by Josef Weiss
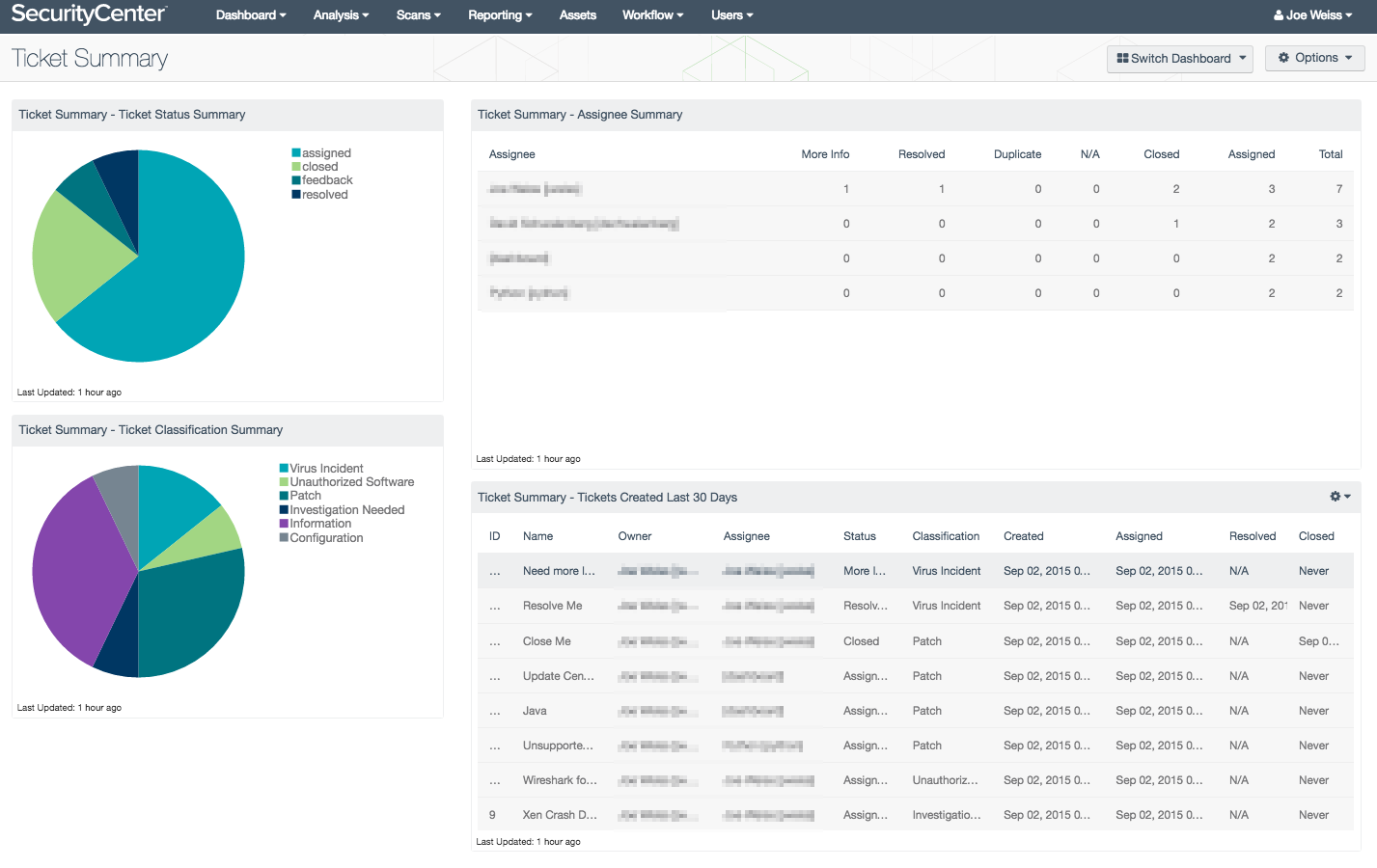
The Tenable SecurityCenter Workflow section features many options for alerting, ticketing, and managing risk rules. Workflow ticketing allows organizations to prioritize workflows based on customer specific triggers and requirements, track incident response, streamline processes, and increase productivity. The Ticket Summary dashboard displays the current status of tickets by classification, assignee, and ticket, allowing organizations to prioritize workflow and facilitate better use of security operational resources by prioritizing vulnerable systems.
In addition to viewing vulnerability information through dashboards, reports, and ARCs, SecurityCenter supports tracking progress via ticketing assignments to perform specific assignments. Tasks such as email alerts, ticket creation and assignment, and the assignment of responsibility for vulnerability resolution can be easily created and monitored in SecurityCenter. Many actions can be assigned per ticket. Tickets may also contain snapshot options, allowing the user to view a vulnerability snapshot displaying the query that was used during ticket creation.
Workflow and ticketing functions allow users to be notified of, and properly handle vulnerabilities and events as they are identified. Tickets can be created both manually, while viewing vulnerabilities or events through analysis tools, and automatically by a predefined set of conditions via alerting functions. For additional information on Tenable’s Workflow please consult this document. This dashboard provides components, which provide details by assignee, on tickets that have been created, assigned, and closed. Summary information displaying ticket classification, and tickets created within the last seven days are also provided.
The Tenable SecurityCenter integrated ticket system simplifies IT workflow. Overhead can be eliminated by automatically creating tickets after vulnerability scanning, decreasing time to initiate mitigation. Organizations can easily streamline processes by customizing specific triggers and requirements. This dashboard and its components assist in prioritizing workflow, track incident response, and provide details on workload and resolution.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Executive. The dashboard requirements are:
- SecurityCenter 5.4
- Nessus 6.7
- PVS 5.1
Tenable SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, and security monitoring. SecurityCenter is continuously updated with information about advanced threats and zero day vulnerabilities, and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, enabling decisive action that transforms your security program from reactive to proactive. Active scanning examines the devices on the systems, running processes and services, detection of vulnerable software development applications, configuration settings, and additional vulnerabilities. With this information, analysts have greater insight to determine if supported software and systems are operating within the organization. Continually scanning the network with passive sensors for servers, desktops, and applications helps prioritize security efforts to mitigate threats and weaknesses. Organizations continue to operate with more mobile and transient network devices and need to have a system in place that continuously monitors traffic, devices, applications, and communications across environments. Tenable enables powerful, yet non-disruptive, continuous monitoring of the organization to ensure vulnerabilities are available to analysts. The SecurityCenter Workflow section features many options for alerting, ticketing, and managing risk rules to enhance this functionality.
This dashboard contains the following components:
- Ticket Summary - Ticket Status Summary - This chart provides and overall status summary of tickets created, closed, resolved, or that require additional feedback.
- Ticket Summary - Ticket Classification Summary - This chart displays a classification summary of tickets created. Ticket classification can be selected from a drop-down list containing such items as Information, Configuration, Patch, Disable, False Positive, and many others.
- Ticket Summary - Assignee Summary - This chart displays an assignee summary table containing the current statistics for each user with ticket entries. The number of tickets that are assigned, require additional information, have been closed, or resolved are displayed with the users name. Note: Tickets that have been assigned to a user that is subsequently deleted or removed from the system will be automatically reassigned to the owner.
- Ticket Summary - Tickets Created Last Thirty Days - This table displays tickets created over the previous thirty days with more detail, including name, assignee, status, classification, and modified date/time.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success