GRIZZLY STEPPE Detection with SecurityCenter

Note: Tenable SecurityCenter is now Tenable.sc. To learn more about this application and its latest capabilities, visit the Tenable.sc web page.
Governments and businesses around the world are always potential targets for spear phishing campaigns and APTs like GRIZZLY STEPPE. On December 29, 2016 the U.S. Department of Homeland Security (DHS) and Federal Bureau of Investigation (FBI) released a Joint Analysis Report (JAR-16-20296) which included technical details about activity tied to exploitation and the eventual compromise of systems within the United States. The U.S. government is referring to this malicious cyber threat as GRIZZLY STEPPE. The Joint Analysis Report includes GRIZZLY STEPPE indicators of compromise such as a YARA rule and suspicious IP addresses and DNS names. Global organizations must be vigilant about detecting these latest indicators of compromise. SecurityCenter® can easily scan for these indicators and alert on any detections.
How does GRIZZLY STEPPE work?
GRIZZLY STEPPE follows a familiar attack pattern. It targets unsuspecting users with a spear phishing campaign, enticing them to click on a malicious link. As soon as the link is clicked, malicious code is delivered and executed, establishing persistent remote access to that system via a Remote Access Tool (RAT), typically in the form of a web shell.
Once a persistent connection has been established, the next step usually involves escalating privileges and enumerating Active Directory accounts, leading to all sorts of nefarious activity.
Indicators of compromise
The Joint Analysis Report released by DHS and FBI included many Indicators of Compromise (IOCs) which organizations can use to assess if their systems have been compromised. The chief indicator among them is a YARA rule which detects a PHP web shell which was used as part of the GRIZZLY STEPPE campaign.
Here’s the YARA rule :
rule PAS_TOOL_PHP_WEB_KIT
{
meta:
description = "PAS TOOL PHP WEB KIT FOUND"
strings:
$php = "<?php"
$base64decode = /\='base'\.\(\d+\*\d+\)\.'_de'\.'code'/
$strreplace = "(str_replace("
$md5 = ".substr(md5(strrev("
$gzinflate = "gzinflate"
$cookie = "_COOKIE"
$isset = "isset"
condition:
(filesize > 20KB and filesize < 22KB) and
#cookie == 2 and
#isset == 3 and
all of them
}
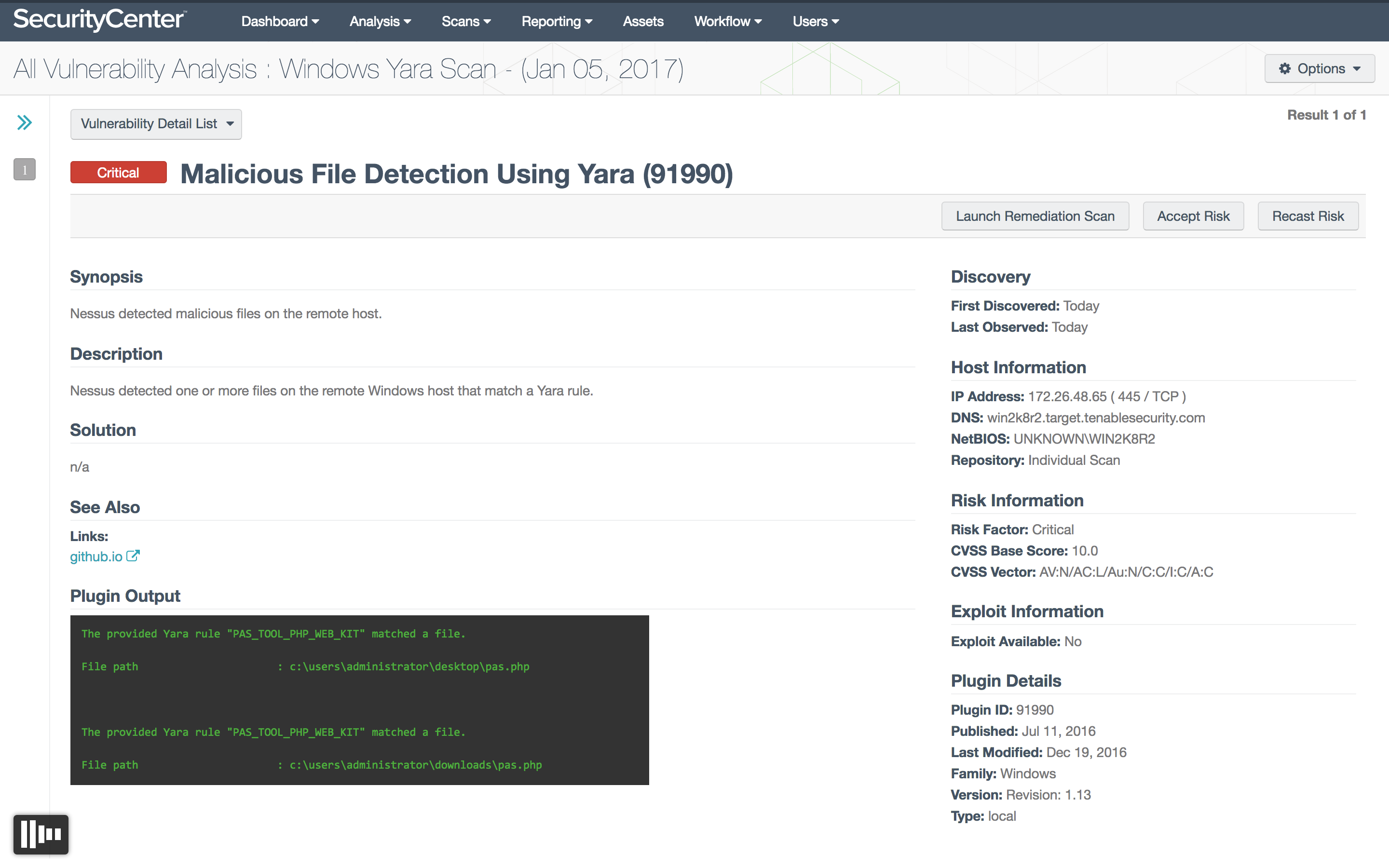
Tenable’s YARA pattern detection
Last year Tenable released SecurityCenter functionality to look for malicious files based on textual and binary patterns as defined by a YARA rule. You can use this functionality to detect the malicious PAS PHP web shell identified in the Joint Analysis Report on Windows systems. Here is a sample scan based on the GRIZZLY STEPPE YARA rule:
