Influence of the NIST Cybersecurity Framework on Hong Kong

Security is a common language across the globe; every person, organization, and country is concerned about security. From personal data privacy, business impact of cyber threats, to protection of core infrastructures, our objective in security is very simple: we all want to prevent attackers from doing something catastrophic. But after so many years and so many generations of technology, is there a simple solution for us all?
NIST
I am so lucky to have the privilege of visiting different organizations to exchange viewpoints in information security. And through those discussions, I have discovered that the Cybersecurity Framework (CSF) from the U.S. National Institute of Standards and Technology (NIST) is influencing my hometown—Hong Kong.
HKMA
Hong Kong, one of the premiere global financial centres of the world, has a solid tradition of protecting the finance industry and managing risk. The Hong Kong Monetary Authority (HKMA), governed by the Exchange Fund Ordinance and the Banking Ordinance of Hong Kong, is responsible for maintaining monetary and banking stability. In response to the latest cyber threats, HKMA published a circular in September 2015 highlighting the growing importance of Cybersecurity Risk Management. This circular drew a great deal of attention from the banking industry in Hong Kong, as all of the banks were looking for solutions to meet the requirements listed in the circular. When I visit banks and discuss this circular, some of them tell me that their security consultants suggest they can implement the NIST Cybersecurity Framework in response to HKMA's circular. Recently, in May 2016, HKMA launched the Cybersecurity Fortification Initiative. This initiative includes three parts: the Cybersecurity Fortification Initiative (CFI), the Cyber Resilience Assessment Framework (C-RAF), and the Intelligence-led Cyber Attack Simulation Testing (iCAST).
Security is a common language across the globe
Similarities between initiatives
I found an interesting similarity in the C-RAF and CSF; the Cyber Resilience Assessment Framework, Step 2, maturity assessment and the NIST Cybersecurity Framework both include five technical functions: identify, protect, detect, respond and recover. HKMA has not yet released details of C-RAF, but I believe the detailed version will share similarities with the NIST CSF. Why is that?
The NIST Cybersecurity Framework provides a flexible and risk-based implementation approach, it is not a one-size-fits-all framework, instead it enables different organizations to select the cybersecurity risk management process that fits their current situation. Why is that important? Because even in the same industry, each organization may have a different security posture. And the best way to help improve your security posture is to understand yourself better, to set an achievable goal, and to review and refine your objectives each year.
Even in the same industry, each organization may have a different security posture
I believe HKMA will provide specific security controls and recommendations, based on the uniqueness of the Hong Kong FSI market. But take a look at the NIST CSF now to better prepare for HKMA recommendations.
SFC
And last but not least, the Securities and Futures Commission (SFC) of Hong Kong issued a Circular to all Licensed Corporations in Hong Kong on 23 March 2016. The circular enumerated the first Suggested Cybersecurity Controls, including:
- Establish a strong governance framework to supervise cybersecurity management
After reading this blog, which framework comes to mind first? The NIST CSF is a tried and true framework gaining popularity worldwide. It’s worth serious consideration at your organization.
