Answering Your Questions about Nessus Cloud

Note: Nessus Cloud is now a part of Tenable.io Vulnerability Management. To learn more about this application and its latest capabilities, visit the Tenable.io Vulnerability Management web page.
I was fortunate to attend several Tenable User Group meetings in the Northeast a few weeks ago. One of the topics we discussed at the meetings was Nessus® Cloud – what it is, what it does, and how it works. The following questions came up several times in the meetings, so we’re sharing here in case they’re on your mind as well.
External or internal scanning?
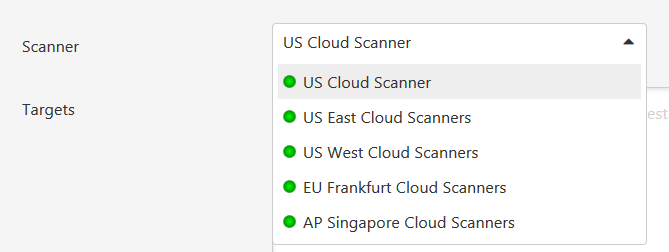
Most people we met at the User Group meetings were familiar with Nessus Cloud for doing external scans and knew that Nessus Cloud is also a PCI DSS Approved Scanning Vendor service for those organizations that need to meet PCI external scanning requirements. What was new for some people is that through the Tenable Cloud, Nessus Cloud customers have several worldwide scanners available to them. While you can select any cloud scanner to scan externally-facing assets, selecting a scanner that’s geographically close to those assets can deliver results faster.
Nessus Cloud customers have several worldwide scanners available to them
For internal scanning, we talked about two options available to Nessus Cloud customers. First, every Nessus Cloud license comes with one or more internal scanners, so customers can deploy these secondary scanners on their internal networks. It’s also possible with Nessus Cloud to deploy Nessus Agents on individual target systems. We expect that Nessus Cloud customers will use a mix of external, internal and agents to scan their environments. This Deploying Nessus Cloud video gives a good overview of the different external and internal scanning options available and when it makes sense to use one option over another.
Where does Tenable host Nessus Cloud?
We host the Tenable Cloud on Amazon Web Services (AWS)
We host the Tenable Cloud on Amazon Web Services (AWS), which offers Nessus Cloud customers many useful benefits, as our VP of cloud services, Sean Molloy outlined in this Nessus in the Cloud blog article earlier this year. For example:
- Given the sheer size of AWS, there’s no upper bound limit on growth.
- With the regional coverage of AWS, customers can select where their data is pinned.
- We’re able to implement multiple layers of security to better protect the Tenable Cloud and our customers’ data.
While scalability of the cloud is very much a given, the second two points above both sparked further discussion.
How do I keep my data in a specific region?
When we talked about AWS and its extensive regional coverage, the question of how to “pin” or designate that your data be archived in a specific region came up multiple times. It’s also one that comes up frequently from our friends in Europe, even more so since the European Court of Justice invalidated the US-EU Safe Harbor agreement back in October, making it more important than ever for organizations managing data within Europe to keep that data within EU boundaries.
For Nessus Cloud customers, it is very easy to pin data to a specific region
For Nessus Cloud customers, it is very easy to pin data to a specific region. When an account is first provisioned, a customer selects an AWS region for data storage. Current choices are:
- US / N. Virginia
- EU / Frankfurt
- APAC / Singapore
Again, specific to Europe, as all customer data is stored in secure, regional AWS services, the certifications for EU data protection that AWS maintains apply to the Tenable Cloud. More information is available from Amazon.
How is my data protected?
The protection of customers’ data in the Tenable Cloud is our top priority, so we're happy when we get the opportunity to talk about the security of our application and our customers’ data. We outline our policies in the Tenable Data Protection Practices whitepaper on our website, and our cloud services team is always available to discuss the policies in more detail. The whitepaper covers Tenable Cloud security policies from several different perspectives:
- For physical security, since the Tenable Cloud uses data centers and services from Amazon Web Services (AWS) to provide and deliver Nessus Cloud to customers, AWS is responsible for policies and controls for physical security of their data centers. They offer documentation on their practices via their website.
- For application security, the Tenable product team follows a number of best practices to ensure security of software applications they develop and deliver.
- Data security practices include encryption for data in all states in the Tenable Cloud and isolation of data so that customers cannot access data other than their own.
Those are a few highlights. Other areas include data retention, replication and disaster recovery policies that all play a role in ensuring the security of the Nessus Cloud application and customer data. Again, for more detail, download the Tenable Data Protection Practices whitepaper.
Other questions?
Do you have other questions about Nessus Cloud? If so, they might be answered in the Nessus FAQ on our website. If not, send me an email at [email protected] and I’ll answer in another blog article, update the FAQ or get back to you directly.
If you’re interested in attending an upcoming Tenable User Group meeting, talk to your local Tenable account manager or partner about upcoming events in your region.
Learn more
- Cloud
- Nessus




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success