CVE-2020-0688: Microsoft Exchange Server Static Key Flaw Could Lead to Remote Code Execution
Attackers are probing for vulnerable Microsoft Exchange Servers, as details surrounding a severe flaw were recently made public.
Update 02/27/2020: The proof-of-concept section has been updated to reflect the availability of several exploit scripts, including those that can be used to automate exploitation.
Background
On February 11, Microsoft released a patch for a severe vulnerability in Microsoft Exchange Server as part of its monthly Patch Tuesday updates. Initially, Microsoft labeled this a memory corruption vulnerability in Microsoft Exchange. However, Microsoft has since updated the title and description for the flaw.
Analysis
CVE-2020-0688 is a static key vulnerability in Microsoft Exchange Control Panel (ECP), a component of Microsoft Exchange Server. The use of static keys could allow an authenticated attacker with any privilege level to send a specially crafted request to a vulnerable ECP and gain SYSTEM level arbitrary code execution.
Microsoft rates this flaw as important, but notes that exploitation is more likely, according to its exploitability index.
Vulnerability details
According to researchers at the Zero Day Initiative (ZDI), Microsoft Exchange Server installations “have the same validationKey and decryptionKey” in the MachineKeySection of the web configuration (web.config). As the ZDI notes, these keys are used to secure server-side data stored in serialized form in the ViewState, which is included as part of the requests from the client in the “__VIEWSTATE” parameter. (If this sounds familiar, it’s because we recently blogged about an improper input validation vulnerability in Microsoft SQL Server Reporting Services that also involved serializing untrusted data through the VIEWSTATE parameter.)
To generate a malicious request, the attacker would need to obtain the following parameter values:
| Parameter | Location |
|---|---|
| validationKey | System.Web.Configuration |
| validation | System.Web.Configuration |
| VIEWSTATEGENERATOR | Exchange Control Panel Source |
| ASP.NET_SessionId | Cookie Field in Request Header |
While the first two parameters are static and easily obtainable, the last two parameters require an attacker to log in to the vulnerable ECP instance with valid user credentials. Only then could the attacker capture these parameters from the HTML source and the cookie field in the request header.
Once an attacker has obtained these values, they can generate a serialized payload using ysoserial.net as part of their malicious request to a vulnerable ECP instance.
In their blog, the ZDI shared a YouTube video demonstrating exploitation of this flaw.
Valid user credential requirement
As part of a Twitter thread about the vulnerability, security researcher Kevin Beaumont noted that authentication is “not a big hurdle.” He also noted the availability of tools that can capture employee information from LinkedIn pages and use them to target Outlook Web Access (OWA) “with authentication attempts via credential stuffing.” Beaumont said the tools are “used in active attacks, to gain OWA and ECP access.”
There are open source tools which take the input of a company page on LinkedIn, dump all the employee names then hammer Outlook Web App with authentication attempts via credential stuffing.
— Kevin Beaumont (@GossiTheDog) February 25, 2020
These tools are used in active attacks, to gain OWA and ECP access.
Organizations behind in patching
Microsoft provides a way to identify Exchange Server build numbers through the login pages of OWA and ECP, enabling attackers to identify which servers are potentially vulnerable to CVE-2020-0688.
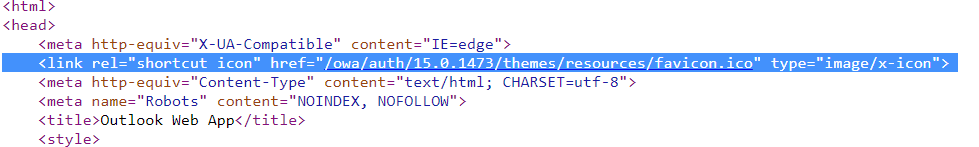
Beaumont found through “a quick sample” that organizations were “averaging in the years rather than months behind” in patching their Exchange Server instances, which is a major concern.
One additional thing - you can see the patch version of Exchange in the ECP and OWA login pages, so expect some sweeping of the internet for this (patch rates) in coming weeks.
— Kevin Beaumont (@GossiTheDog) February 25, 2020
I just did a quick sample, orgs are averaging in the years rather than months behind with Exchange.
Attackers probing for vulnerable Microsoft Exchange Servers
Soon after the ZDI’s blog post was published, attackers began probing for vulnerable Microsoft Exchange Servers.
Troy Mursch, chief research officer at Bad Packets, tweeted that “mass scanning activity has begun” for this vulnerability.
CVE-2020-0688 mass scanning activity has begun. Query our API for "tags=CVE-2020-0688" to locate hosts conducting scans. #threatintel
— Bad Packets Report (@bad_packets) February 25, 2020
Beaumont himself also identified mass scanning activity for the vulnerability based on data from BinaryEdge.
That was quick, since 2 hours ago seeing likely mass scanning for CVE-2020-0688 (Microsoft Exchange 2007+ RCE vulnerability). pic.twitter.com/Kp3zOi5AOA
— Kevin Beaumont (@GossiTheDog) February 25, 2020
Proof of concept
Details to craft a proof-of-concept for this vulnerability can be found in the ZDI’s blog post. Additionally, several exploit scripts were recently shared on GitHub [1, 2, 3] that can automate exploitation so long as the user has valid credentials.
Solution
Microsoft released patches for this vulnerability during Patch Tuesday on February 11, 2020, for Microsoft Exchange Server 2010, 2013, 2016 and 2019. Though unconfirmed, this may also affect Microsoft Exchange Server 2007, which reached end of life in April 2017.
| Microsoft Exchange Server Version | Support Article |
|---|---|
| 2010 Service Pack 3 | 4536989 |
| 2013 Cumulative Update 23 | 4536988 |
| 2016 Cumulative Update 14 | 4536987 |
| 2016 Cumulative Update 15 | 4536987 |
| 2019 Cumulative Update 3 | 4536987 |
| 2019 Cumulative Update 4 | 4536987 |
Identifying affected systems
A list of Tenable plugins to identify this vulnerability can be found here.
Get more information
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management