Create a Yara scan policy
- Click Scans -> Policies -> Add.
- Select Malware Scan.
- Enter a scan name.
- Click Malware and enable File System Scanning.
- Select the desired Directories and upload the Yara Rules File.
- Click Submit.
- Create and run a scan using the new policy.
You can also run a similar YARA scan in Nessus®. Refer to Threat Hunting with YARA and Nessus for instructions on creating a YARA scan in Nessus®.
Suspicious IP/DNS event analysis with SecurityCenter
In addition to the YARA rule, the Joint Analysis Report also included IP addresses and DNS names tied to malicious actors related to the GRIZZLY STEPPE campaign. While many false positives have been reported with these IP addresses and DNS names, you may still want to scan for them or use new more reliable sources if they become available. Using SecurityCenter, you can define a custom Watchlist asset list to look for any events within your organization which are tied to these suspicious IP addresses as follows:
Create a new asset list
- Click Assets -> Add -> Custom -> Watchlist.
- Create a file containing the IP addresses.
- Assign a name to the asset list, such as Grizzly Steppe IPs.
- Click Submit.
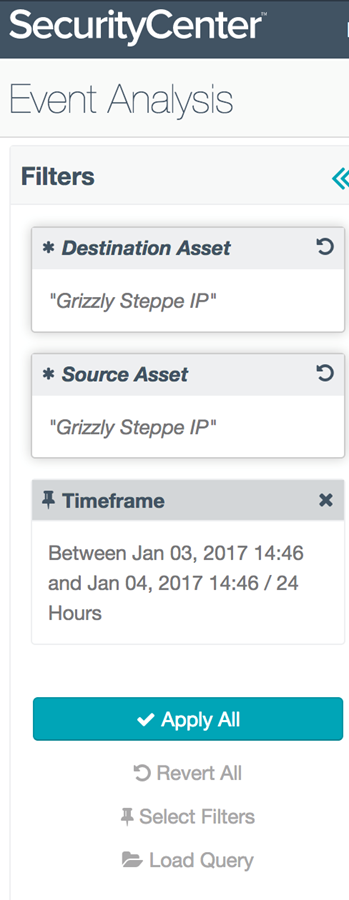
Analyze events
- Click Analysis -> Events.
- Configure Event Analysis to include Destination Asset and Source Asset.
- Select Grizzly Steppe IPs as the asset to watch.
- Select a timeframe of events to monitor.
- Click Apply All, and review the events.
Follow similar steps to create assets for malicious DNS names, with the caveat that you may get many false positives.
In addition to Watchlists, you can also add custom IPs, URLs or domains to the built-in threat detection in LCE®. This is done by creating custom files in the LCE plugins directory. Refer to the Tenable Community Discussion for more details.
Protecting your systems
Review activity to and from any suspicious IP addresses related to GRIZZLY STEPPE, especially if it appears to be performing a vulnerability scan. For any public facing Windows systems, run a scan with the YARA signature listed above and review any activity that might indicate a compromise.
Thanks to Rich Walchuck, John Chirhart and Andrew Flick for their contributions to this blog.
Learn more
- Government
- LCE
- Malware
- Nessus
- SecurityCenter
- Vulnerability Scanning



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success