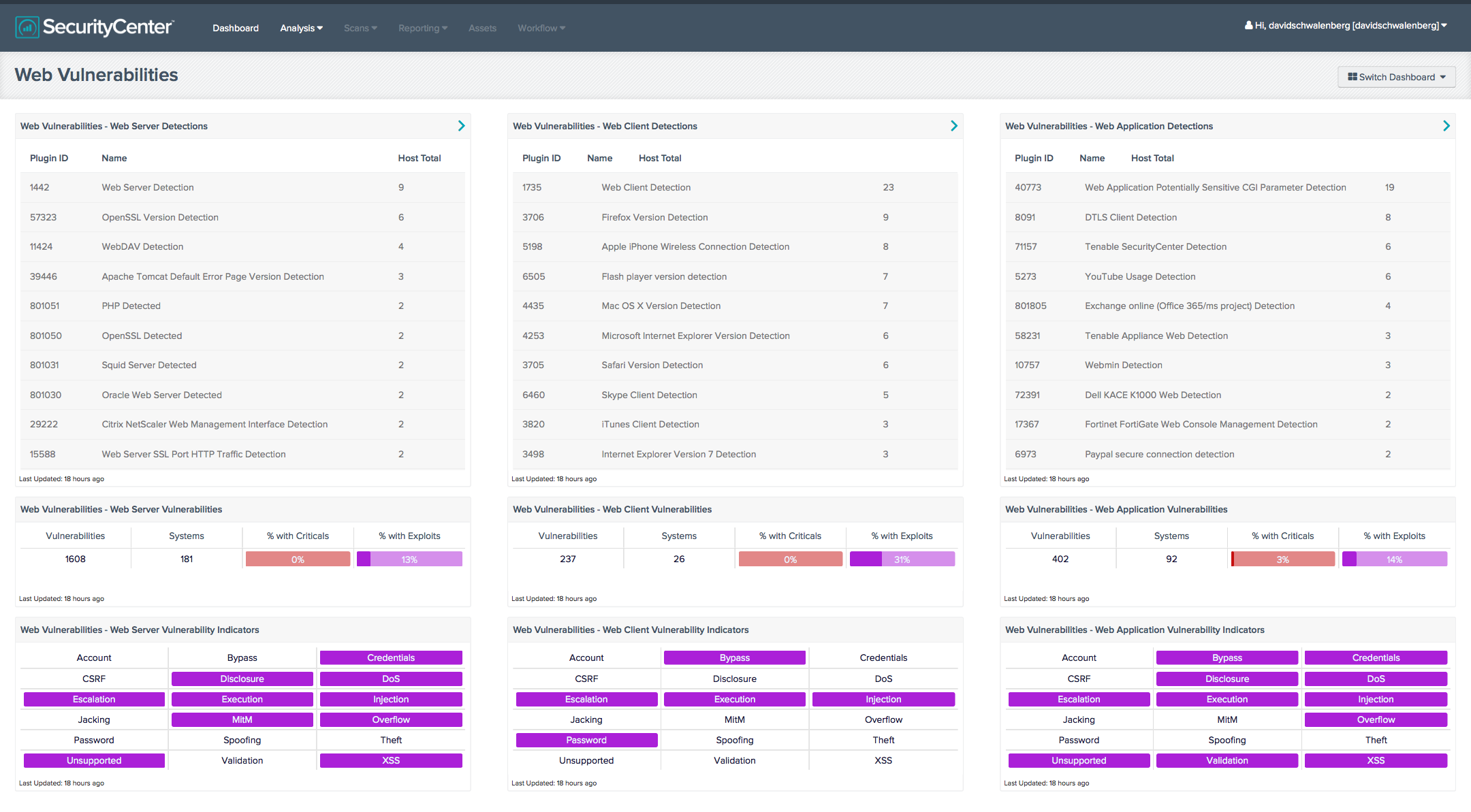
Unauthorized and vulnerable web servers, web clients, and web applications can pose a great security risk to the network. This dashboard displays vulnerability summary information for the web servers, web clients (including web browsers), and web applications detected on the network. An analyst can use this information to determine if any unauthorized web servers, clients, or applications are present on the network and what vulnerabilities exist. For each group, a table of detections is displayed, along with a vulnerability summary and an indicator panel of key words that are present in the vulnerabilities. These key words cover the major web threats, such as password and account weaknesses, information disclosure, improper input validation, injection attacks, cross-site scripting (XSS), and more.
