New to Nessus: More Cloud Support, Init15 Voting Winners and More

Note: Nessus Cloud is now a part of Tenable.io Vulnerability Management. To learn more about this application and its latest capabilities, visit the Tenable.io Vulnerability Management web page.
We are pleased to announce the release of Nessus 6.5. Like all new releases of Nessus®, this one is chock full of great new capabilities. I’ll hit a few highlights here. Visit the New in Nessus 6.5 web page for more details and a complete list.
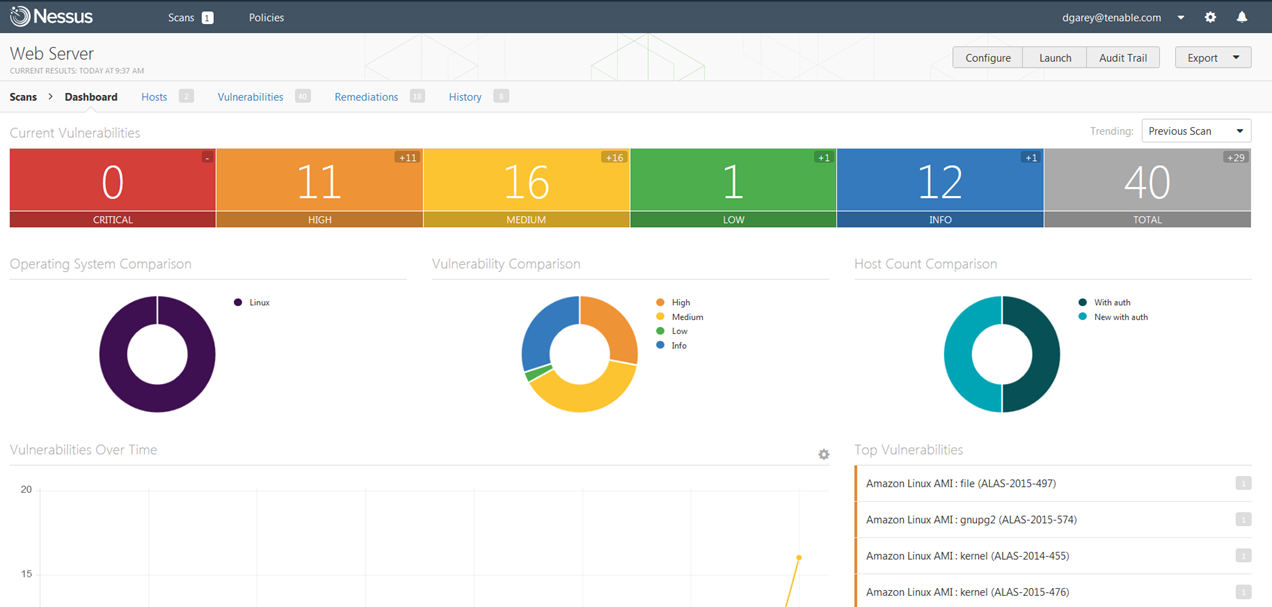
Cloud support
Nessus Agents cloud OS support
We know that many of our Nessus customers are moving some or all of their IT assets to the cloud so we’re continuing to add capabilities to help them make sure their cloud environment is free of vulnerabilities and configuration issues.
Nessus 6.5 adds Nessus Agent operating systems support for popular cloud operating systems (Note: You can also use agents on these OSs if you’re running them in a physical or virtual environment):
- Amazon Linux
- Debian Linux
- Ubuntu Linux
According to ZDNet, Ubuntu is by far the most popular cloud operating system, running in Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform, Fujitsu, and Joyent. So if you’re spinning up IT services in the cloud and running one of these popular OSs, consider using Nessus Agents to check for vulnerabilities and configuration issues.
