Microsoft’s February 2020 Patch Tuesday Addresses 99 CVEs Including Internet Explorer Zero-Day (CVE-2020-0674)
Microsoft smashes the CVE count with security patches for 99 CVEs, 12 of which are rated as critical.
Update 02/25/2020: Updated the section for CVE-2020-0688 to reflect a correction to Microsoft's original advisory description.
Microsoft addresses a staggering 99 CVEs in the February 2020 Patch Tuesday release. This update contains 17 remote code execution flaws and 12 vulnerabilities rated as critical. This month’s updates include patches for Microsoft Windows, Microsoft Office, Microsoft Edge, Internet Explorer, Microsoft Exchange Server, Microsoft SQL Server, Microsoft Office Service and Web Apps, Windows Malicious Software Removal Tool and Windows Surface Hub. The following is a breakdown of the most important CVEs from this month’s release.
CVE-2020-0673 and CVE-2020-0674 | Scripting Engine Memory Corruption Vulnerability
CVE-2020-0673 and CVE-2020-0674 are both remote code execution vulnerabilities due to the way in which the scripting engine handles objects in memory in Internet Explorer. Exploitation of these vulnerabilities could allow an attacker to corrupt memory and execute arbitrary code with the same level of privileges as the current user. CVE-2020-0674 was first noted as being exploited in the wild in January, where Microsoft released an out-of-band advisory (ADV200001). The advisory provided mitigation steps at that time. However, this month, Microsoft provided an update to correct these vulnerabilities, which modifies how the scripting engine handles objects in memory.
According to Google Project Zero researcher Maddie Stone, CVE-2020-0674 is the “3rd attempt” to patch this vulnerability after it had been patched two times before. The previous CVEs associated with this vulnerability are CVE-2019-1367 and CVE-2019-1429. CVE-2019-1367 was originally patched out-of-band in September 2019 after exploitation had been observed in the wild, while CVE-2019-1429 was patched in Microsoft’s November 2019 Patch Tuesday and also observed to be exploited in the wild.
CVE-2020-0674 is patched today after in-the-wild exploitation detected by @_clem1 of Google TAG. This is now the 3rd attempt to patch this bug after 2 misfixes (CVE-2019-1367/CVE-2019-1429). We have to fix these bugs the 1st time, especially when they've been exploited itw.
— Maddie Stone (@maddiestone) February 11, 2020
CVE-2020-0662 | Windows Remote Code Execution Vulnerability
CVE-2020-0662 is a remote code execution vulnerability wherein an attacker with a domain account could manipulate Windows’ memory handling to execute injected code. The attacker could leverage the domain account to execute this attack from within the target network, without needing to directly log in to the affected device.
CVE-2020-0681 and CVE-2020-0734 | Remote Desktop Client Remote Code Execution Vulnerability
CVE-2020-0681 and CVE-2020-0734 are both remote code execution vulnerabilities within the Windows Remote Desktop Client. An attacker can exploit these flaws to execute arbitrary code on the connecting client. This requires the attacker to convince a user to connect to a malicious server or have control over a server that a user could be persuaded to connect to. While these CVEs are not reportedly exploited in the wild, Microsoft does rate these as Critical and label them as ‘Exploitation More Likely.’
CVE-2020-0655 | Remote Desktop Services Remote Code Execution Vulnerability
CVE-2020-0655 is a remote code execution vulnerability in Remote Desktop Services that allows an authenticated attacker to abuse clipboard redirection. If an attacker manages to successfully exploit this vulnerability, it could result in the execution of arbitrary code on the target system, allowing not only the viewing, alteration and deletion of data, but also the ability to install applications and create new users with admin-level privileges. For an attacker to exploit this vulnerability, they must already have compromised the target system running Remote Desktop Services and wait for a victim to connect to the service.
CVE-2020-0660 | Windows Remote Desktop Protocol (RDP) Denial of Service Vulnerability
CVE-2020-0660 is a denial of service (DoS) vulnerability in Windows RDP in which an attacker could connect to a target system using RDP while sending malicious requests in such a way that the protocol ceases to function. This could be used to stop administrators from connecting to critical infrastructure during an attack or isolate targets after infection.
CVE-2020-0688 | Microsoft Exchange Validation Key Remote Code Execution Vulnerability
CVE-2020-0688 is a remote code execution vulnerability in Microsoft Exchange server which occurs due to the server failing to create unique keys during installation. An attacker with knowledge of the validation key and a valid Exchange user account with any privileges could pass arbitrary serialized obejcts to a vulnerable Exchange server and run commands as the system user.
