Vulnerable devices and applications on an organization's network pose a great risk to the organization. Vulnerabilities such as outdated software, susceptibility to buffer overflows, and risky enabled services are weaknesses that could be exploited, allowing attackers to compromise the network and steal or destroy data. A robust vulnerability scanning and risk assessment process combined with a sound vulnerability management and remediation program can go far to protect an organization.
Tenable.sc Continuous View (CV) assists in vulnerability management and risk assessment by discovering vulnerabilities through active scanning, passive listening, and host data analysis. Tenable.sc CV groups vulnerabilities into families based on the detection plugins used to discover the vulnerabilities. There is a wide range of plugin families, such as Backdoors, Data Leakage, Web Servers, SCADA, families based on operating system-specific local security checks, families based on network protocols, and more.
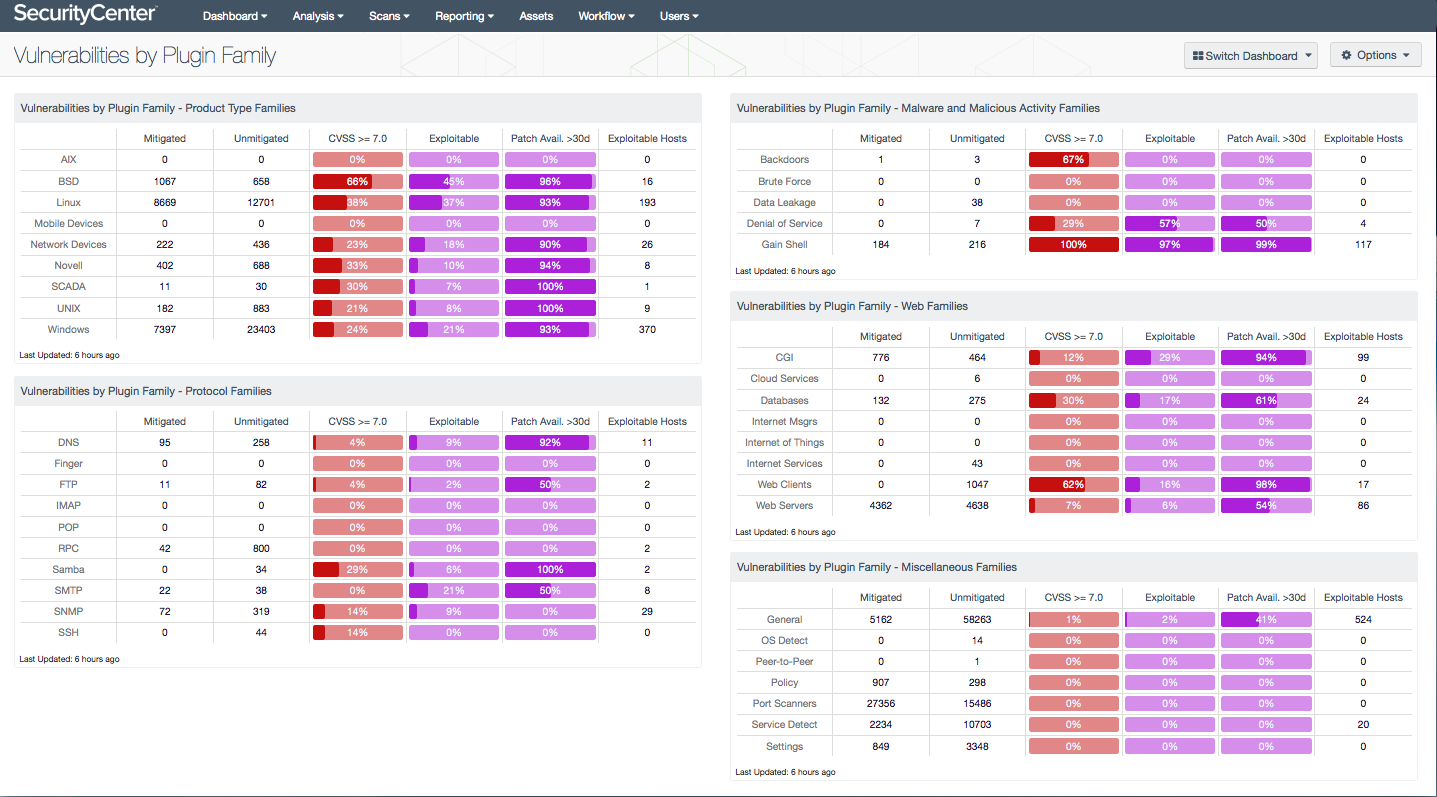
This dashboard presents the vulnerabilities discovered in each plugin family grouping and can assist an organization in identifying vulnerabilities, prioritizing remediations, and tracking remediation progress. Each matrix component groups plugin families at a high level, such as product type families or web families, and each row in a matrix is a specific plugin family or group of related families. For example, in the Product Type Families component, the Linux row includes all plugin families for the various flavors of Linux, such as Red Hat, Ubuntu, Gentoo, and others. In many cases, there are related plugin families for vulnerabilities discovered both actively and passively; these related plugin families are also combined within a matrix row.