Since web servers, clients, and applications interact through the Internet with the outside world, they are often targeted by outside attackers. Unauthorized web servers pose a risk to the network because there is no way to ensure that they are properly configured and patched. This could allow compromise of the web servers, which in turn could allow compromise of the network. The use of unauthorized and vulnerable web clients and web applications also may allow the network to be compromised. The information in this dashboard can assist the organization as it seeks to reduce its chances of network compromise by eliminating unauthorized web servers, clients, and applications (e.g., from critical servers and point-of-sale systems) and by patching vulnerabilities.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
- SecurityCenter 4.8.1
- Nessus 6.1.1
- PVS 4.0.3
- LCE 4.4.1
Tenable's SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with the Tenable Passive Vulnerability Scanner (PVS), as well as log correlation with the Tenable Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network.
Listed below are the included components:
- Web Vulnerabilities - Web Server Detections - This table displays web server detections on the network. These detections are from the active and passive Web Servers plugin families. A count of hosts is given for each detection; the list is ordered so that the detection with the greatest number of hosts is at the top. An analyst can use this table to determine if any unauthorized web servers are present on the network.
- Web Vulnerabilities - Web Server Vulnerabilities - This matrix displays web server vulnerability summary information. These vulnerabilities are from the active and passive Web Servers plugin families and include all severity levels including Informational. The total number of vulnerabilities is displayed, along with the number of vulnerable systems, a red ratio bar of the percent of systems with Critical severity vulnerabilities, and a purple ratio bar of the percent of systems with vulnerabilities known to be exploitable. Clicking on an indicator will bring up details on the vulnerabilities.
- Web Vulnerabilities - Web Server Vulnerability Indicators - This matrix displays key words that are present in the web server vulnerabilities detected on the network. These vulnerabilities are from the active and passive Web Servers plugin families and include all severity levels except Informational. The key words cover the major web threats, such as password and account weaknesses, information disclosure, improper input validation, injection attacks, cross-site scripting (XSS), and more. A purple indicator means that one or more vulnerabilities contain the keyword; clicking on the indicator will bring up details on the vulnerabilities.
- Web Vulnerabilities - Web Client Detections - This table displays web client detections on the network. These detections are from the passive Web Clients plugin family. A count of hosts is given for each detection; the list is ordered so that the detection with the greatest number of hosts is at the top. An analyst can use this table to determine if any unauthorized web clients (including web browsers) are in use on the network.
- Web Vulnerabilities - Web Client Vulnerabilities - This matrix displays web client vulnerability summary information. These vulnerabilities are from the passive Web Clients plugin family and include all severity levels including Informational. The total number of vulnerabilities is displayed, along with the number of vulnerable systems, a red ratio bar of the percent of systems with Critical severity vulnerabilities, and a purple ratio bar of the percent of systems with vulnerabilities known to be exploitable. Clicking on an indicator will bring up details on the vulnerabilities.
- Web Vulnerabilities - Web Client Vulnerability Indicators - This matrix displays key words that are present in the web client vulnerabilities detected on the network. These vulnerabilities are from the passive Web Clients plugin family and include all severity levels except Informational. The key words cover the major web threats, such as password and account weaknesses, information disclosure, improper input validation, injection attacks, cross-site scripting (XSS), and more. A purple indicator means that one or more vulnerabilities contain the keyword; clicking on the indicator will bring up details on the vulnerabilities.
- Web Vulnerabilities - Web Application Detections - This table displays web application detections on the network. These detections are from the active and passive CGI, Internet Services, and Cloud Services plugin families. A count of hosts is given for each detection; the list is ordered so that the detection with the greatest number of hosts is at the top. An analyst can use this table to determine if any unauthorized web applications are in use on the network.
- Web Vulnerabilities - Web Application Vulnerabilities - This matrix displays web application vulnerability summary information. These vulnerabilities are from the active and passive CGI, Internet Services, and Cloud Services plugin families and include all severity levels including Informational. The total number of vulnerabilities is displayed, along with the number of vulnerable systems, a red ratio bar of the percent of systems with Critical severity vulnerabilities, and a purple ratio bar of the percent of systems with vulnerabilities known to be exploitable. Clicking on an indicator will bring up details on the vulnerabilities.
- Web Vulnerabilities - Web Application Vulnerability Indicators - This matrix displays key words that are present in the web application vulnerabilities detected on the network. These vulnerabilities are from the active and passive CGI, Internet Services, and Cloud Services plugin families and include all severity levels except Informational. The key words cover the major web threats, such as password and account weaknesses, information disclosure, improper input validation, injection attacks, cross-site scripting (XSS), and more. A purple indicator means that one or more vulnerabilities contain the keyword; clicking on the indicator will bring up details on the vulnerabilities.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success