Tenable solutions
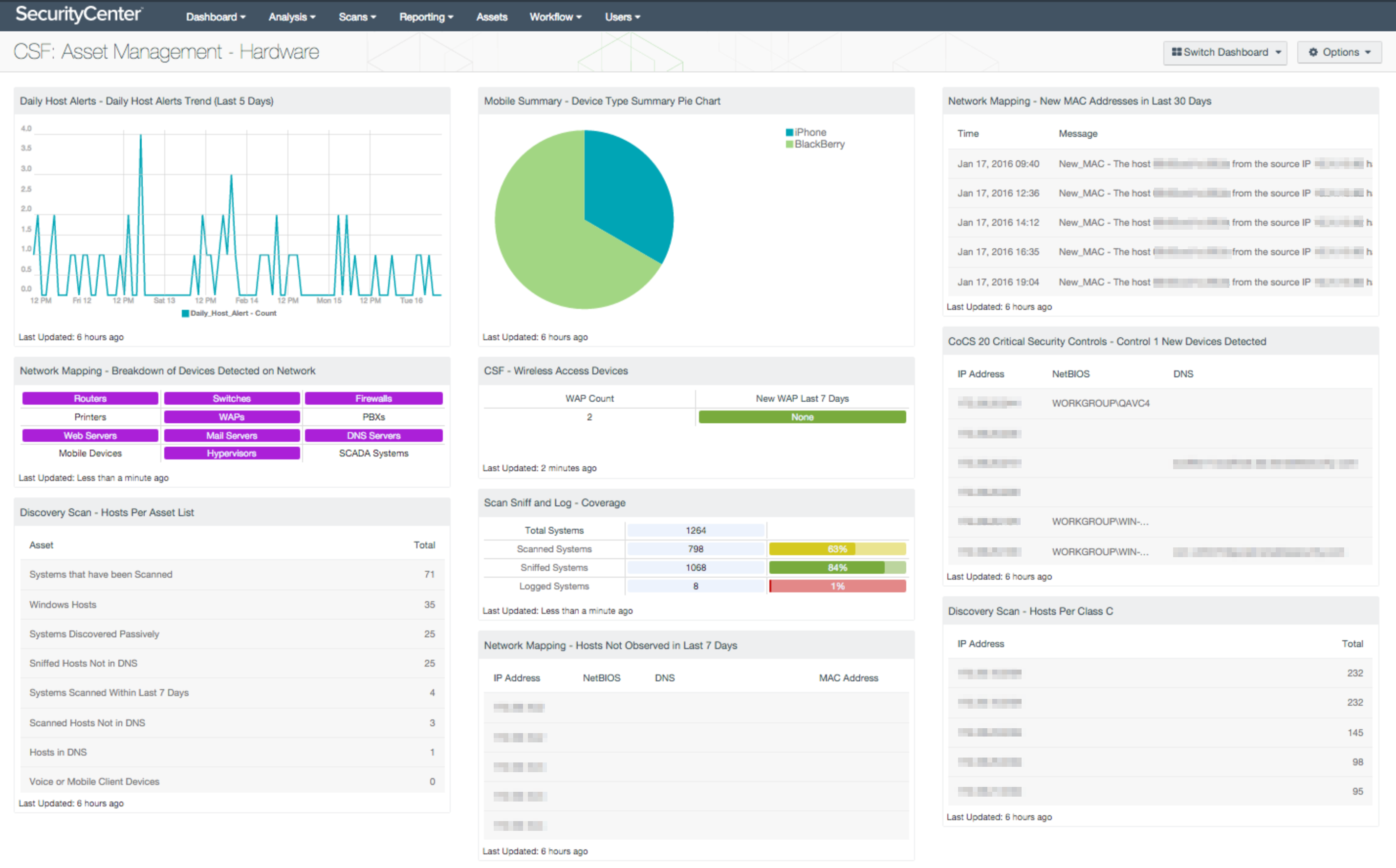
Tenable can help you implement a framework. Our unique SecurityCenter Continuous View™ (SecurityCenter CV™) solution can help. SecurityCenter CV will first collect data using different methods. For example, it can scan the network, together with picking up network packets and data from hosts. All data is pulled together, and based on what you have and what is happening, SecurityCenter CV will advise you about what to address and what you should be concerned about.
