Implement Good Cyber Hygiene with Continuous Network Monitoring

Does your state or local government agency have too few IT security personnel? Have you been tasked with developing your organization’s cybersecurity program? Is the growing complexity of your IT environment causing poor visibility and gaps in protection?
If you answered "yes" to any of the above questions, implementing good cyber hygiene through continuous network monitoring may be the solution you’ve been looking for.
Good cyber hygiene, as outlined by the Center for Internet Security (CIS) and the Council on CyberSecurity (CCS), means appropriately protecting and maintaining IT systems and devices and implementing cybersecurity best practices. When good cyber hygiene is built upon a continuous network monitoring platform, you continuously visualize the security posture of your entire IT infrastructure and better protect your organization against advanced cyber attacks.
Good cyber hygiene
CIS and CCS introduced the Cyber Hygiene Campaign for state, local, tribal, and territorial governments last year, with the vision of providing a low-cost program for enabling immediate and effective defenses against cyber attacks. The campaign’s top priorities address the vast majority of known cyber threats:

- Count: Know what’s connected to and running on your network
- Configure: Implement key security settings to help protect your systems
- Control: Limit and manage those who have administrative privileges for security settings
- Patch: Regularly update all apps, software, and operating systems
- Repeat: Regularly revisit the Top Priorities to form a solid foundation of cybersecurity
The campaign aligns with the NIST Cybersecurity Framework, the CCS’s 20 Critical Security Controls, and the Australian Signals Directorate’s Strategies to Mitigate Targeted Cyber Intrusions. Tenable’s continuous network monitoring solution supports these industry guidelines as well as the Cyber Hygiene Campaign’s top priorities.
Continuous network monitoring
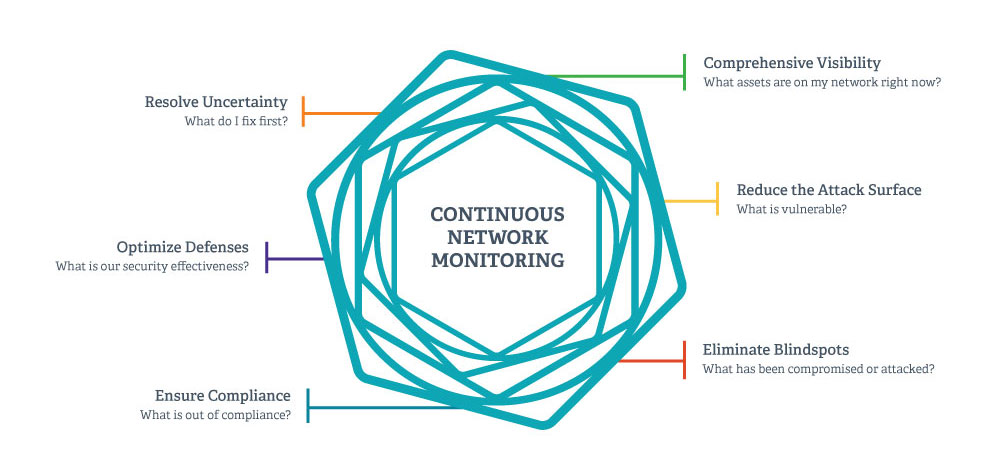
Can you answer these questions for your organization?
Continuous network monitoring—the automated process used to manage and measure an organization’s security, compliance, and risk—can help you answer these questions. And it also helps you implement the top priorities for good cyber hygiene.
Tenable’s continuous network monitoring platform, SecurityCenter Continuous View™ (SecurityCenter CV™), resolves uncertainty by providing prioritized, actionable security and compliance data. SecurityCenter CV identifies the most critical vulnerabilities across your organization, so you can prioritize remediation efforts and reduce risk.
The benefits of continuous network monitoring include:
- Reducing the attack surface by identifying all known assets on your network and the vulnerabilities present on each asset
- Eliminating blindspots through continuous discovery and detection of unknown assets, threats, and when controls fail
- Comprehensive visibility across your ever-changing IT infrastructure
- Optimizing defenses with integrated, context-based security metrics and reporting
- Ensuring compliance by continuously assessing and demonstrating compliance with security regulations, frameworks, and policies
Learn more about how Tenable can help
Continuous network monitoring with SecurityCenter CV supports good cyber hygiene by discovering devices and their vulnerabilities, performing configuration audits, tracking remediation progress, monitoring the network for unauthorized or malicious activity, and measuring compliance.
Continuous network monitoring with SecurityCenter CV supports good cyber hygiene
For an overview of how cyber hygiene is simplified using Tenable, view the Cyber Hygiene solution brief. For detailed information on how Tenable helps meet the Cyber Hygiene Campaign’s top priorities, download the Tenable Solutions for the Cyber Hygiene Campaign technical paper.
If you would like to evaluate how Tenable’s continuous network monitoring solution can help your organization, please contact us or your local authorized Tenable reseller.
Learn more
- Security Frameworks
- Security Policy
- Standards



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success