by Cody Dumont
Agencies and organizations that must report to US Cyber Command (USCYBERCOM) must be able to identify vulnerabilities identified by the Information Assurance Vulnerability Management (IAVM) Notices. IAVM Notices are published at several levels with differing priority categories. This report provides a detailed list of the vulnerabilities identified from 2002 – 2015.
The report is available in the Tenable.sc Center Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
- NNM 5.9.0
According to the US Secretary of Defense, the IAVM employs positive control mechanisms to mitigate potentially critical software vulnerabilities through the rapid development and dissemination of actions. The IAVM Notices are posted on a USCYBERCOM website and also entered into the Defense Information Systems Agency (DISA) operated Vulnerability Management System (VMS). Tenable receives weekly updates and correlates the alerts to plugins for integration into Tenable.sc Continuous View (CV). The IAVM publishes three types of alerts:
- IA Vulnerability Alerts (IAVA) address severe network vulnerabilities resulting in immediate and potentially severe threats to DoD systems and information. Corrective action is of the highest priority due to the severity of the vulnerability risk.
- IA Vulnerability Bulletins (IAVB) address new vulnerabilities that do not pose an immediate risk to DoD systems, but are significant enough that noncompliance with the corrective action could escalate the risk.
- Technical Advisories (TA) address new vulnerabilities that are generally categorized as low risk to DoD systems.
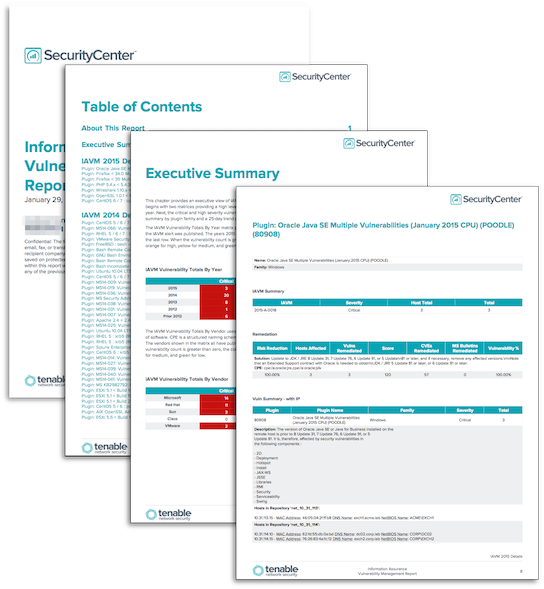
This report provides an executive summary chapter that contains several summary charts and tables. The following chapters contain details for the individual years starting with 2012 – 2015. The last chapter is a combined chapter with vulnerabilities with IAVM alerts released from 2002 – 2011. Each detail chapter contains a network summary chart, showing the most vulnerable subnets, followed by an IAVM summary chart showing the top most severe vulnerabilities. The chapters also provide the vulnerability summary, affected hosts, applicable IAVM alerts, and remediation summary.
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Tenable.sc CV allows for the most comprehensive and integrated view of network health. By combining data from active scanning (Nessus Vulnerability Scanner), passive detection (Nessus Network Monitor), and log analysis (Log Correlation Engine), Tenable.sc CV supports vulnerability detection for more technologies than any other vendor; including vulnerabilities for operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure.
Chapters
Executive Summary - This chapter provides an executive view of IAVM related vulnerabilities within the network. The chapter begins with two matrices providing a high level view of IAVM vulnerabilities detected by vendor and calendar year. Next, the critical and high severity vulnerabilities are summarized. The remaining components provide a summary by plugin family and a 25-day trend graph.
IAVM 2015 Details – This chapter provides the vulnerability details for the IAVM alerts released in 2015. The chapter begins with two summary components showing the most vulnerable networks and most common IAVM alerts. An iterator for IAVM vulnerabilities detected in 2015 follows the summary information. For each vulnerability detected, a list of applicable IAVM alerts, remediation tasks, and affected hosts is provided.
IAVM 2014 Details – This chapter provides the vulnerability details for the IAVM alerts released in 2014. The chapter begins with two summary components showing the most vulnerable networks and most common IAVM alerts. An iterator for IAVM vulnerabilities detected in 2014 follows the summary information. For each vulnerability detected, a list of applicable IAVM alerts, remediation tasks, and affected hosts is provided.
IAVM 2013 Details – This chapter provides the vulnerability details for the IAVM alerts released in 2013. The chapter begins with two summary components showing the most vulnerable networks and most common IAVM alerts. An iterator for IAVM vulnerabilities detected in 2013 follows the summary information. For each vulnerability detected, a list of applicable IAVM alerts, remediation tasks, and affected hosts is provided.
IAVM 2012 Details – This chapter provides the vulnerability details for the IAVM alerts released in 2012. The chapter begins with two summary components showing the most vulnerable networks and most common IAVM alerts. An iterator for IAVM vulnerabilities detected in 2012 follows the summary information. For each vulnerability detected, a list of applicable IAVM alerts, remediation tasks, and affected hosts is provided.
IAVM Details Prior to 2012 – This chapter provides the vulnerability details for the IAVM alerts released prior to 2012. The chapter begins with two summary components showing the most vulnerable networks and most common IAVM alerts. An iterator for IAVM vulnerabilities detected prior to 2012 follows the summary information. For each vulnerability detected, a list of applicable IAVM alerts, remediation tasks, and affected hosts is provided.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success