by Ben Smith
The United Arab Emirates’ (UAE) National Electronic Security Authority (NESA) Information Assurance Standards state that various information security policies should be in place across the organization and should comply with policies and with any other standards that are applicable. The NESA standard is a composite of many different types of controls and was derived from similar standards including the ISO 27000 standards, NIST 800, and CIS Controls. NESA makes clear that organizations must comply with all applicable policies, laws, and compliance standards. Many controls require the organization to have appropriate policies covering all aspects of information security. In this report, the operations team can easily see the organization’s current compliance state with NESA and how that compares to other similar standards.
NESA covers a broad array of information security controls. This report provides a summary view of all relevant NESA controls grouped by similarity. Relevant controls have been grouped into six sections. This allows an organization to select the standards and categories that apply to their own business requirements. Each grouping is represented in a separate chapter with separate sections for relevant information. This is shown below in the chapter descriptions.
One aspect of NESA compliance involves ensuring devices conform to generally accepted hardening standards. In adopting any configuration standard or baseline, the organization should review current best practices. Tenable.sc provides the capability to visualize individual hosts with compliance concerns that may not be in line with current best practices. Utilizing a view of audit checks indicating compliance failures, a consultant is able to quickly gain an understanding of which hosts are out of compliance and identify optimized paths to remediate.
Understanding assets on the network ensures a successful vulnerability management program. NESA requires knowledge of assets on the network and the appropriate identification, categorization, and protection of these assets. Knowing the types of assets on the network also aids in identifying known vulnerabilities in administrative, accounting, and business communications systems. Vulnerability assessments should be performed frequently and after any risk assessment or control implementation. Similarly, NESA requires software to be maintained at a level supported by the supplier.
A normal scanning program will show a fairly even spread of assets over time. When this is not the case, the scanning program should be tweaked to ensure assets are appropriately identified and authorized. New assets need to have authorization. Keeping in line with authorizing new assets, Tenable.sc utilizes active scan plugins to show a variety of wireless device information. Suspected wireless devices, access points, wireless vulnerabilities, and more can all be shown using active plugin searches.
In order to understand asset criticality, threat context, and vulnerability severity, an organization needs to understand the security of communications on their network. The most prevalent types of network communication encryption are SSL/TLS and SSH. Data transferred internally, externally, and used for online transactions needs to be protected in transit from exposure to unauthorized third parties. Understanding where good encryption is used, and where good encryption is not is imperative to Cyber Exposure and to NESA. Tenable.sc can identify plugins that indicate the usage of SSL/TLS and SSH. Tenable.sc also shows common cryptographic compliance concerns that help identify areas of exposure.
In order to understand privilege and access, an organization must answer several questions. Are there unnecessary administrative privileges in the organization? Are all user accounts unique? Do administrators log on to non-administrative workstations? Are inactive accounts purged from the environment? Are effective controls for separation of duties in place? The answers to these questions provide a solid basis for understanding credential hygiene and maintaining NESA compliance.
Administrative privileges should be limited specifically to those with a need, to limit the risk from account compromise. Each user of a system should have a unique account assigned. Sharing of user accounts limits accountability for actions. This limits the risk of account compromise via non-hardened workstations and ensures an appropriate audit trail exists in case of credential use by a bad actor. Users should only have the access specifically needed and no more. Similarly, user privileges should be separated by functional groups preventing fraud by ensuring that no individual has unnecessary authority to perform critical functions.
The report and its elements are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment.
The report requirements are:
- Tenable.sc 5.12.0
- Nessus 8.9.0
- Compliance Data
- MDM Data
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess an organization’s adherence to best practice configuration baselines. Tenable.sc provides customers with a full and complete Cyber Exposure platform for completing an effective Cyber Hygiene program prescribed by NESA standard.
This report contains:
Summary: The UAE's NESA information assurance standards define security policies that should be in place across the organization. NESA makes clear that organizations must comply with all applicable policies, laws, and compliance standards. Tenable.sc assists the operations team to easily assess the organization’s current compliance state with NESA and other similar standards.
