Auditing Network Devices Without Scanning
The title of this post might seem a bit odd, but it is true. Nessus is now able to audit network devices without scanning the devices.
Network device auditing can be difficult for several reasons.
- The network department may be very protective of the organization’s network infrastructure equipment and the credentials to those systems. Rightfully so as those devices are the foundation of the network. This underscores the importance of the security of these devices as well, including patch and configuration management.
- The devices do not support secure remote access.
- The devices may be in locations which simply aren’t accessible from the scanners.
- Pagination issues or improper implementation of SSH RFC.
The problem has been that the security team needs the credentials and access to the network systems to perform audits, but Nessus now solves this problem. Nessus can now perform configuration auditing against device configuration files, rather than the systems themselves. This means you can request the configuration files from your network administrators and test the configurations for security. A very powerful benefit of this feature is that users can now make proposed changes in the configurations and test the security of the changes before they go into production, making it easier to test and deploy securely configured devices throughout the network.
Making this new feature even more powerful is the option to upload a zip file with one or more configuration files and audit the individual configuration files, reporting on each device’s configuration separately. The plugin reports file-name as hostname/IP address of the network device and the results appear the same as if Nessus had performed a credentialed scan of the devices(s).
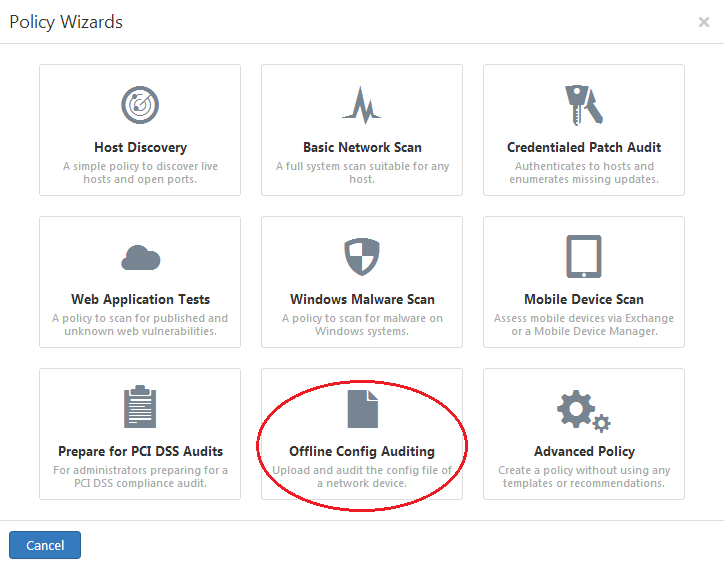
Where to Get the New Offline Configuration Audit
This new functionality is now available to Nessus users and currently supports Brocade, Cisco, FireEye, FortiGate, HP, Junos, and NetApp plugins, with more product support to come. Note that more than one configuration can be uploaded in a single policy. For example, you can upload Cisco, HP, and Junos configurations all in a single policy by uploading them to their respective sections, and you do not have to create separate policies for each device type.
For More Information
Special thanks to Mehul Revankar for his contribution to this post.
Learn more
- Plugins
- Security Frameworks
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success