Tenable.sc CV records when vulnerabilities are discovered, when patches are issued, and when vulnerabilities are mitigated. In each matrix row, the Mitigated column displays the number of vulnerabilities that have been moved to the mitigated database. A vulnerability is moved to the mitigated database when the vulnerability is no longer detected by a rescan; the vulnerability is assumed to be remediated. The Unmitigated column displays the number of current vulnerabilities that are not yet remediated and have not been moved to the mitigated database. The CVSS >= 7.0 column displays the percentage of those unmitigated vulnerabilities that are the most concerning, as rated by the Common Vulnerability Scoring System (CVSS). The Exploitable column displays the percentage of unmitigated vulnerabilities that are known to be exploitable. The Patch Available column displays the percentage of the unmitigated, exploitable vulnerabilities that have had a patch available for more than 30 days. Ideally, all of these percentages should be 0%, because all severe and exploitable vulnerabilities and all vulnerabilities with patches available should have been mitigated already. The Exploitable Hosts column displays the number of hosts on the network that have unmitigated, exploitable vulnerabilities.
Analysts can use this dashboard to easily drill down into the data presented by the dashboard components. Drilling down enables the analyst to gain more detailed information about the vulnerabilities found on the network, such as which vulnerabilities are the most dangerous. The analyst can also determine information that will benefit vulnerability remediation, such as on which hosts a vulnerability is found and what remediations would most benefit a particular group of machines. Knowing these details can enable better and more efficient vulnerability management, patch prioritization, and remediation efforts within the organization. This will in turn help the organization better protect itself from exploitation of network vulnerabilities, and potential intrusions, attacks, and data loss.
This dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- Tenable.sc 5.3.2
- Nessus 6.7.0
- NNM 5.0.0
- LCE 4.8.0
Many other vulnerability-focused dashboards are also available in the Threat Detection & Vulnerability Assessments Feed category. These dashboards can assist an analyst in further investigating vulnerabilities and tracking remediations. Some suggested dashboards are Vulnerability Top Ten, Web Vulnerabilities, Browser Vulnerabilities, Understanding Risk, and Mitigation Summary. Dashboards dealing with exploitations of specific vulnerabilities (such as Shellshock and Logjam) can be found in the Security Industry Trends Feed category.
Tenable automatically analyzes information from active scanning, intelligent connectors, agent scanning, passive listening, and host data in order to provide continuous visibility and critical context. Active scanning periodically examines systems within the organization to determine risk. Intelligent connectors leverage other security investments to provide additional context and analysis. Agent scanning enables assessing systems without the need for ongoing host credentials. Passive listening provides real-time monitoring of host activity and communications. Host data is analyzed to identify malicious activity and anomalous behavior. The combination of these sensors delivers information that enables decisive action, transforming an organization's security program from reactive to proactive.
The following components are included in this dashboard:
Vulnerabilities by Plugin Family - Product Type Families: This component presents vulnerabilities discovered in product type plugin family groupings.
Vulnerabilities by Plugin Family - Protocol Families: This component presents vulnerabilities discovered in protocol plugin family groupings.
Vulnerabilities by Plugin Family - Malware and Malicious Activity Families: This component presents vulnerabilities discovered in malware and malicious activity plugin family groupings.
Vulnerabilities by Plugin Family - Web Families: This component presents vulnerabilities discovered in web-related plugin family groupings.
Vulnerabilities by Plugin Family - Miscellaneous Families: This component presents vulnerabilities discovered in the remaining plugin family groupings not covered by the other Vulnerabilities by Plugin Family components.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success