Auditing More Network Devices Offline with Nessus
Let’s do a show of hands. How many network administrators go through a security audit without experiencing some anxiety?
Anyone?
I am guessing not many. And I can understand why.
The problem
In most cases, network administrators don't have the liberty to run the audit themselves; they have to share credentials for critical network infrastructure with a separate audit team. Which means some other team is going to run an audit against the network, and if for some reason one of the devices — say a router or a switch — goes down, we all know how the blame game gets played out. In the end, you as the network administrator are responsible for making sure that the network is up and running (audit or no audit). I remember one of my friends once jokingly said that every time he saw the "Typing..." status in his IM window from the audit team, his heart started racing, wondering what crisis was coming at him next.
Network administrators don't have the liberty to run the audit themselves
But the issue is not one sided. Nobody likes to willingly bring down a network (unless, of course, there is malicious intent). Auditors just want to do their job and be done with it just as fast as the administrators want to be done with it, too. But they are plagued with a myriad of issues; one of them is incomplete reports, which might force them to run the scan more than once. For example, scanning a router or a firewall during times of high traffic could result in a partial response or — even worse — no response at all. In some cases, pagination issues could result in a partial configuration, resulting in an incomplete audit. And finally, some devices could simply be out of scope for the scan because of their significance within the network.
Auditing against configuration files with offline auditing
These are all real problems, significant problems that we first encountered when developing Nessus® audits for network devices such as Cisco and Junos in 2009.
We introduced a concept called "offline auditing" for network devices.
We kept working at it and found an interesting solution. We thought, what if a network administrator hands off the router/firewall/switch configuration to the audit team, and the auditor just audits the configuration instead? It does the same thing as a regular audit, except there is no need to share credentials or create accounts, no risk of down time, it guarantees complete results, and above all else, everyone gets to keep their jobs and be happy.
Early last year we introduced a concept called "offline auditing" for network devices. Basically as an administrator, you would run the show config (or its equivalent) command on the device, and then hand the result off to the audit team. The audit team in turn would take the configuration, run it past pre-canned lists of checks recommended by CIS, DISA and other industry standard guides, test for compliance, and be done. This feature was well received, and has now been included in all network audit compliance plugins for Nessus. You can read more about offline auditing in our Discussion Forums.
New Nessus plugins
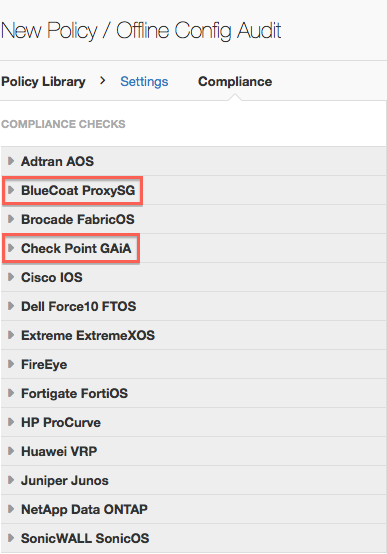
With the release of Nessus 6.2, this feature was also included in the new plugin for BlueCoat Proxy SG, and for CheckPoint GAiA, which until now didn't have this feature.
Auditors can also use this feature in combination with the “known good” feature to create a baseline reference scan and to track changes to configurations from one scan to another. You can read more about the known good feature in the Nessus Discussion Forum.
At Tenable, we work on a range of features, each one designed to solve a unique problem for our end users. We hope that features like offline auditing and known good help you solve everyday problems, and find their way into your daily workflow. As always, we appreciate feedback for improvements or support for devices that aren’t already covered.
Learn more
- Plugins
- Security Frameworks
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success