by Josef Weiss
The Windows Software Summary report identifies installed software across actively scanned Windows hosts. Utilizing plugin 20811, Microsoft Windows Installed Software Enumeration (credentialed check), Nessus can possibly enumerate installed software on selected hosts. With this report, administrators will have better control over software inventory and device configurations.
Applications are critical to an organization’s end-users’ ability to perform their daily tasks. Ultimately, an organization may have a wide variety of applications installed across many departments. While installing applications may be easy, keeping track of them can be a difficult task.
Auditing installed applications on a regular basis is important. Many times, software is installed to serve a particular purpose and is later forgotten. These dormant, un-patched applications may, over time, become vulnerable to security flaws. End users may have the permissions to install software locally without prior approval, which can lead to the potential threat of unauthorized software, critical unknown vulnerabilities, and legal liabilities.
Organizations should have a method in place to track software inventory. Knowing the software that’s installed is a key element in software inventory control. Additionally, administrators will find it easier to locate, update, patch, and/or remove unauthorized software.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Discovery & Detection. The report requirements are:
- SecurityCenter 4.8.2
- Nessus 6.4.3
Tenable's SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring platform. SecurityCenter CV provides vulnerability identification, risk reduction, and compliance monitoring. SecurityCenter CV is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, SecurityCenter CV provides the most comprehensive view of vulnerability data.
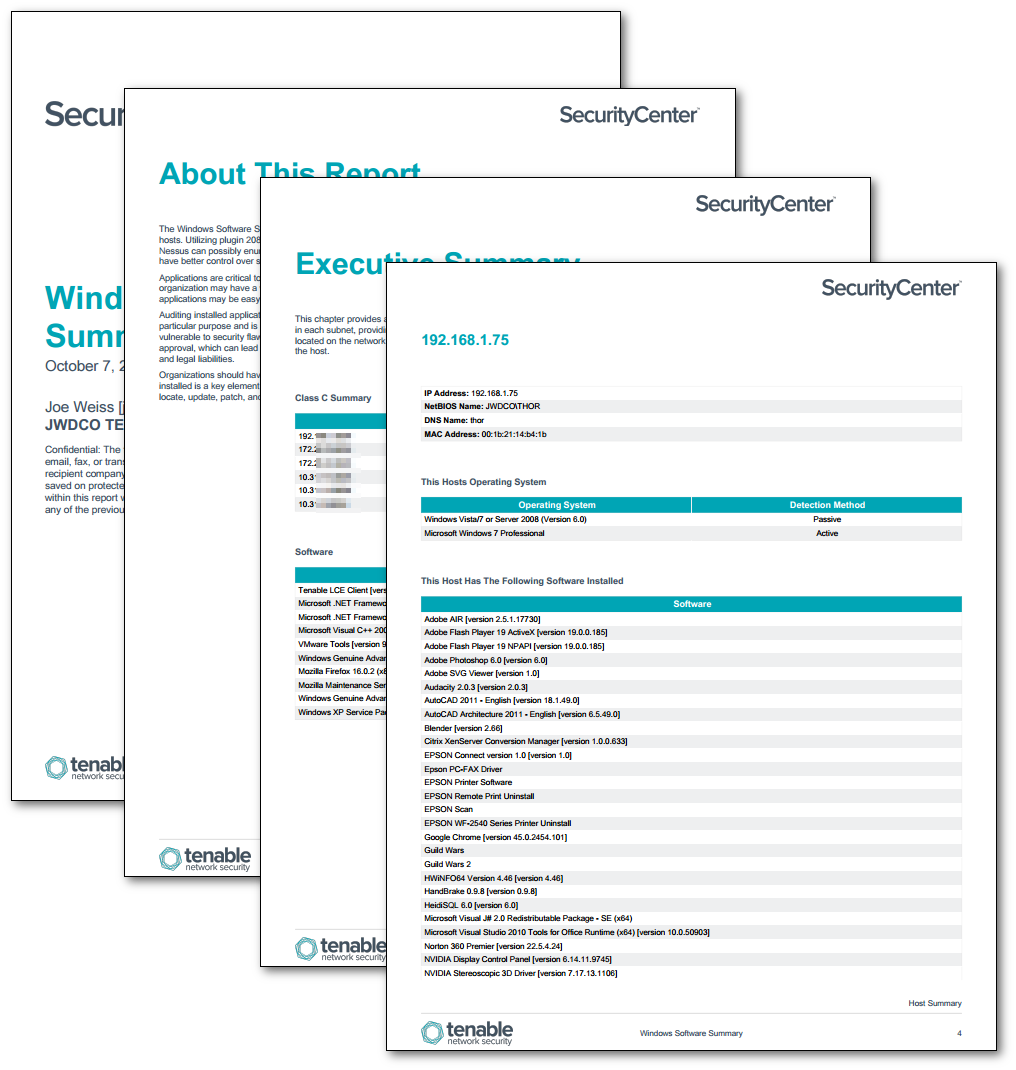
This report is comprised of a Table of Contents for each identified host. The Identified Hosts Table lists the hosts by IP address, NetBIOS Name, and DNS Name, and is followed by a detailed look at each host individually.
The report contains the following chapters:
- About This Report - This chapter provides a description of Software Summary Report.
- Executive Summary - This chapter provides an overview of the Class C address space and the number of Windows hosts scanned in each subnet, providing a visual representation of where the hosts that are being scanned are physically located on the network. In addition, a table is provided that lists the software packages that are installed on the host.
- Host Summary - This chapter provides some host details in a header with IP Address, DNS Name, NetBIOS Name, and Last Scan Date, and is followed by the host Operating System and a list of installed software, and version (if available).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success