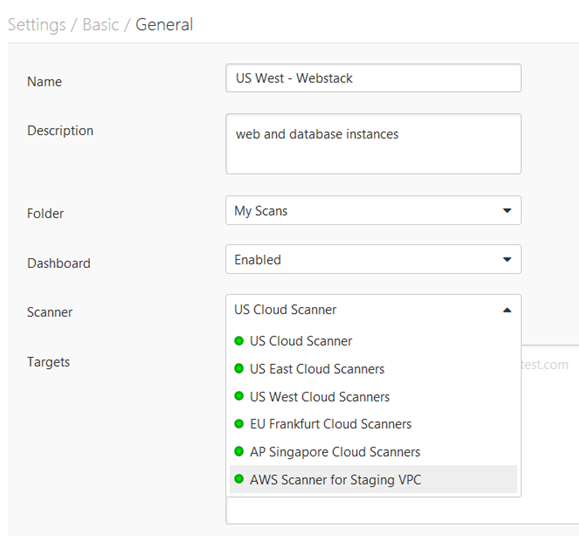
New Nessus scanner for AWS
We’re making it easier for organizations using AWS to scan EC2 instances with Nessus. With Nessus 6.5, we’ve introduced a new scanner for AWS that comes with your Nessus Cloud license. Simply install the scanner in your AWS environment, point it at the targets you’d like to scan, and then view and manage the scan results in Nessus Cloud.
Note: This new Nessus scanner will soon be available in AWS Marketplace.
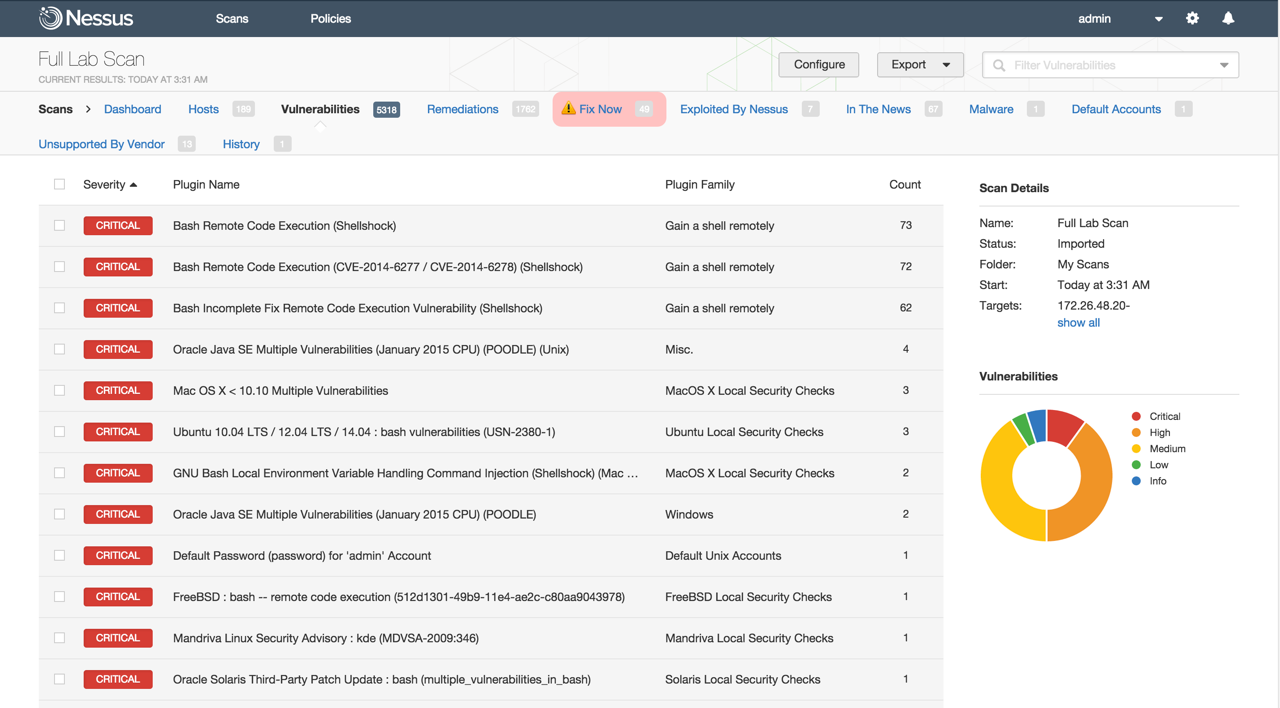
Init15 voting winners
The Tenable hackathon, dubbed Init15, was an intense 60-hour event for the Tenable R&D and product management teams held in Las Vegas this summer. The product teams came up with fantastic new enhancement ideas for Tenable products, customers voted on their favorites, and we're pleased to announce that the top three vote-getting enhancements made it into this release.
