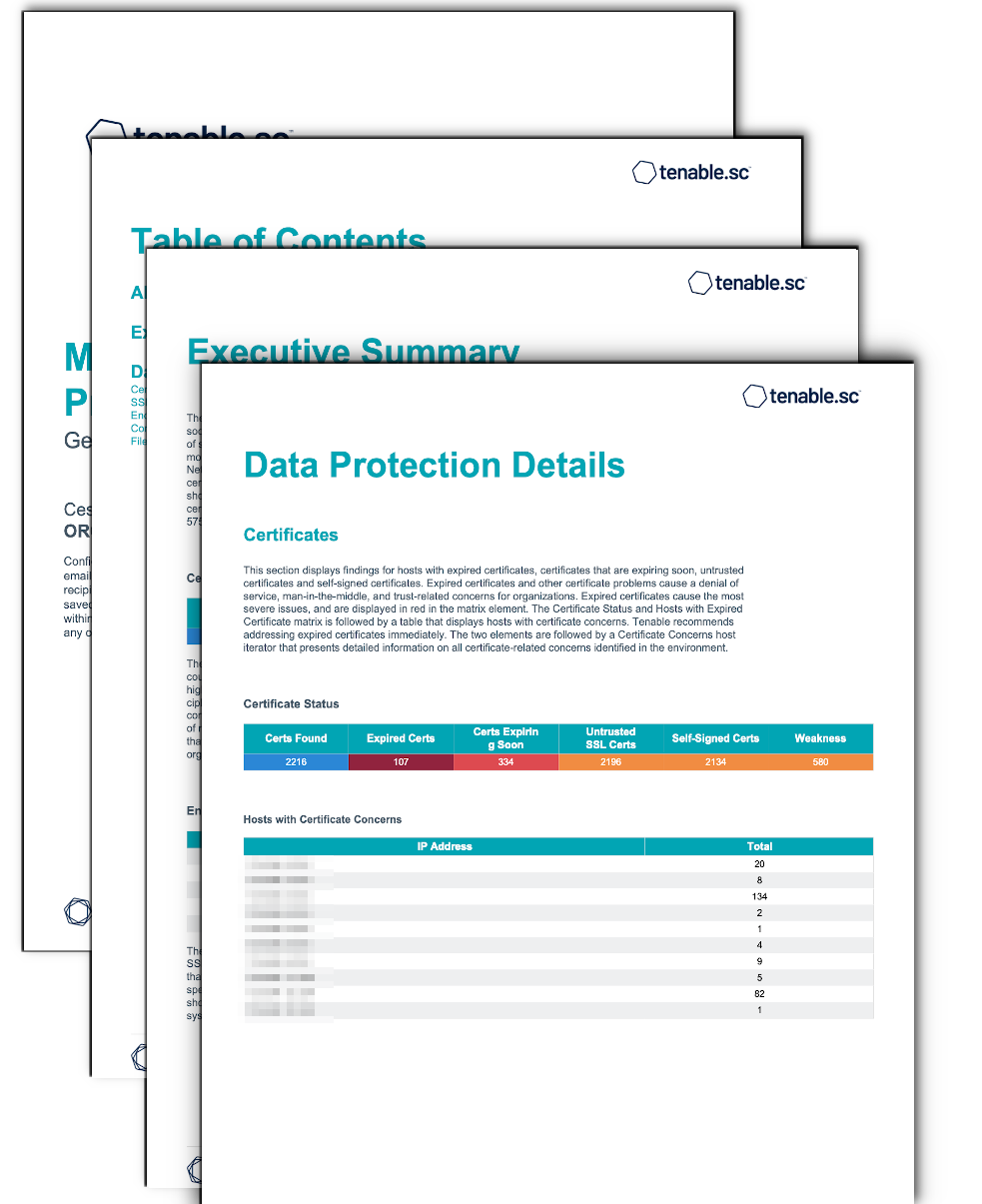
- Certificates – This section displays findings for hosts with expired certificates, certificates that are expiring soon, untrusted certificates and self-signed certificates. Expired certificates and other certificate problems cause a denial of service, man-in-the-middle, and trust-related concerns for organizations.
- SSL/TLS Vulnerability Summary – This section provides an overview of systems and vulnerabilities related to SSL/TLS. The SSL/TLS Vulnerabilities by Type element displays a count of systems and vulnerabilities related to SSLv2 and SSLv3 in the first two rows. From the third row down, information is provided on all the systems running any version of TLSv1 and higher.
- Encryption – This section provides an overview of systems and vulnerabilities related to SSL/TLS and Encryption/Cryptographic Compliance. Information presented in this section highlights issues such as weak hashing algorithms and keys as well as the use of insecure encryption ciphers. Many of these issues are the result of misconfigurations or use of outdated encryption methods. This detailed information also highlights vulnerabilities that can be exploited by attackers. Tenable recommends that security teams review the data to determine the risk to the organization.
- Confidentiality of Protected Information – This section provides an overview of systems and vulnerabilities related to Security Requirement 3.13.16 in the NIST Special Publication 800-171. Revision 2 provides guidance to protect the confidentiality of Controlled Unclassified Information (CUI) at rest and maps to Security Control SC-28 of NIST Special Publication 800-53.
- File Content Audit Results – The following section displays File Content Audit Results. The first two rows of the File Contents Audit Results Compliance Checks provide the total count of Passed checks, Failed checks, and checks requiring a manual review. The first row, ‘Check Count’, provides a count of the current checks per check status. The second row, ‘Check Ratio’, provides a ratio view of check status. The three columns together total 100%. The last two rows provide a system count analysis. The third row, ‘System Count’, provides the number of systems with at least one audit check in the applicable state. The last row, ‘System Ratio’, provides a percentage of systems with at least one audit check in the applicable state.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success