Cloud Security: 3 Things InfoSec Leaders Need to Know About the Shared Responsibility Model

Whether you’re just beginning your cloud journey or have years of deployments under your belt, it’s worth taking the time to make sure you’re clear on which aspects of security in the cloud fall to your cloud service provider and which are the domain of your security organization.
As 2020 draws to a close, organizations worldwide are forced to grapple with the realization that quick changes made earlier in the year in response to the Covid-19 pandemic may be here to stay. For some, this could mean a strategic move to double down on their use of cloud services, including infrastructure-as-a-service (IaaS), platform-as-a-service (PaaS) and software-as-a-service (SaaS).
The advantages of moving to the cloud are clear in today’s environment, in which providing employees with remote access to the critical tools and data they need to do their jobs is essential for keeping an organization up and running. Earlier this year, a commissioned global study conducted by Forrester Consulting on behalf of Tenable found that nearly two thirds of organizations (64%) have remote/work-from-home employees. The study also revealed a complex mix of technologies and services being managed by the 416 security executives surveyed, including public cloud (41%), private cloud (45%) and hybrid (39%). As the need for a fully functional remote workforce continues, we anticipate even more organizations adding to their cloud portfolios in 2021 and beyond.
Whether you’re just beginning your cloud journey or have years of deployments under your belt, it’s worth taking time to make sure you’re clear on which aspects of security in the cloud fall to your cloud service provider and which are the domain of your security organization. As with so much in information technology, the answers can vary widely depending on which flavor of cloud technology you’re deploying. Here’s a quick breakdown of what the shared responsibility model looks like for three main cloud computing tiers, based on guidance from the Cloud Security Alliance:
- IaaS: In this tier, the security burden on the cloud service provider (CSP) includes virtualization security and infrastructure security. Areas such as data security, application security, middleware security and host security fall to the IaaS customer. Simply put: users are responsible for the guest OS and everything inside of it.
- PaaS: In this tier, the CSP’s responsibilities are broader, including: security configuration, management, operating monitoring, and emergency response of infrastructure; security of virtual networks; security of the platform layer, such as the security of operating systems and databases; and security of application systems. The PaaS customer is responsible for data security and application security.
- SaaS: In this tier, the CSP is responsible for security of the application and underlying components. The SaaS customer is responsible for data security and endpoint device protection.
The example below, from Microsoft, illustrates a typical shared responsibility model:
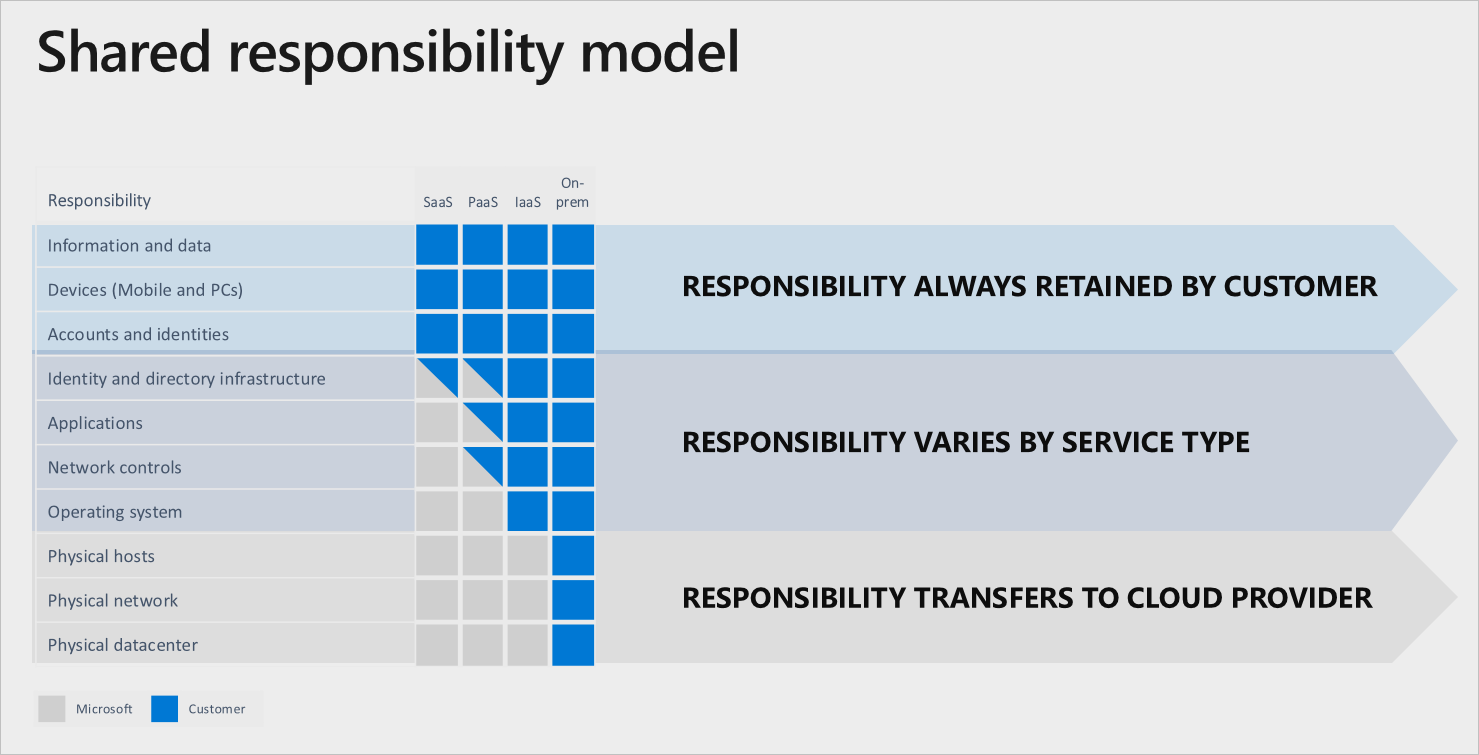
Image Source: https://docs.microsoft.com/en-us/azure/security/fundamentals/shared-responsibility
While the shared responsibility model at a glance may look fairly straightforward, security professionals need to prepare for considerable nuance within each tier. For example, vulnerability management for IaaS deployment models can be particularly difficult and time consuming. Security teams require a full inventory of virtual private clouds (VPCs) and Elastic Compute 2 (EC2) image pipelines to get started. Scanners and agents need to be configured, installed and continuously managed to incorporate updates. New vulnerability detections can lag for several weeks. And if this weren’t challenging enough, security professionals have to account for numerous blind spots due to unknown cloud accounts and dynamic cloud environments that are constantly changing.