The SecurityCenter CV also provides dashboards for many frameworks. For example:
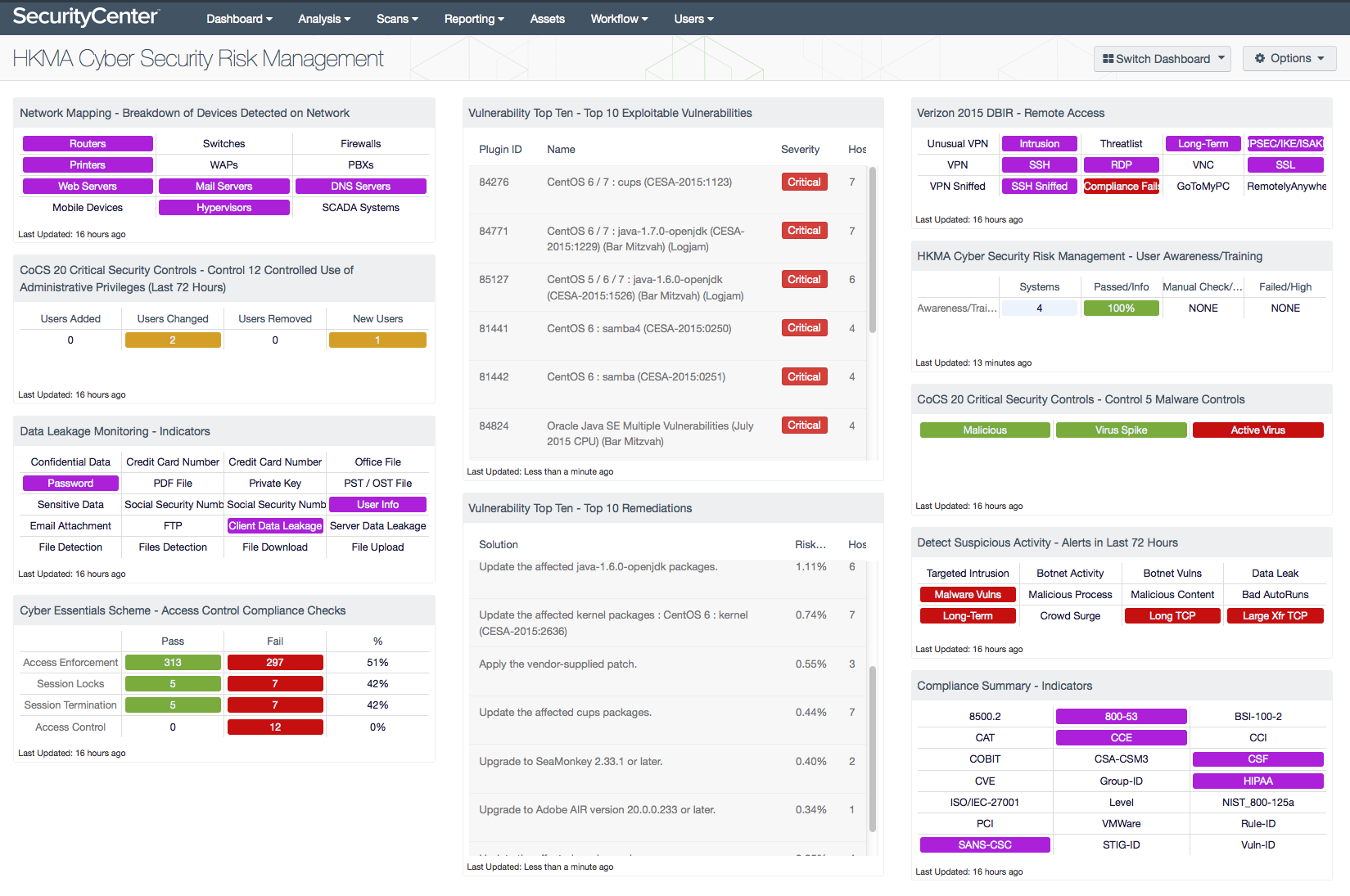
The HKMA Cyber Security Risk Management dashboard maps to the cyber security controls prescribed by HKMA. It provides an initial view of your current security posture and what you have in your network, and it helps you identify significant risks so you can prepare better for different audit requirements.