Remediation Prioritization (Caught With Your Pants Down)
New filters in Nessus 6.5 help customers prioritize which vulnerabilities they should remediate first. There are five new filters you can use to address the most critical of vulnerabilities. For example:
- Can the vulnerability be exploited by Nessus? If so, that means anyone else using Nessus, including the many people who have the most basic Nessus Home account, can too.
- Is it a vulnerability on an asset that is no longer supported by the vendor, for example a vulnerability in Windows 98? That means it’s never going to be fixed.
- Is it a vulnerability that’s recently in the news, like Shellshock or Heartbleed?
Using these or the other new filters will help you make best use of resources and fix those vulnerabilities that could cause the biggest holes in your attack surface.
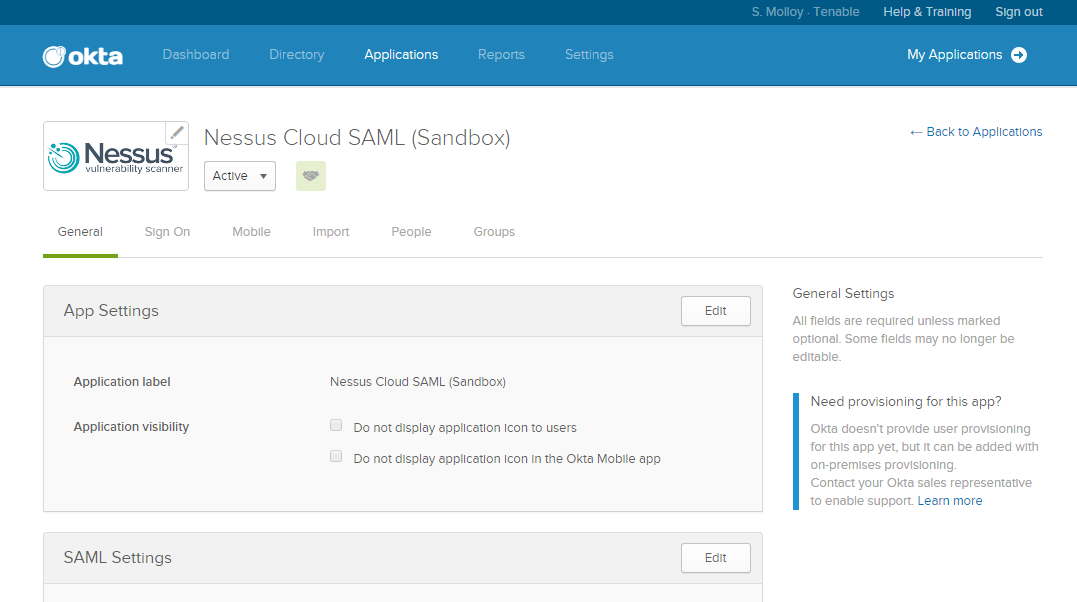
SAML Authentication for Nessus Cloud
The second new feature that came from Init15 voting is a micro-services based architecture that lets customers use SAML authentication services (such as Okta) for access to Nessus Cloud.