CVE-2020-0683 and CVE-2020-0686 | Windows Installer Elevation of Privilege Vulnerabilities
CVE-2020-0683 and CVE-2020-0686 are elevation of privilege vulnerabilities that exist in the Windows Installer when MSI packages process symbolic links. An attacker who successfully exploits this vulnerability could bypass access restrictions and add or remove files. To exploit this vulnerability, the attacker first needs to be able to log on to the target system and then execute a specially crafted application.
CVE-2020-0706 | Microsoft Browser Information Disclosure Vulnerability
CVE-2020-0706 is an information disclosure vulnerability in Microsoft browsers that affects how cross-origin requests are handled. An attacker who successfully exploits this vulnerability could ascertain the origin of all webpages visited in the vulnerable browser. For an attacker to exploit this vulnerability, they would have to insert specially crafted content on either a malicious website or a compromised website, and convince a victim to visit the malicious site and view the content.
CVE-2020-0738 | Windows Media Foundation Memory Corruption Vulnerability
CVE-2020-0738 is a memory corruption vulnerability in Windows Media Foundation. An attacker would need to trick a user into visiting a malicious webpage or open a malicious file. Once compromised, the attacker could completely modify local Windows user settings and therefore become an administrator on the target machine.
CVE-2020-0689 | Microsoft Secure Boot Security Feature Bypass Vulnerability
CVE-2020-0689 is a security feature bypass vulnerability in Microsoft’s implementation of Secure Boot. An attacker could exploit the flaw by running a specially crafted application, which would result in the bypass of secure boot, allowing the attacker to load untrusted software. Prior to applying the standalone security updates for this vulnerability, Microsoft advised the following prerequisite Servicing Stack Updates be installed.
| Product | Servicing Stack Update Package | Date Released |
|---|---|---|
| Windows Server 2012 | 4523208 | November 2019 |
| Windows 8.1/Server 2012 R2 | 4524445 | November 2019 |
| Windows 10 | 4523200 | November 2019 |
| Windows 10 Version 1607/Server 2016 | 4520724 | November 2019 |
| Windows 10 1709 | 4523202 | November 2019 |
| Windows 10 1803/Windows Server, version 1803 | 4523203 | November 2019 |
| Windows 10 1809/Server 2019 | 4523204 | November 2019 |
| Windows 10 1903/Windows Server, version 1903 | 4538674 | February 2020 |
| Windows 10 1909/Windows Server, version 1909 | 4538674 | February 2020 |
CVE-2020-0757 | Windows SSH Elevation of Privilege Vulnerability
CVE-2020-0757 is an elevation of privilege vulnerability due to a flaw in how Windows handles Secure Socket Shell (SSH) remote commands. To exploit this flaw, an attacker would need to first log onto a system and execute a crafted application. This would allow an attacker to execute privileged commands with a lower-level user account.
Tenable Solutions
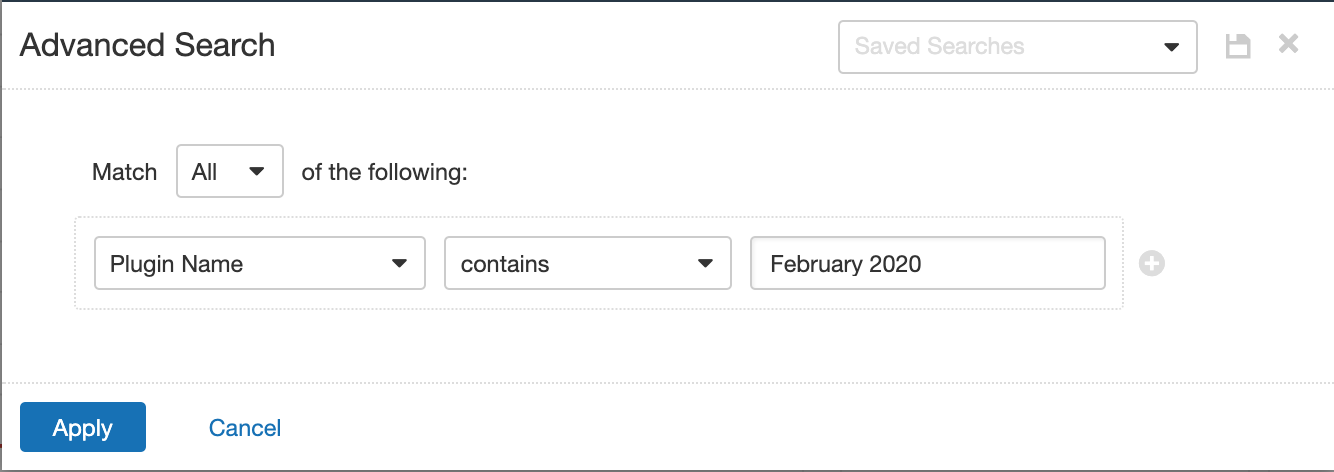
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name Contains February 2020.
