Common user interfaces in a modern workplace involve some type of web interface. Web interfaces allow more diverse sets of users to connect to an application through common web browsers. Allowing users to connect to web-enabled user interfaces typically reduces IT requirements, enabling the user to work more efficiently.
Enabling a web-based user interface may require more IT requirements for security, but those requirements may not be enabled by default. When a connection is made to a website, the response from the website back to the source usually contains some type of information. The response back to the source could contain a POST response with a few HTTP headers, or a POST response with excessive HTTP headers.
Depending on the web platform, a POST response could contain excessive HTTP headers and all of the other HTTP options a user can perform. In a typical website “transaction”, a typical experience contains HTTP GET and POST. However, other options can be “DELETE” or “MOVE”, which could provide attackers a way to circumvent security controls. Security controls such as packet-layer firewalls and web application firewalls can block non-typical HTTP options to help minimize the risk to the environment. Removing or denying those HTTP options with a configuration management program can also reduce the risk to the web platform.
While threats such as unprotected HTTP options exist in web platforms, inadvertent information disclosures are commonly returned in responses. HTTP response headers such as “Server”, and X-Headers such as “X-Powered-By” and “X-AspNet-Version”, provide attackers detailed web platform information. If an attacker can send a basic GET request to a web platform, they could receive detailed information for the web platform, reducing their time for reconnaissance.
With detailed information provided in the HTTP response, an attacker can better tailor attacks and exploitation strategies. The strategies can better match the specific versions of software running on the web platform. Organizations may have differing views of the value of HTTP response headers in the environment. However, if analysts are aware of the headers in the environment, removing or being aware of the headers may help to reduce risk in the environment.
In addition to HTTP options and response headers, this report provides analysts with a view of the certificates used on web platforms. Analysts can see certificates that have expired, will expire soon, and will in the future become valid certificates. Using this information, analysts can work with the various teams in the organization to reduce potential certificate issues along with ensuring best practice certificate usage.
Following the information in the chapters above, a list of web platforms in use in the organization is provided. This list can help assist analysts to ensure that authorized web platforms are in use and raise awareness of unknown or unexpected web platforms. The remaining chapter of the report provides details of medium, high and critical severity vulnerabilities found with web servers in the organization.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.6.0
