by Josef Weiss
The proliferation of unsupported and end-of-life (EOL) products is a common security problem experienced across all organizations. As applications and operating systems reach EOL, vendors stop offering support, causing security and stability to decrease over time. This dashboard provides organizations with a clear and simplified method to identify EOL software and enables security managers to predict where risk will increase to develop a mitigation plan.
Identifying assets running EOL applications is an important part of assessing and minimizing organizational risk since patches, updates and security fixes are longer available. Many industries have regulatory requirements (e.g., GDPR, HIPPA, PCI-DSS,) that mandate up-to-date software. In addition, the Center for Internet Security (CIS) states that organizations must ensure that only software applications or operating systems that are currently supported and receiving vendor updates are added to the organization’s authorized software inventory.
Tenable Security Center enables organizations to continuously assess the health and security posture of the network, including identification and monitoring of unsupported software. Quick identification of unsupported operating systems and applications, enables risk managers to see risks associated with EOL software. Identifying exposures, provides the operations teams direction to implement, act, and prioritize remediation efforts to mitigate cyber risk. Risk managers and operations teams can communicate to the leadership team how upgrading unsupported operating systems and applications reduces their network risk.
Tenable Security Center uses active methods to identify EOL products found in the environment by examining the Microsoft registry, common software installation locations, or using applications utilities such as YUM or APT in Linux systems. Risk managers are able to verify the operation team's activities and identity areas for risk mitigation.
This dashboard provides the organization with a clear and simplified method to identify EOL software and enables security managers to predict where risk will increase and develop a mitigation plan.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Security Center discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture. The requirements for this dashboard are: The requirements for this dashboard are: Tenable Security Center (Nessus, NNM).
Components
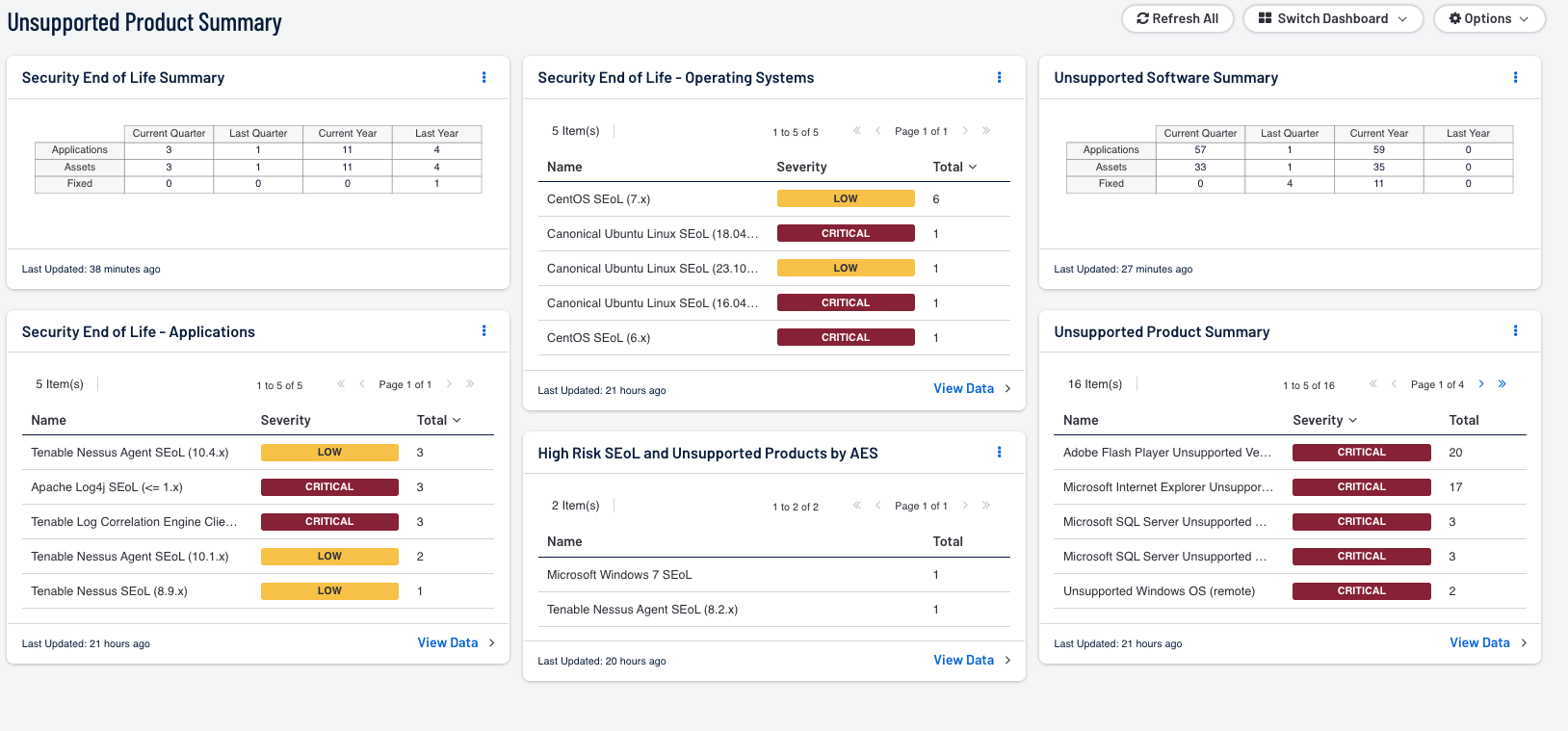
- Security End of Life - By SEoL Date Range - The Security End of Life Summary matrix displays the count of applications that are no longer supported by vendors, assets with unsupported applications, and mitigated assurances of the unsupported applications over different time periods.
- Security End of Life - Operating Systems - The Security End of Life - Operating Systems table displays all SEoL operating systems, associated severity, sorted by count.
- Unsupported Software Summary - By Last Observed Date Range - The Unsupported Software Summary matrix displays the count of applications that are no longer supported by vendors, assets with unsupported applications, and mitigated assurances of the unsupported applications over different time periods.
- Security End of Life - Applications - The Security End of Life - Applications table displays all SEoL applications, associated severity, and is sorted by count.
- Unsupported Product Summary - Unsupported Products by AES - The High Risk SEoL and Unsupported Products by AES table displays products that are either SEoL or Unsupported, and have a very high AES Score.
- Unsupported Product Summary - Unspported Applications - The Unsupported Product Summary table displays all unsupported applications by name, sorted by count.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success