How to Improve Your Cybersecurity Decision-Making to Reduce Business Risk

Increase your program efficacy by identifying the metrics that offer the right context to aid decision making across the executive, strategic and tactical levels of your organization.
The challenges for security teams continue to increase in the face of ever-changing environments and attackers leveraging the speed and scalability of modern IT environments. The pace and complexity of these changes ushers in a new chapter in the evolution of information security teams; today, security teams must also become risk management experts. Whether you're a team of one or many, you're faced with making decisions across multiple levels of your organization in order to more effectively mitigate risk.
In our latest whitepaper, 3 Levels of Security Strategy for Business Risk Decisions, we dive into the three levels of decision-making strategies security teams need to perform:
- executive;
- strategic; and
- tactical
The decision-making process across each of these levels involves much nuance and can be complex. Here, we'll show you some examples of the types of decisions required at each level and how the right metrics and tools can help you improve decision-making across all three levels in order to uplevel your security program efficacy.
Executive-level decisions
At the executive level, security leaders deal with two different sub-areas of decision-making support: relaying information and metrics about the organization's security and risk posture to their C-suite business counterparts; and for their own executive-level decisions to provide direction and support for their security team.
In support of their C-suite peers, security executives will typically ask their security teams for a wide variety of information to help guide business, revenue and liability decisions that affect the entire organization. To improve decision making at this level, the metrics provided by the security team must be risk based and framed in a way that aligns with business drivers.
For example, because business leaders need security information to be communicated within the broader context of the organization's goals, they won't find much value looking at the raw number of malware programs blocked by endpoint protection software or the total number of vulnerabilities patched this month. These represent a total volume number without any business context. Instead, security leaders should consider looking at the percentages of discovered critical risk vulnerabilities eliminated within the established Service Level Agreement (SLA) timeframe or the trend of risk reduction broken out by a major business function, such as the organization's primary e-commerce website, or the main data center in New York.
Viewing security performance through a broader lens enables security leaders to provide valuable context to business executives, so they can see how the security program is being effective and decide if there are areas where they must invest more resources to further mitigate and reduce risk within the business.
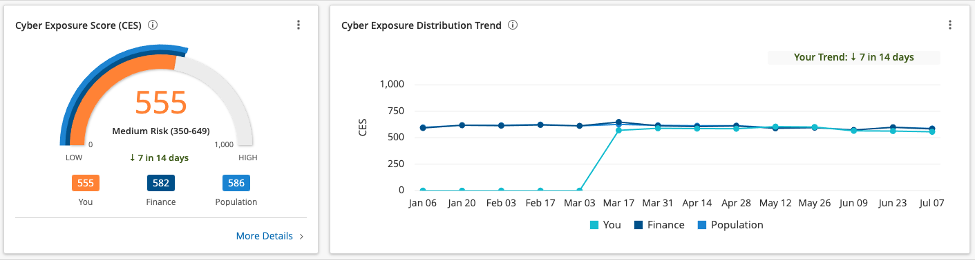
These same metrics, when viewed through the lens of solely the security team's perspective, represent the amalgam of all the efforts being driven by all members and decision-making levels of the team. In this way, CISOs and other executive-level security leaders can measurably determine if the vision for the security team is being successfully realized by other team members and that the strategic- and tactical-level decisions are effective in reducing risk in a tangible way. Of course, if these metrics are showing a downward trend, this allows for security leaders to course correct and identify areas that need more management support in order to clear obstacles, acquire more resources, hire more staff or bring in additional, outside assistance.
