by Josef Weiss
The proliferation of unsupported and end-of-life (EOL) products is a common security problem experienced across all organizations. As applications and operating systems reach EOL, vendors stop offering support, causing security and stability to decrease over time. This report provides organizations with a clear and simplified method to identify EOL software and enables security managers to predict where risk will increase to develop a mitigation plan.
Identifying assets running EOL applications is an important part of assessing and minimizing organizational risk since patches, updates and security fixes are longer available. The Center for Internet Security (CIS) Critical Controls (Sub-control 2.2) states that organizations must ensure that only software applications or operating systems that are currently supported and receiving vendor updates are added to the organization’s authorized software inventory. Organizations need to tag all unsupported software in the asset inventory.
Tenable Vulnerability Management enables organizations to continuously assess the health and security posture of the network, including identification and monitoring of unsupported software. Quick identification of unsupported operating systems and applications, enables risk managers to see risks associated with EOL software. Identifying exposures, provides the operations teams direction to implement, act, and prioritize remediation efforts to mitigate cyber risk. Risk managers and operations teams can communicate to the leadership team how upgrading unsupported operating systems and applications reduces their network risk.
Tenable Vulnerability Management uses active methods to identify EOL products found in the environment by examining the Microsoft registry, common software installation locations, or using applications utilities such as YUM or APT in Linux systems. Risk managers are able to verify the operation team's activities and identity areas for risk mitigation.
This report provides the organization with a clear and simplified method to identify EOL software and enables security managers to predict where risk will increase and develop a mitigation plan.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Vulnerability Management discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture. The requirements for this report are: Tenable Vulnerability Management (Nessus, NNM) and Tenable.cs.
CHAPTERS
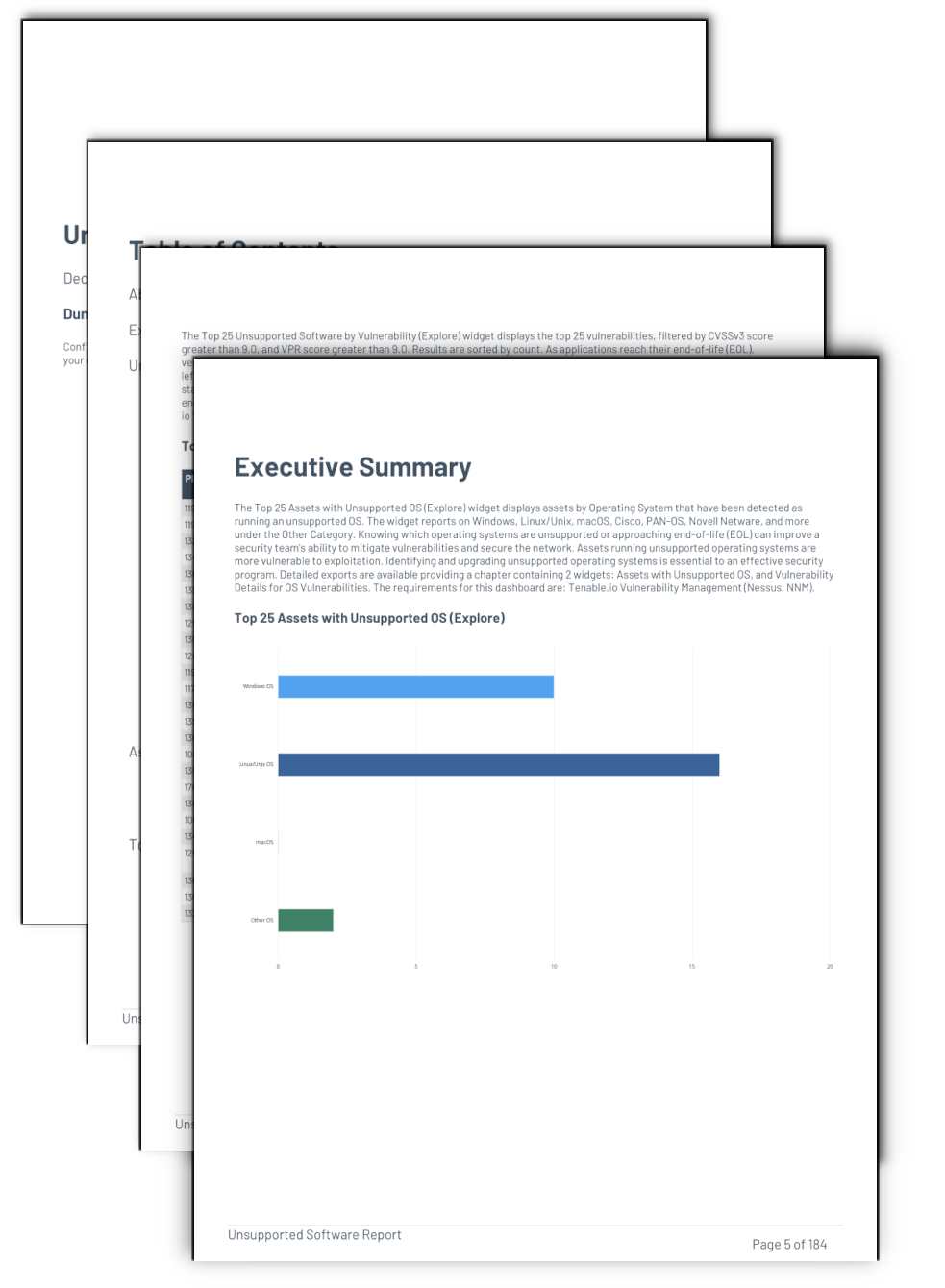
Executive Summary: This chapter offers a look at the assets that pose the greatest risk, and a look at the number of assets with unsupported applications. The chapters contains a number of elements that display assets with unsupported operatings systems, unsupported software, unsupported outliers, end of life software, and operating systems discovery. This information can be used as a starting point when identifying areas of risk by displaying the assets that require the most attention. .