With that filter set, click the plugin families to the left, and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
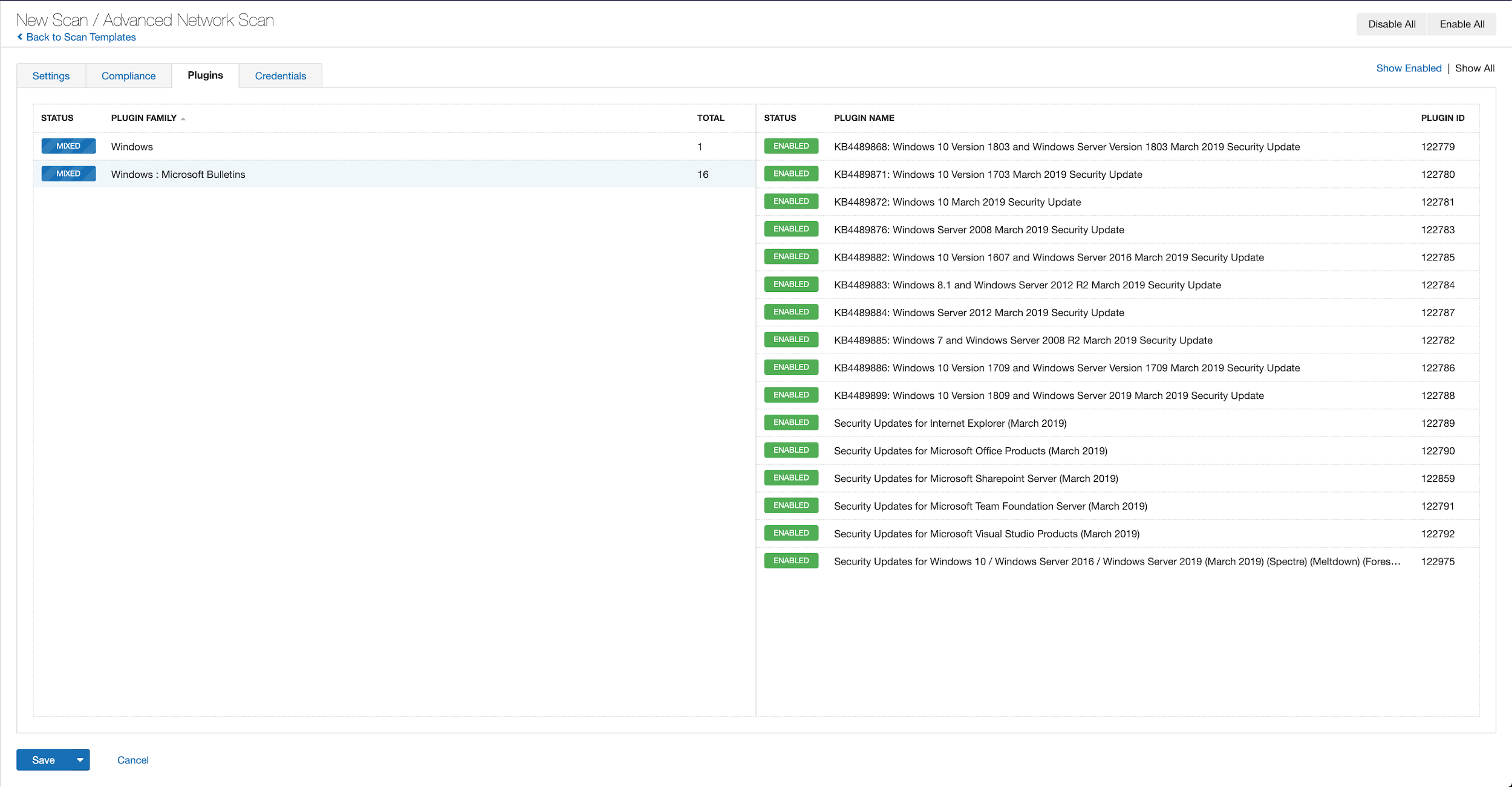
A list of all the plugins released for Tenable’s February 2020 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
Get more information
- Microsoft's February 2020 Security Updates
- Tenable plugins for Microsoft February 2020 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success