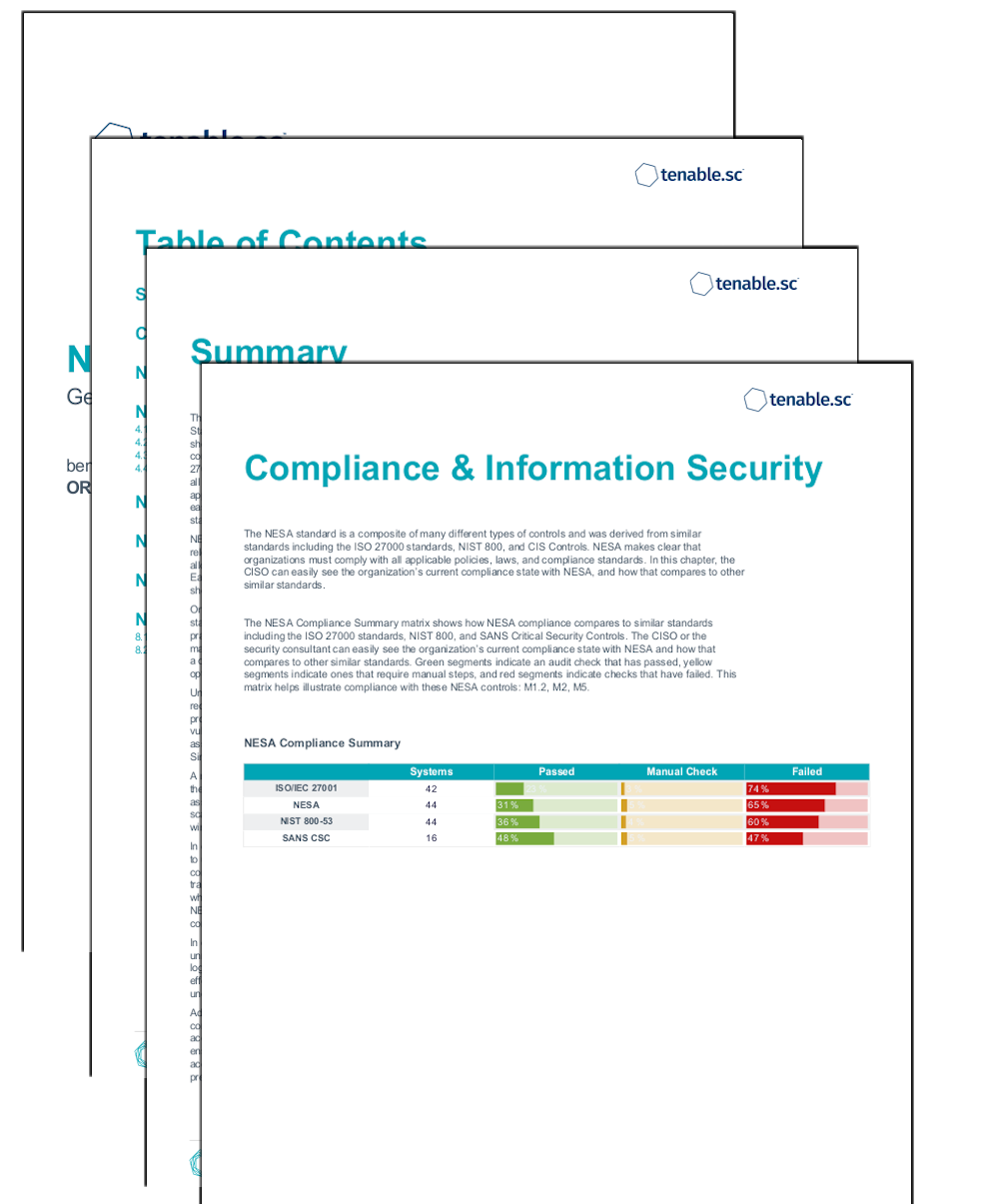
Compliance and Information Security: The NESA standard is a composite of many different types of controls and was derived from similar standards including the ISO 27000 standards, NIST 800, and CIS Controls. NESA makes clear that organizations must comply with all applicable policies, laws, and compliance standards. In this chapter, the CISO can easily see the organization’s current compliance state with NESA, and how that compares to other similar standards.
Configuration Management: The NESA standard includes many controls related to appropriate configuration management and utilizing baselines. Tenable.sc includes audits files based on the CIS Benchmarks which are mapped to a wide variety of compliance standards including NESA and ISO 27000. This chapter provides risk managers with a clear visibility into configuration hardening and overall compliance status.
Vulnerability and Support: The NESA standard includes many controls related to vulnerability management across a wide variety of devices. Tenable.sc includes active scan aggregation and vulnerability management. This chapter provides risk managers with clear visibility into the state of vulnerabilities across the organization.
Asset Identification and Authorization: Tracking asset inventory and authorizing new assets is a key requirement of NESA. Tenable.sc includes active scan aggregation and vulnerability management. This chapter allows a risk manager to easily see the organization’s new assets, mobile assets, wireless assets, and drill into details of each.
Secure Communications: Secure communications are required by the NESA standard. Tenable.sc includes many indicators about encryption used. This chapter allows a risk manager to easily understand the organization’s use of encryption for communications and areas where data leakage may occur.
Users and Privilege: The NESA standard requires the understanding of user privileges and access rights. Tenable.sc includes many indicators of user access and activity. This chapter allows a risk manager to easily understand the user privileges within the organization and areas where rights can be tightened.
NESA Audit Summary: This chapter shows the overall state of compliance in the NESA environment. The Failed Check Summary lists hosts that have failed audit checks and can be easily used by an analyst to keep assets in compliance. The Manual Check lists hosts where manual verification is required. Similarly, the analyst can review those hosts in order to maintain compliance.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success