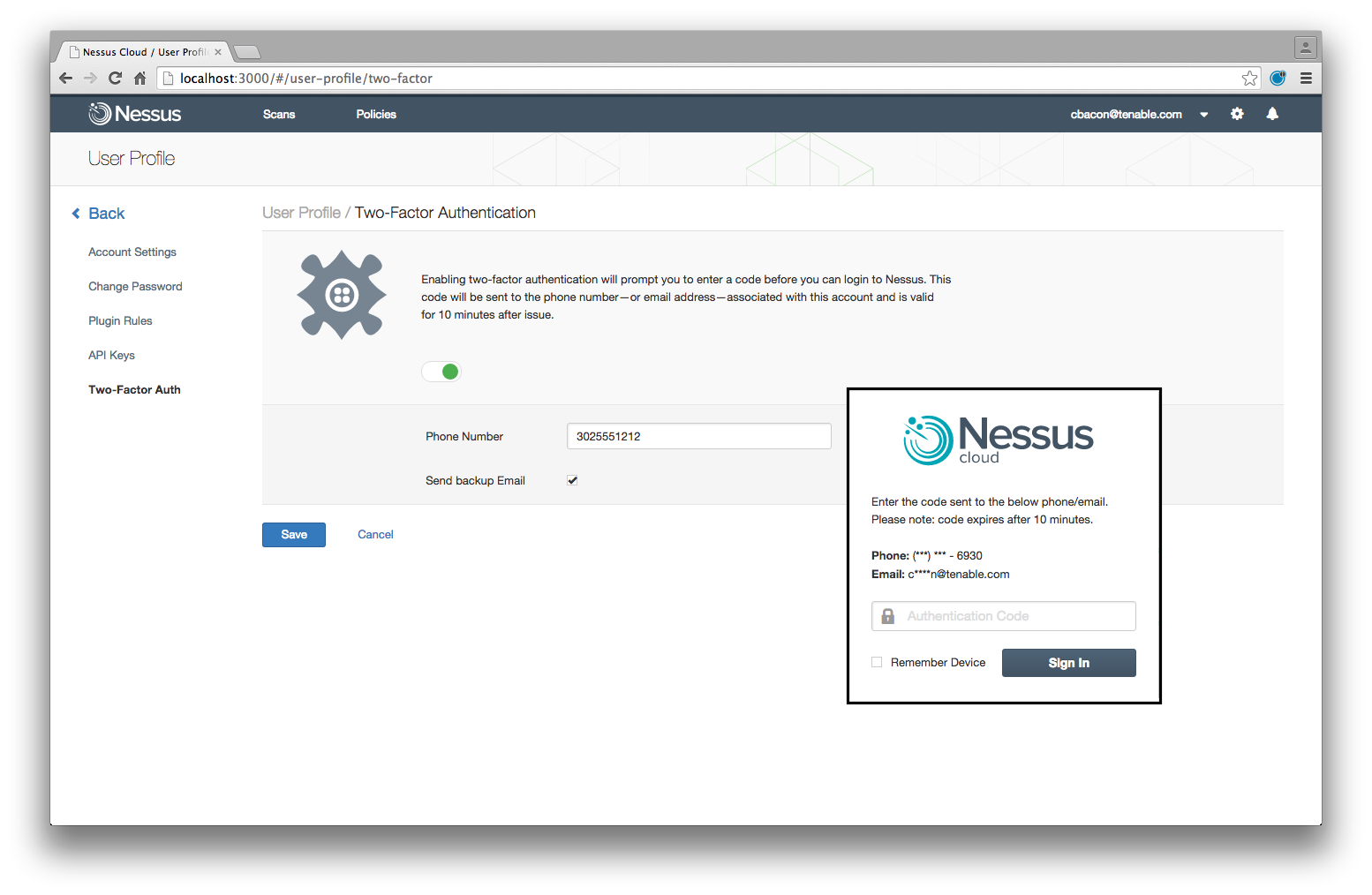
Nessus Cloud Two Factor Authentication
And finally, thanks to customer votes, Nessus Cloud now includes two-factor authentication using Twilio and SMS.
Note: This capability will initially be available for Nessus Cloud customers in North America; we expect it will be expanded to other regions in the future.
Nessus Cloud regional data center availability
While not part of Nessus 6.5 itself, we made an announcement last week about Nessus Cloud regional data center availability. This includes expansion of Nessus Cloud services into Europe with its software as a service (SaaS) applications hosted on AWS in the AWS EU (Frankfurt) region. For organizations that want or need to maintain data storage in a local region, we're pleased to offer this capability as a Nessus cloud-hosted option.
Congratulations to the entire Nessus team on a successful launch. Many thanks to Matt McClellan, Corey Bodzin and Glen Pendley for their contributions to this article.
Learn more
- Agents
- Announcements
- Cloud
- Nessus



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success