Searching for Custom Malicious File Hashes with Nessus
The Nessus malicious process detection plugins were recently enhanced to allow for searching with custom file hash lists. This allows organizations to add their own sources of malicious file hashes into Tenable's set of cloud-based hashes and botnet checks.
Previously, Nessus included checks to perform file integrity checks of running Windows processes during credentialed patch or configuration audits. The file hashes are cross referenced against a large database of known malware.
This feature has been very popular with our customers and was extended to include support for a variety of additional indicators, including the Mandiant APT1 file hashes.
We've received many requests to allow Nessus to perform the same type of hash check, but against a custom list of hashes. Many of our customers receive hash lists from the U.S. government and from intelligence services such as Critical Intelligence, Cyber Squared, iSight Partners, or Mandiant.
Tenable's Research team recently introduced plugin 65548 which allows users to upload a custom list of hashes. Plugin 65548 includes a preference which specifies a list of hashes that can be named or simply listed as follows:
# hashes for the foobar malware
11b95ccc1427be5f6c7f0e547bde34e6,foobar malware 1.0
333459378f2d53d861ed2819b8b298af,foobar malware 1.1
f80a405f55c2cd651e58a8fc59550830,foobar malware 1.2
# example.exe
4f8793a9c7560af2cb48f062cd7879af
Below is a screen shot of a scan performed with Nessus for a variety of custom file hashes:
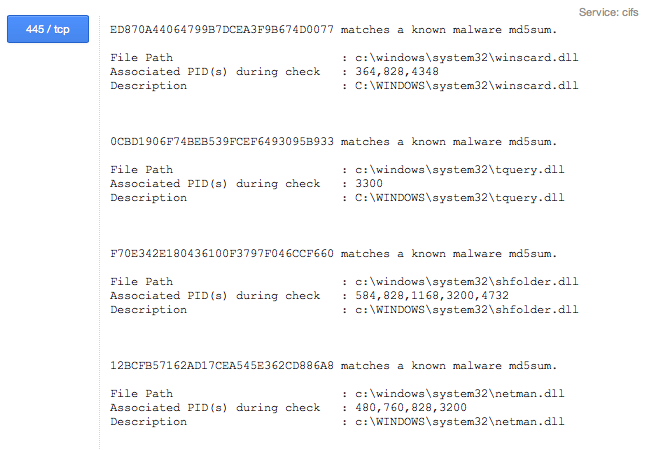
The report includes the running process IDs. If you run a SIM or log search tool, such as Tenable's Log Correlation Engine, these IDs can be used to identify logs associated with the potential malware. An example video illustrating this concept is located on the Tenable YouTube Channel.
Organizations managing their scans with SecurityCenter or SecurityCenter Continuous View can also leverage this feature and perform these types of audits right next to their web, patch, botnet, configuration, or vulnerability scans across thousands and tens-of-thousands of systems.
Learn more
- Nessus



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success