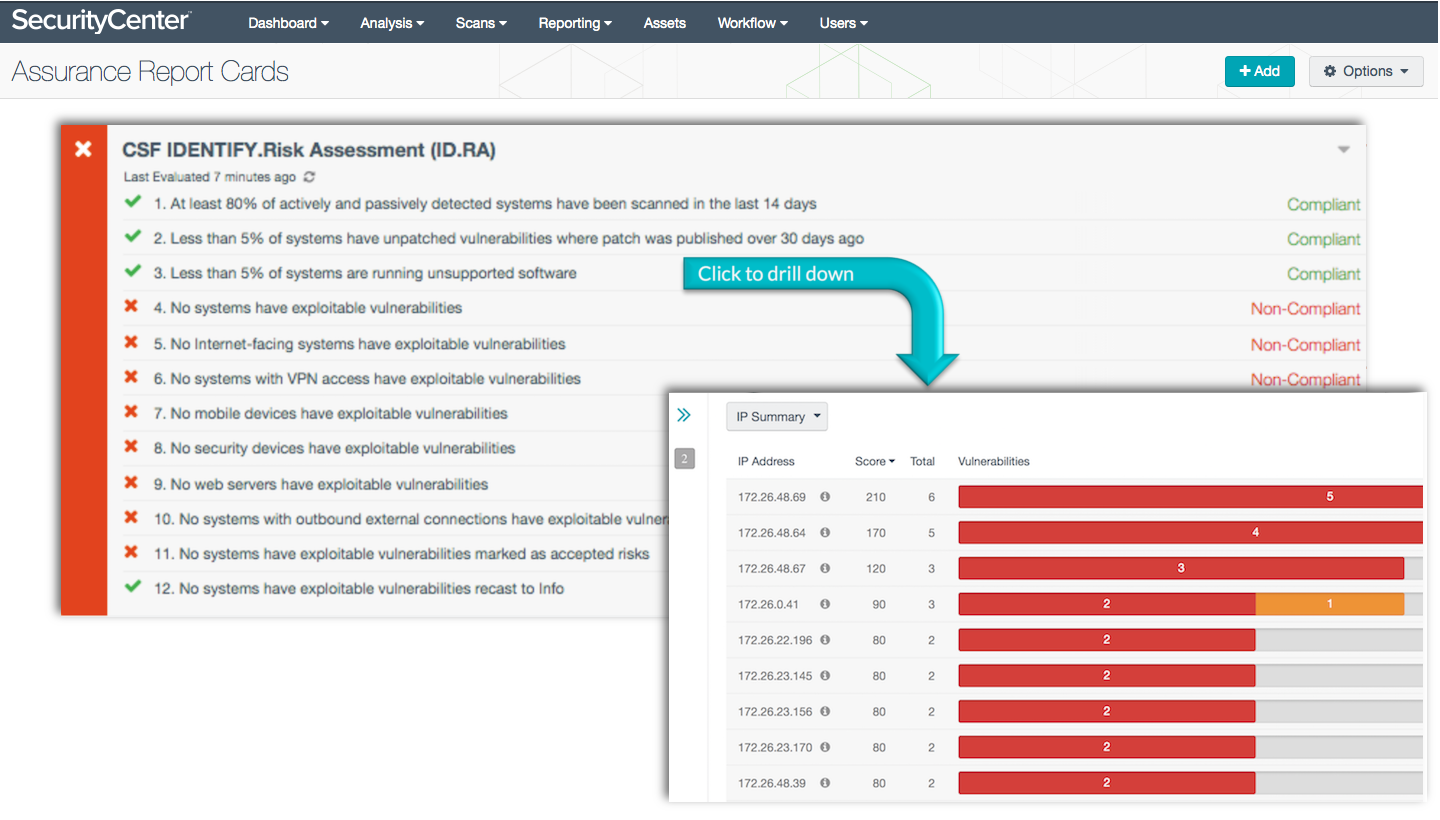
A lot of customers will move on to build their own security framework, based on CSF. SecurityCenter CV supports over 90% of the NIST CSF technical controls and includes 9 Assurance Report Cards (ARCs) and 20 dashboards built specifically to illustrate CSF conformance.
With the ARCs, you can report on your security posture that matches your business context.
You can learn more about NIST CSF support in our solution story.
More information
Check out a few more blogs about the NIST Cybersecurity Framework:
- Understanding NIST’s Cybersecurity Framework
- Tenable Automates NIST Cybersecurity Framework Technical Controls
- NIST Cybersecurity Framework Adoption on the Rise
- Tailoring the NIST Cybersecurity Framework for a Precise Fit
Also read about what ARCs can provide:
Learn more
- APAC
- Financial Services
- NIST
- Security Frameworks




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success