Managing Credentials Just Got Easier: SecurityCenter and CyberArk
Note: Tenable SecurityCenter is now Tenable.sc. To learn more about this application and its latest capabilities, visit the Tenable.sc web page.
Scanning with credentials is essential for getting the most out of your vulnerability management. Credentialed scans give you a “deeper dive” into your environment by providing access and visibility into assets that could otherwise only be scanned remotely, and therefore remain vulnerable. Scanning with credentials gives you access to the local host, which will get you much richer results.
So we know that for the best results we should use credentials, but we also know that having to manage an ever-changing, increasingly complex set of passwords, usernames and privileges across multiple platforms can be a challenge, especially in large environments. Tenable has a solution.
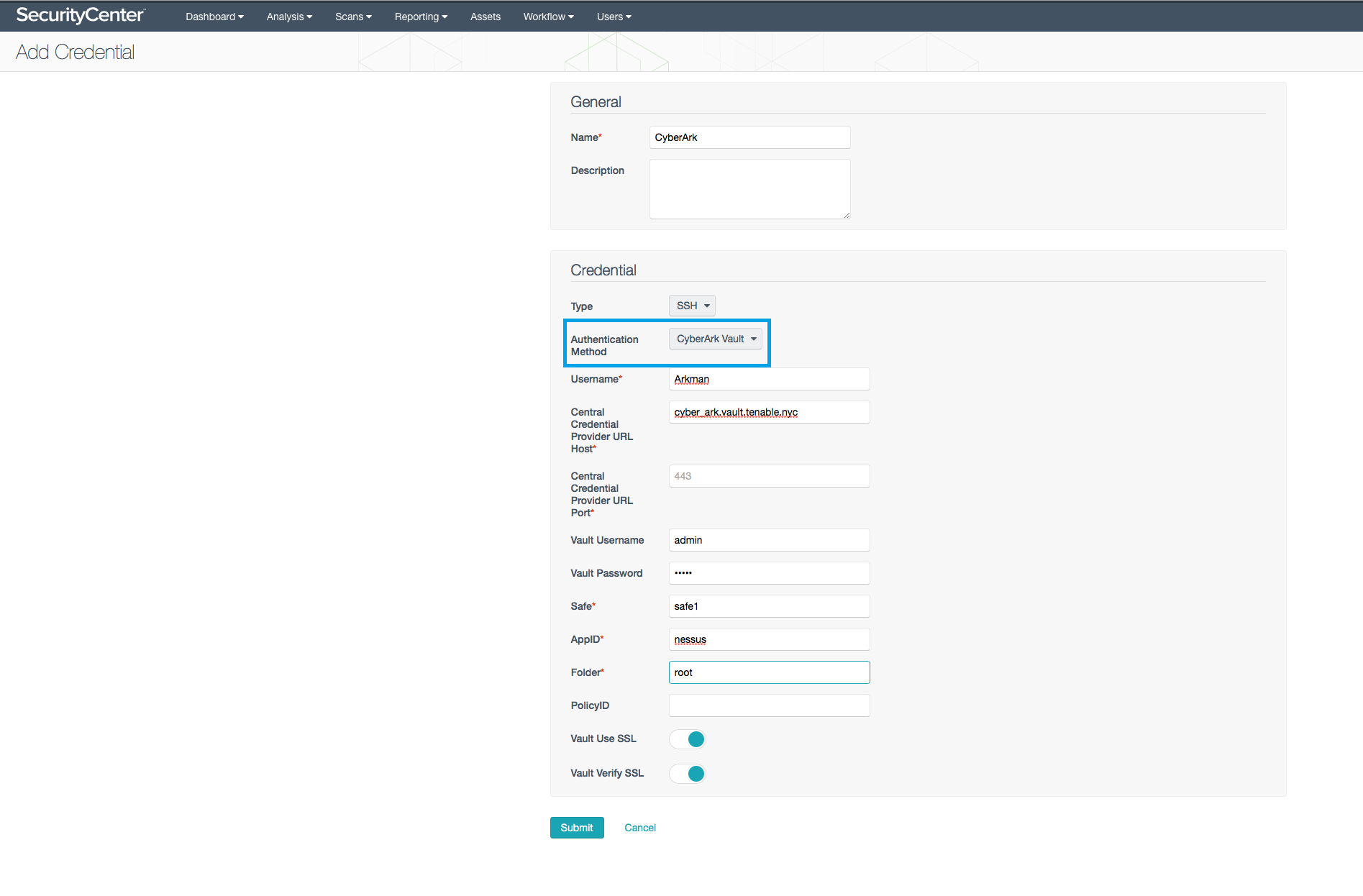
To make credentialed scanning easier, SecurityCenter™ now integrates with CyberArk, a leading enterprise password vault. With this integration, you will no longer have to manually add passwords into SecurityCenter each time you want to run a credentialed scan. Simply configure your CyberArk credentials once, and you’re good to go.
This new feature will save you valuable time that could otherwise be spent on remediating, or creating beautiful Assurance Report Cards (ARCs) to impress your manager. Additionally, SecurityCenter will automatically update passwords as they change in CyberArk, so you only have to manage one tool.
Credential types that are supported include:
- Windows (domain/username + password)
- SSH (username + password; username + ssh key (w/o password))
For more information including a video and link to technical documentation, please visit our CyberArk integration page.
- Announcements
- Integrations
- SecurityCenter
- Vulnerability Scanning