Malicious process detection is essential to effectively securing an organization. Malicious processes can be indicative of misuse, intrusion, or infection and should be investigated immediately. Tenable.sc is able to leverage Nessus to effectively detect malicious processes on hosts throughout an organization.
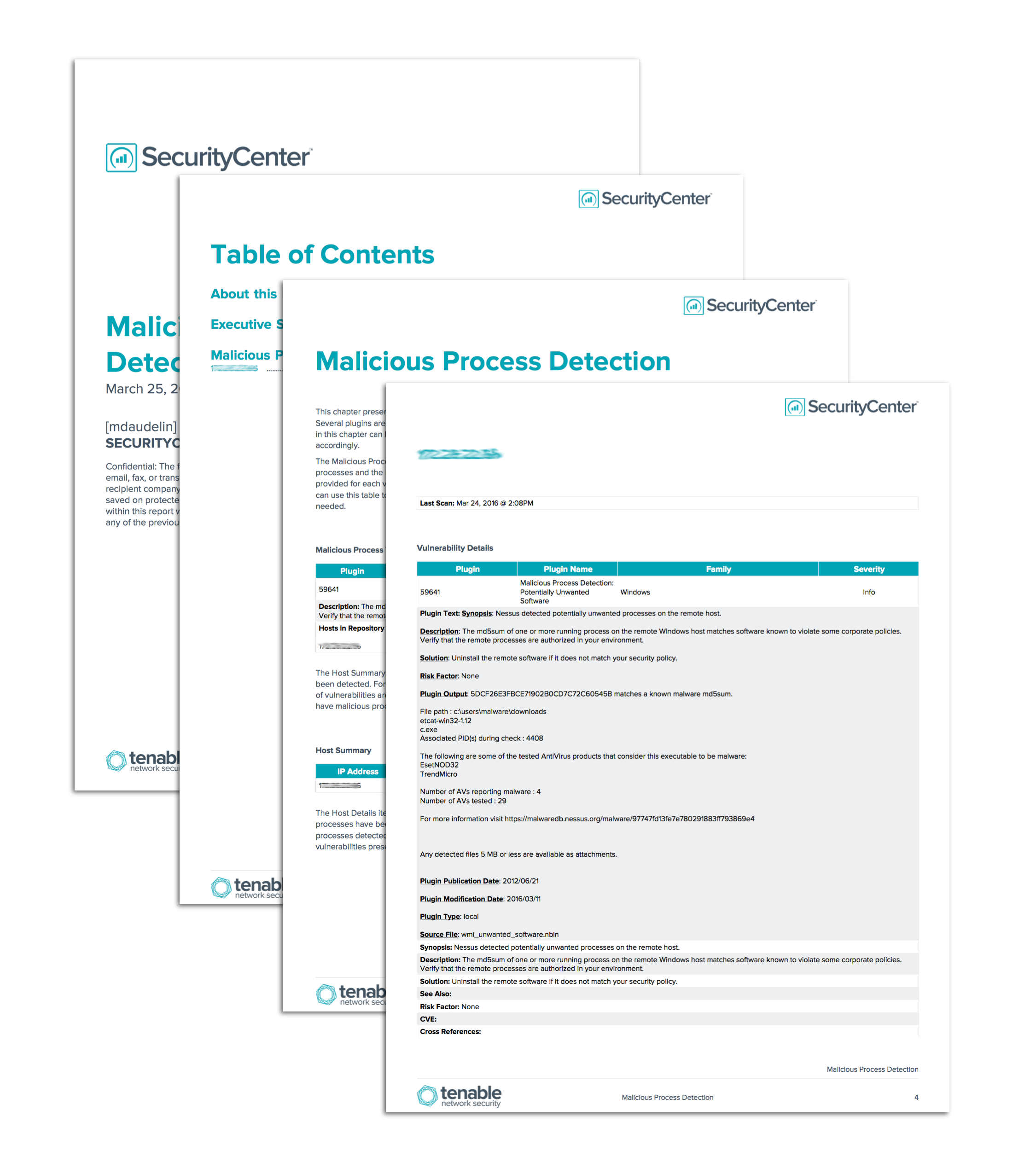
The Malicious Process Detection report assists security teams with identifying vulnerabilities related to malicious processes. Details about malicious process detections are presented for review by security teams. The report also includes detailed information about each host on which malicious processes have been detected. Security teams can use this report in order to monitor their networks for hosts running malicious processes and tailor remediation efforts accordingly.
The chapters in this report leverage data gathered by Nessus credentialed scans. Nessus can detect and provide detailed information about malicious processes running on hosts on the network. The elements are filtered to use plugins related to malicious process detection, and an iterator is used to provide extensive data about each host affected. Any malicious processes detected should be investigated to determine whether they are related to misuse, intrusion, or infection.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection and Vulnerability Assessments. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.6.0
Tenable.sc Continuous View (CV) can identify vulnerabilities, and help eliminate blind spots on your network, such as systems capable of remote access. Tenable.sc CV uses Nessus to detect missing patches, incorrect configurations, lapsed defenses, incomplete monitoring, and network intruders. Tenable’s unique combination of detection, reporting, and pattern recognition leads the market place in Continuous Monitoring. By taking a proactive approach to continuous monitoring, Tenable.sc CV can identify critical risk across the entire enterprise.
The following chapters are included in this report:
- Executive Summary: This chapter provides a high-level overview of malicious processes detected on the network. Trend data about malicious process detection is included, as well as a high-level summary of related vulnerabilities. The elements in this chapter can be used by security teams to monitor the presence of malicious processes over time.
- Malicious Process Detection: This chapter presents detailed information about vulnerabilities related to malicious process detection. Several plugins are used to identify malicious processes and details about the hosts affected. The information in this chapter can be used to identify hosts running malicious processes and focus remediation efforts accordingly.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success