Another concern for security professionals is understanding that the security of the storage infrastructure is the responsibility of the CSP but users have a significant impact as well. Misconfigurations — whether in S3 buckets or EC2 instances — are a primary cause of breaches.
Further, the shared responsibility details can vary depending on whether your CSP is Amazon Web Services (AWS), Google Cloud Platform (GCP) or Microsoft Azure. In addition to the guidelines available from the Cloud Security Alliance, resources for understanding your security team’s role in the shared responsibility model are also available from the Center for Internet Security.
Shared Responsibility in the Cloud: 3 Things Cybersecurity Leaders Need to Know
IDG’s 2020 Cloud Computing Study, which polled 551 IT decision-makers (ITDMs), found that the vast majority of respondents (81%) are already using computing infrastructure or applications in the cloud and another 12% plan to adopt cloud-based applications in the next 12 months. If you’re among them, here are three things to keep in mind about the shared responsibility model:
- Although it may seem equal on paper and in visuals, a significant amount of responsibility, implementation and attack surface defense (?) is still on the customer. Don’t underestimate the time and resources you’ll need to invest for each cloud deployment — including any necessary training to bring your team up to speed.
- Certain audit and compliance categories (control families) are made easier by shifting to the cloud via inherited controls from the cloud provider. Inherited controls can include patch management and configuration management and can translate to noticeable cost savings. While your infosec team should drive this strategy, it’s important to engage with other key groups in your organization, particularly the governance, risk and compliance (GRC) and legal departments. The internal audit team can prove especially helpful here. According to a 2018 Deloitte report, “while an organization’s information security group can build cloud monitoring capabilities, [the internal audit team] can assist and assess the effectiveness of the control environment and prevent the IT department being left out of the loop.”
- Don’t assume the cloud provider holds sole liability in the event of a breach. Even if a scenario were to happen where the cloud provider was found to be at fault, the fallout would still potentially extend to your customers and your organization could be named in and class action lawsuits. In many jurisdictions, legal liability falls to the data owner (ie. the organization using the cloud services) rather than the CSP itself. In short, don’t be complacent. Paying attention to your role in the shared responsibility model can do more than keep your data secure; it can protect your organization in the event of a lawsuit.
Forrester predicts that, in 2021, “cloud computing will power how companies adapt to the ‘new, unstable normal.’ ” Now is the time to closely evaluate any cloud solutions hastily put in place earlier this year and revisit services you’ve had in place for a while to ensure that you’re fulfilling all your security obligations under the shared responsibility model.
Learn More:
- Attend the webinar: Frictionless Assessment of EC2 Assets
- Download the solution brief: Frictionless Assessment of AWS Assets
Learn more
- Cloud
- Tenable Vulnerability Management
- Vulnerability Management
- Vulnerability Scanning



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success