by Ryan Seguin
The Cyber Exposure gap is often widened by the amount of time invested in identifying risk. Security personnel spend disproportionate time evaluating assessed threats in comparison to the hours spent mitigating that threat. This report serves to reduce effort, and assist in narrowing the gap between risk and mitigation.
As the elastic attack surface expands and contracts, asset malware protection changes too. This report’s strategic focus is to add context to asset exposure to prioritize remediation, and to select appropriate remediation techniques. These strategies are achieved through malware identification and prevention.
Analysts and administrators will be able to use this report to quickly assess their business’ current malware state. With easy to understand data points, any organization will be able to maximize the understanding of their digital landscape’s health. With that understanding, direct action can be taken and a leap forward can be made to ensure that the Cyber Exposure gap is reduced.
Cyber Exposure will help analysts drive a new level of dialogue with the business. By knowing which areas of the business are secure or exposed, analysts can effectively measure the organization's Cyber Risk. Analysts can use the metrics provided by Tenable.io to determine how much and where to invest to reduce risk to an acceptable amount and help drive strategic business decisions. Tenable.io is the first Cyber Exposure solution and provides key risk metrics that organizations need to measure risk exposure.
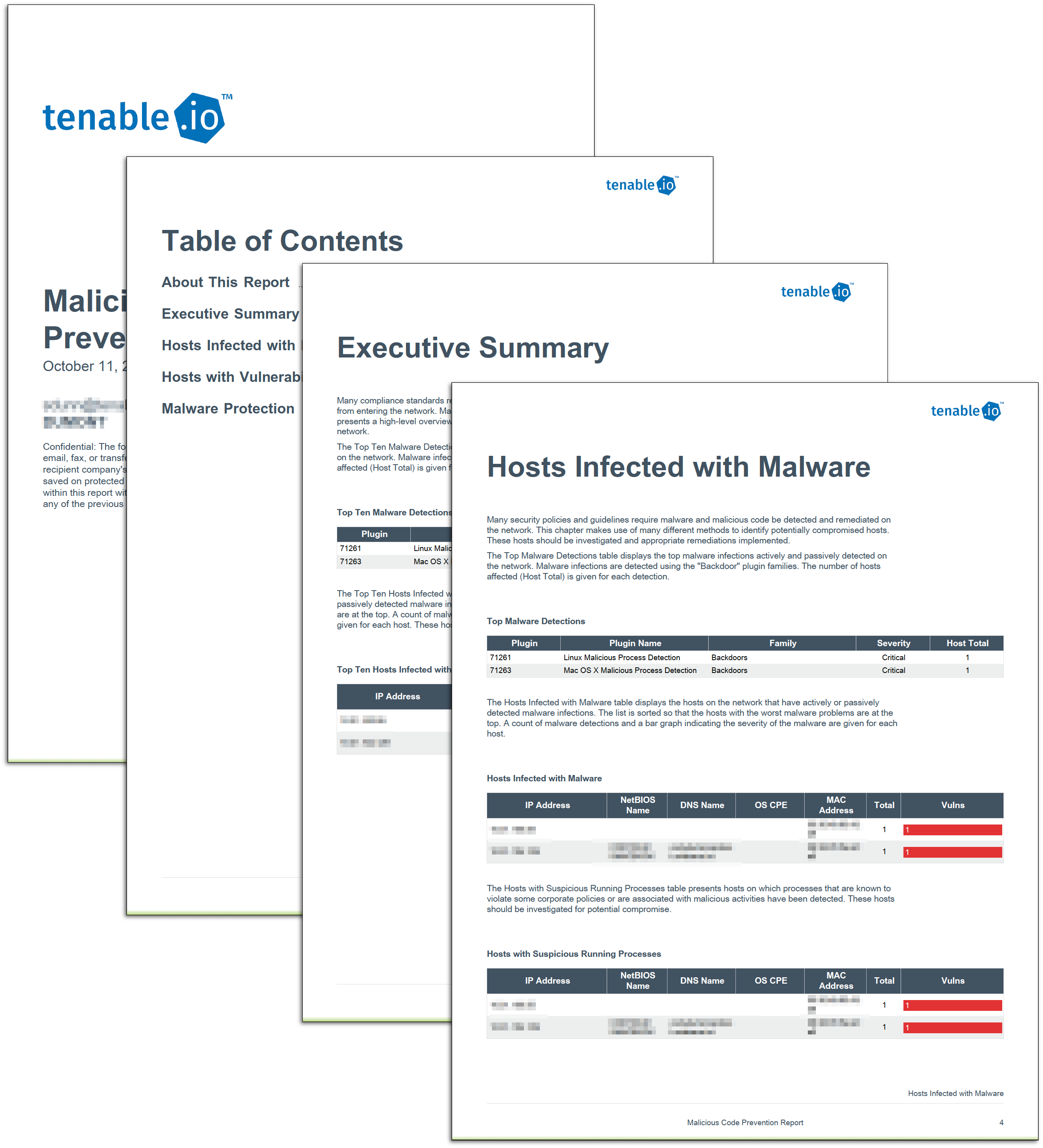
Executive Summary
This chapter presents a high-level overview of potential malware on the network and the malware protection status of the network. Vulnerabilities are listed here by plugin ID for quick asset association and assessment. The summary serves to give a top level health check and asset status.
Hosts Infected with Malware
This chapter makes use of many different methods to identify potentially compromised hosts. Immediate action items should be made to address assets presented in this chapter. Assets found in this chapter are likely an active threat to an organization.
Hosts with Vulnerabilities that Can Be Exploited
This chapter presents information on exploitable vulnerabilities, which will help direct protection efforts. While these vulnerabilities do not indicate the presence of malware, these vulnerabilities should be acted upon to prevent malware injection. Creating tasks to remediate vulnerabilities found on these assets strengthens an organization’s ability to protect assets from future attack.
Malware Protection
This element detects whether antivirus software is installed and running on an asset and whether the antivirus engine and virus definitions are up to date. Assets should always be as up to date as possible so that antivirus solutions can perform correctly. For an organization that has an active antivirus update plan, this chapter will also assist with identifying potential weaknesses in current update operations.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success