Unsupported Outliers by Vulnerability: This chapter contains the Unsupported Outliers by Vulnerability table which uses plugin name wildcard filters to display information about unsupported software or protocols. Tenable.io has several plugins that report unsupported software and configurations that are unrelated to a specific software vendor and identify unsupported outliers. These identified vulnerabilities are often related to Linux/Unix, OpenSSL, and Web Services. These plugins provide the ability to group assets together based on an unsupported software or protocol. The widget is followed by an iterator that provides detailed information on the exploitable vulnerability, starting with the number of hosts that have been identified as vulnerable. Details on the exploitable vulnerability are shown in a Vulnerability Details table, which provides information on remediation steps (Solution) as well as detailed reference data. The Vulnerability Details table is followed by a Host Details table that contains information about each vulnerable asset. The requirements for this chapter are: Tenable Vulnerability Management (Nessus, NNM).
Top 25 Assets with Unsupported OS: This chapter contains the Unsupported Operating System ring chart, leveraging the Host Analysis API to group on Plugin Name. The ring chart displays Operating Systems that have been detected as being unsupported and their respective percentages. The widget reports on Windows, Linux/Unix, macOS, Cisco, PAN-OS, Novell Netware, and more. Details on the unsupported OS are shown in a Vulnerability Details table, which provides detailed reference data and plugin output. The Vulnerability Details table is followed by a Host Details table that contains information about each vulnerable asset. Assets running unsupported operating systems increase organizational risk since patches, updates and security fixes are longer available from the vendor, causing security and stability to decrease over time. Identifying and upgrading unsupported operating systems is essential to an effective security program. The requirements for this chapter are: Tenable Vulnerability Management (Nessus, NNM).
Top 25 Unsupported Software by Vulnerability: This chapter contains the Top 25 Unsupported Findings table, presenting a list of the top most vulnerable assets at risk for exploitation. Information is filtered by vulnerabilities with a CVSSv3 Score of 9 or higher that are unsupported, and is sorted by total vulnerabilities. As applications and operating systems reach end-of-life, vendors stop offering support, causing security and stability to decrease over time. Identifying unsupported applications is critical to minimize organizational risk. The widget is followed by an iterator that provides detailed information on the vulnerability, starting with the number of hosts that have been identified as vulnerable. Details on the vulnerability are shown in a Vulnerability Details table, which provides information on remediation steps (Solution) as well as detailed reference data. The Vulnerability Details table is followed by a Host Details table that contains information about each vulnerable asset. The requirements for this chapter are: Tenable Vulnerability Management (Nessus, NNM).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success