by Cody Dumont
Database management systems are one of most prized targets for adversaries, and therefore the security team must protect them at several layers. The Center for Internet Security (CIS) and Defense Information Systems Agency (DISA) provide database server configuration hardening guidelines at the OS and database level. This report provides the analyst a review of the current hardening and vulnerability status of database management systems.
The CIS Security Benchmarks program provides documented and widely accepted industry best practices, which help organizations improve their computer security. Tenable is a long standing CIS Security Benchmark Security Vendor. SecurityCenter and SecurityCenter Continuous View (CV) have supported CIS benchmark testing since 2010. Each year, the number of audit files has grown, and as of Q2 2016 there are over 225 CIS audit files. These audit files allow organizations to successfully test for database system configuration best practices. Due to the reputation of the CIS Security Guidelines, these resources are accepted throughout the industry. Many database system compliance requirements are based on or directly relate to CIS Configuration Guidelines, such as requirements in FISMA, PCI DSS, HIPAA and other similar standards.
DISA selected Tenable for the Assured Compliance Assessment Solution (ACAS). ACAS is a product suite that easily provides automated network vulnerability scanning, configuration assessment, application vulnerability scanning, device configuration assessment, and network discovery. As part of ACAS, Tenable provides several audit files created to audit against DISA configuration guides. These audit files have been supported on several products, including database management systems.
This report provides organizations with audit and vulnerability results for all systems related to Relational Database Management Systems (RDMS). The report has three sections consisting of the executive summary, audit results, and vulnerability results. The executive summary provides a quick historic overview of database compliance checks and vulnerabilities within the Database plugin families. The subsequent chapters provide detailed information about audit and database vulnerabilities results respectfully. Analysts can use this report to gain an understanding of database management systems within the organization. To achieve a maximum amount of audit and vulnerability results, both audit scans and vulnerability scans are required.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The report can be easily located in the SecurityCenter Feed under the category Compliance & Configuration Assessment. The report requirements are:
- SecurityCenter 5.2.0
- Nessus 6.6.1
- PVS 5.0.0
- This report requires “Full Text Search” to be enabled for each analyzed repository.
SecurityCenter CV allows for the most comprehensive and integrated view of network health. SecurityCenter CV provides a unique combination of detection, reporting and pattern recognition utilizing industry recognized algorithms and models. Tenable’s distributed solution scales to meet the future demands of monitoring database systems, cloud services, and the proliferation of devices. SecurityCenter CV supports mounting for compliance checks and vulnerabilities on many technologies including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure.
Chapters
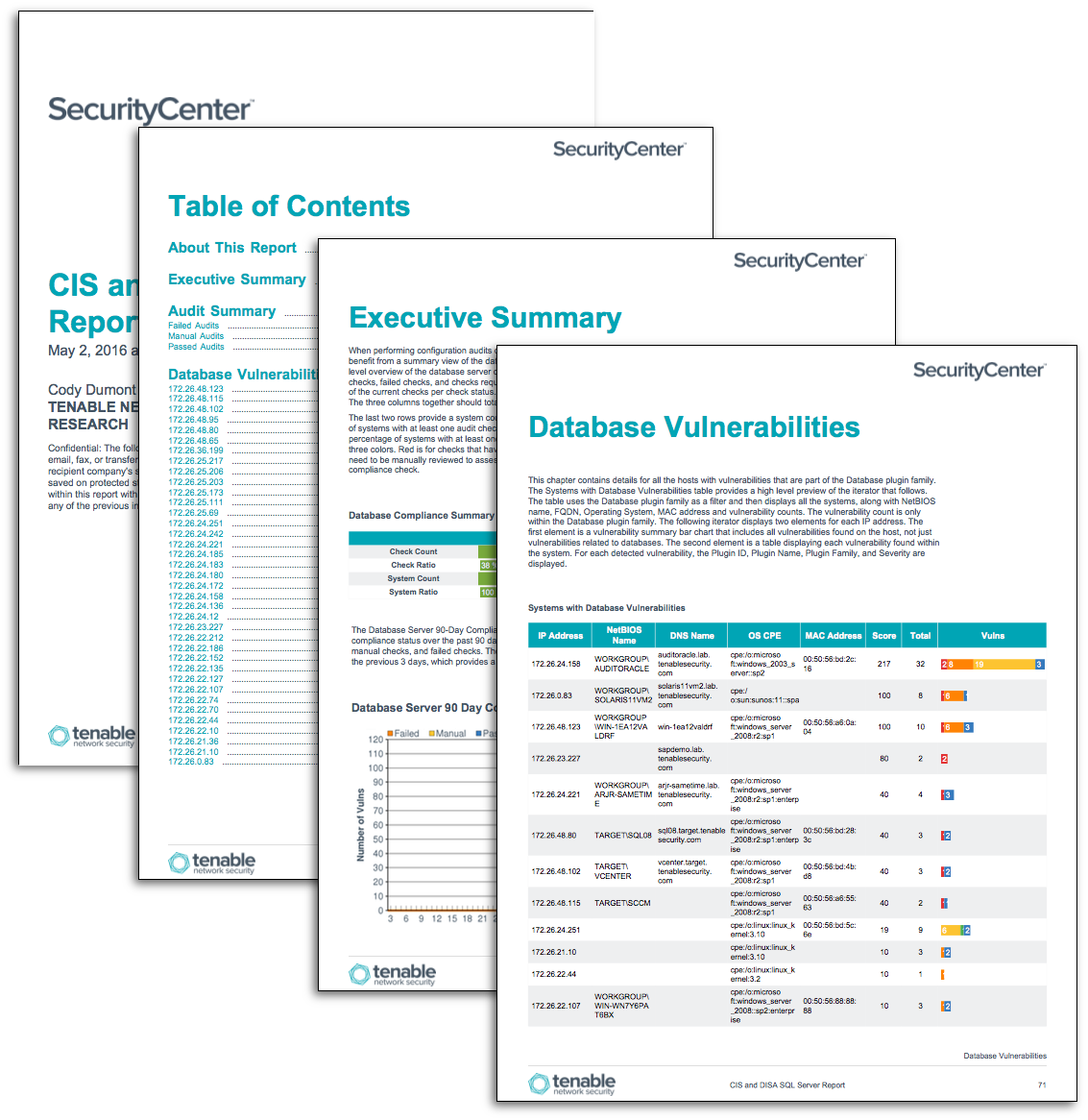
Executive Summary: This chapter provides a high level view of compliance checks and vulnerability data related to databases. For each data type, there is a summary table or chart and a 90-day historical trend line element.
Audit Summary: This chapter provides the details of all database related compliance checks. There are separate sections for each audit result such as Passed, Manual, and Failed. The Passed audit checks have appropriate configurations within the bounds of a compliance check. Failed checks are not within the configured configuration boundary. The manual checks require an analyst or database administrator to review the results to determine if the configuration is a pass or fail.
Database Vulnerabilities: This chapter provides a list of systems with the discovered database vulnerabilities. A full list of all vulnerabilities is included for each system, including database related vulnerabilities.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success