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Tenable's family of products includes Tenable.sc Continuous View (CV), Nessus, Nessus Network Monitor (NNM), and Log Correlation Engine (LCE). Tenable.sc CV provides the most comprehensive and integrated view of network health, and is the global standard in detecting and assessing network data.
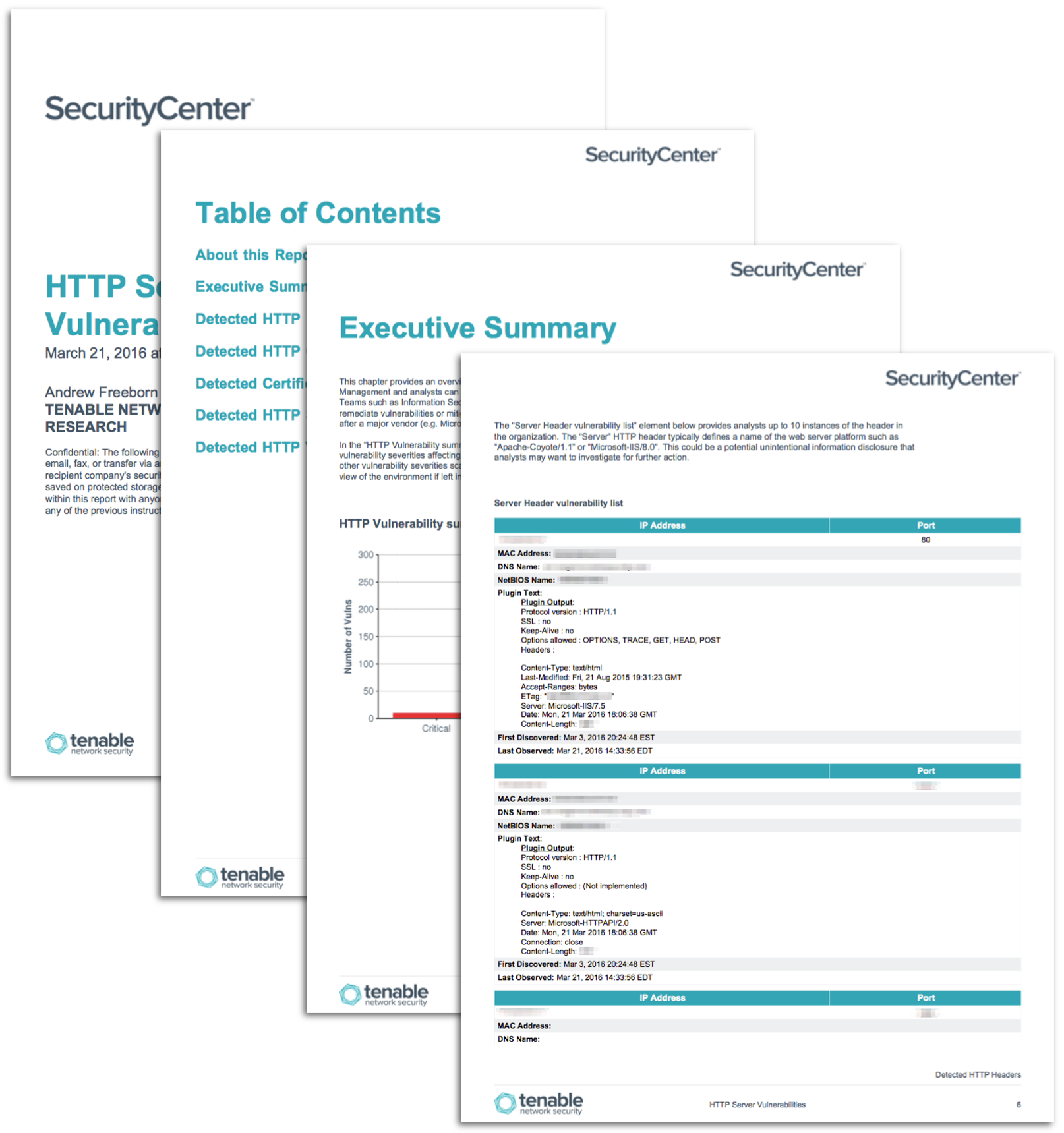
This report contains the following chapters:
- Executive Summary: This chapter provides an overview of HTTP-related vulnerabilities and ports in the organization. Management and analysts can quickly see the counts of vulnerability severities affecting web platforms. Teams such as Information Security, Development, QA and others can review this report together to help remediate vulnerabilities or mitigate risk found in this report.
- Detected HTTP headers: This chapter provides an overview of various HTTP headers detected in the organization. An important note to make is that not all HTTP headers in an environment are called out specifically in this chapter. Common HTTP headers are called out which organizations may want to consider removing or be aware of the potential risk. There are no vulnerabilities specifically associated with the HTTP headers, but they may present unintentional or intentional information disclosures.
- Detected HTTP options: This chapter provides an overview of various HTTP options detected in the organization. The HTTP options shown in this chapter may have a unique and defined purpose in the organization. However, some web platforms may by default enable excessive HTTP options not necessary for the web application to perform. The HTTP options, along with the web platform, could potentially open unintentional security gaps an attacker could exploit. Analysts should review the HTTP options along with the context of the web platform. Analysts can then ensure that proper usage is allowed per organizational requirements and proper security controls are in place.
- Detected Certificate Information: This chapter provides an overview of certificate issues detected in the organization. Certificate issues could cause unique problems in the environment without proper management and rotation. Analysts can be aware of certificates in different states of validity to help ensure appropriate and secure communication in the organization.
- Detected HTTP Server Types: This chapter identifies the various versions of web platforms detected in the organization. Analysts can use this information to determine if the web platforms deployed meet organizational requirements and authority. Knowing this information can assist analysts to reduce shadow IT along with unexpected or unauthorized web platforms.
- Detected HTTP Vulnerability Details: This chapter identifies web server vulnerabilities with a medium, high or critical severity. Analysts can gain proactive insight into the organization with vulnerabilities affecting web servers. Concise information for every vulnerability is provided, enabling the analyst to further research the issue to best address each vulnerability.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success