Strategic-level decisions
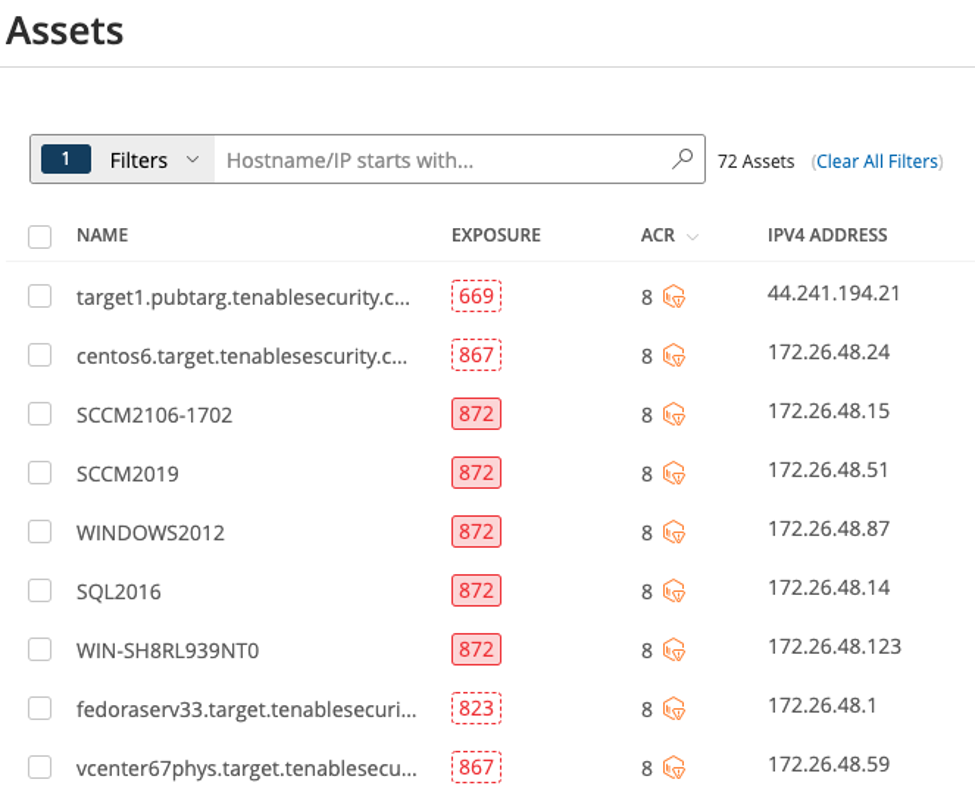
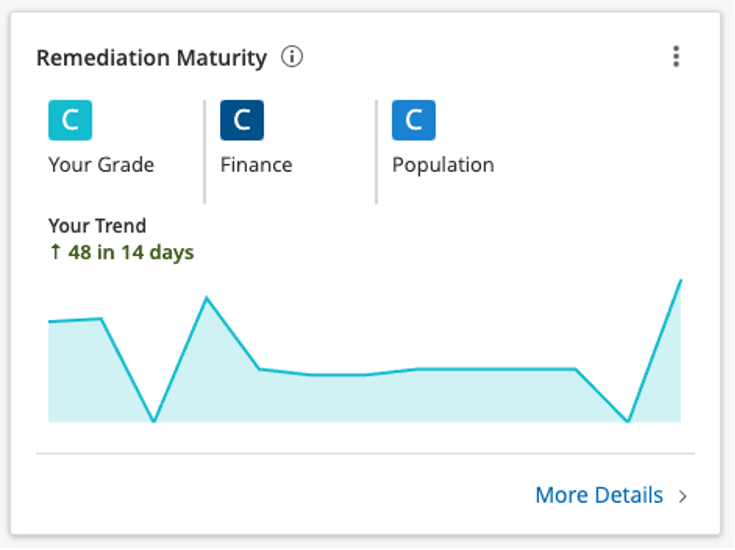
As you move down the org chart within the security team, the strategic-level decision makers (commonly directors, team leads or other mid-tier managers, but can also be senior technical experts or analysts) must support the executive-level teams to make better decisions for the overall direction of the business while also helping the tactical-level teams be more efficient and effective in their remediation efforts to reduce risk.
Prioritization of risk is key to best support the tactical-level teams, where the day-to-day operational decisions are critical to ensure the organization is focusing resources on the most critical areas where remediation will have the biggest impact. As you work to translate the business requirements to operational execution, asset criticality is key to understand not only where to reduce the most critical risks to the business overall, but to help operational teams prioritize their work efforts more efficiently and effectively.
By understanding the business criticality of assets in your organization, whether by location of the asset, exposure to the internet, the type of device, what business function it supports, or any number of other factors, you can apply a more risk-based approach to your remediation workflows.
For the overall management of your security program, it's also important to understand whether or not the policies, processes and procedures are working as expected and are helping increase maturity over time. It's important that strategic-level decisions support the other two levels of decision making. By constantly refining and improving the security program through better strategic decisions, one can demonstrate that the program is effective and that it is continuing to improve, which is an important indication of business value for executive-level decision makers. Having executives understand that there is business value in what you're doing to improve the security program is not just critical to the team's success, but can be used to support requests for additional budgetary and staffing allotments. It's here, then, that measuring the effectiveness of your assessment and remediation processes from a maturity standpoint not only allows for the strategic-level decision maker to shuffle resources where needed to improve these workflows, but also supports the overall business requirements to continuously reduce risk and drive more ROI through efficiency and process optimizations.
Tactical-level decisions
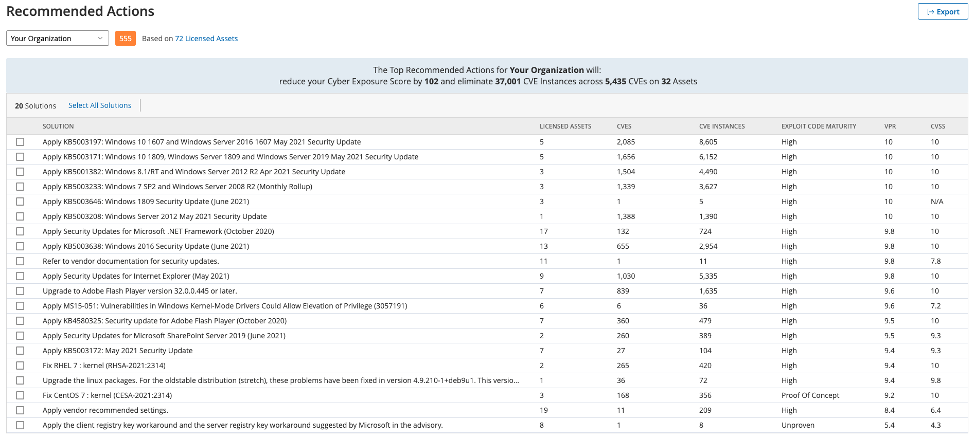
Whether or not the security team is directly involved in the operational execution of active remediation efforts, they still play a critical role in helping execute these day-to-day patching and remediation tasks effectively and efficiently.
By translating security findings into specific recommendation steps, the security team can make it easier for the operations teams to quickly understand what needs to be done and efficiently build the proper workflow to perform the necessary remediation steps. A more seamless integration between the security and operational processes here means improved program efficacy overall, which creates better value and reduces more tangible risk to the organization.
Each level brings its own unique challenges when it comes to decision making. But armed with the right insights and perspectives, you can make — and demonstrate — tangible improvements in program efficacy.
Learn more
- Read the whitepaper: 3 Levels of Security Strategy for Business Risk Decisions
- Register for the webinar: Improve Your Security Strategy: Master the 3 Levels of Decision Making
- Watch the videos: Measure Program Efficacy with Tenable Lumin
- Executive Management
- Risk-based Vulnerability Management
- Vulnerability Management
- Vulnerability Scanning


