by Josef Weiss
Operational requirements often limit the ability to continuously scan devices, or to ensure 100% coverage of active scanning, therefore passive scanning allows organizations to continuously detect vulnerabilities, devices, services, and attacks. Passive monitoring provides a wealth of information, and providing a high-level overview or summarizing the information can be a time consuming task. Information contained in this executive report summarizes this large amount of passive data, providing an overview of passively detected vulnerabilities within the organization.
Tenable Nessus Network Monitor (NNM) provides deep packet inspection to continuously discover and track applications and vulnerabilities, eliminating network blind spots. Areas of importance where passive detection are most effective are detection of new devices, detecting new services, network traffic, and monitoring for vulnerabilities, while active scanning is not taking place. This report presents a comprehensive summary of passively detected vulnerabilities on the network. Summarized information will help executives and management review concerns quickly, without trudging through all the details. Indications within this summary report provide an overview to quickly alert the viewer on potentially unauthorized services in use, misconfigurations, or vulnerabilities on critical systems.
Using this report, organizations will be able to summarize large volumes of real-time information quickly, assisting with prioritizing and reducing overall security risks within the enterprise. In addition, there are four detailed NNM Detections reports covering exploitable vulnerabilities, devices and services, vulnerabilities and attacks, and network traffic. These additional reports can be utilized in conjunction with this NNM Detections Executive report. The additional reports provide a more comprehensive and detailed outlook of the organization’s passive vulnerabilities. The reports can be found at the following links:
NNM Detections - Vulnerabilities and Attacks
NNM Detections - Devices and Services
NNM Detections - Traffic
NNM Detections - Top 50 Exploitable Vulnerabilities
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Executive
The report requirements are:
- Tenable.sc 5.3.2
- PVS 5.0.0
Tenable automatically analyzes information from active scanning, intelligent connectors, agent scanning, passive listening, and host data in order to provide continuous visibility and critical context. Active scanning periodically examines hosts within the organization to determine risk. Intelligent connectors leverage other security investments to provide additional context and analysis. Agent scanning enables assessing systems without the need for ongoing host credentials. Passive listening detects hosts that were offline during active scans, and provides real-time monitoring of host activity throughout the network. Host data is analyzed to correlate real-time events, monitor firewall traffic, and identify malicious attacks. The combination of these sensors provides organizations with the tools they need to proactively detect, monitor, and respond to threats within the enterprise.
The following chapters are included in this report:
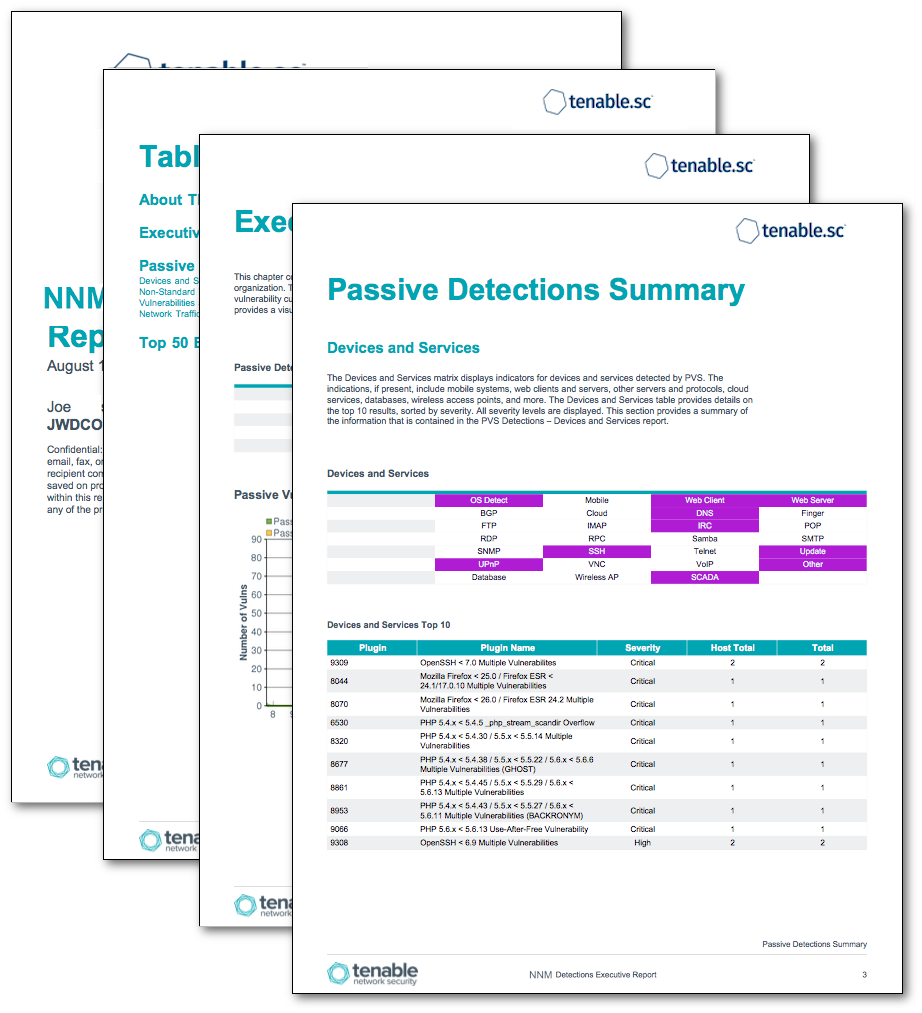
- Executive Summary - This chapter contains two elements, which provide an overall summary of passive detections within the organization. The Passive Detections matrix displays, by family, an indication for every passively detected vulnerability currently being identified by NNM. The Passive Vulnerability Trend provides an overview of passive vulnerabilities over the last 25 days for all severity levels.
- Passive Detections Summary - This chapter presents a summary of the full NNM Detections reports. Each section of this chapter is named after and summarizes a full report. Matrices and tables display indicators for vulnerabilities detected by NNM. The table provides details on the Top 10 results, sorted by severity. All severity levels are displayed.
- Top 50 Exploitable Vulnerabilities - This chapter presents the top 50 exploitable vulnerabilities passively detected by NNM. The most critical vulnerabilities are listed first. An initial table of the top 50 is shown, followed by details on the top 10 most vulnerable hosts, based on the exploitable vulnerabilities passively detected by NNM. The table is sorted so the most vulnerable host is listed first. Host details and a bar graph of vulnerabilities are shown for each host.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success